Getting started with Network Policy Server
Network Policy Server (NPS) is the Microsoft implementation of a Remote Authentication Dial-in User Service (RADIUS) server and proxy. A RADIUS server provides authentication, authorization, and accounting (AAA) services. NPS has many great features.
In this article, we will mainly focus on AAA services as well as RADIUS packet types in Wireshark and communication between a RADIUS client and a RADIUS server. Since, it is a huge topic, I will break it into 3 parts to explain it with examples better.
Authentication
Authentication service is used to confirm a user identity. When the user attempts to access a network or another resource, Network Access Server (NAS) creates an “Access-Request” packet and sends it to the RADIUS server, asking if that user’s credentials are valid or not. Following shows a truncated “Access-Request” packet in Wireshark.
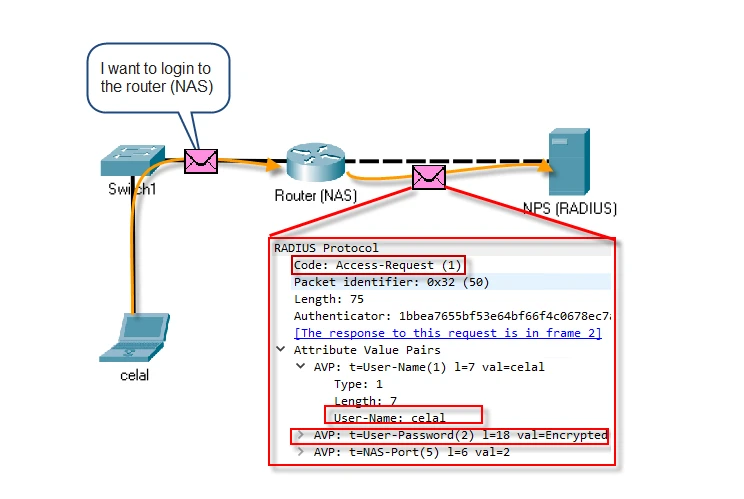
The RADIUS server may return one of these responses to the RADIUS client:
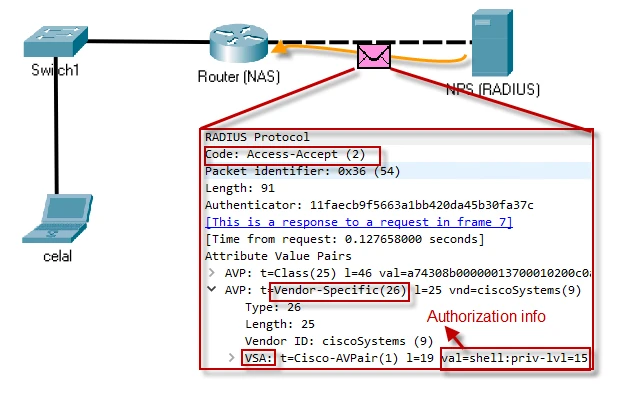
“Access-Accept”: Once the user gets authenticated which means the credentials are valid, the RADIUS server sends an “Access-Accept” packet to inform the NAS to grant access to the client. The response packet may also contain authorization information in the attributes. Following Wireshark packet shows a truncated “Access-Accept” packet with authorization information in the vendor specific attribute.
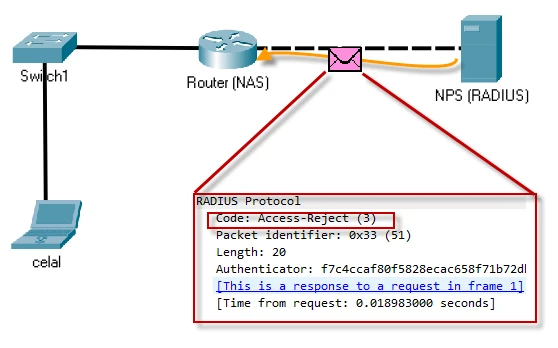
“Access-Reject”: When the authentication fails, the RADIUS server denies access to all requested network resources by sending an “Access-Reject”. Following shows a truncated “Access-Reject” packet in Wireshark.
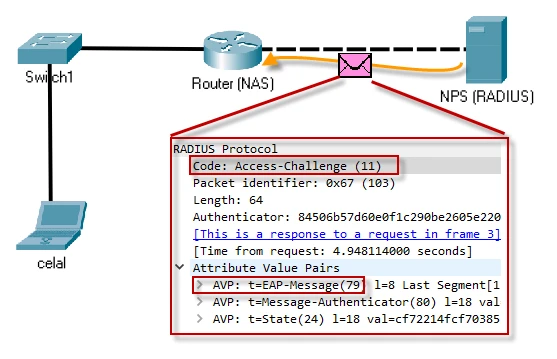
“Access-Challenge”: The RADIUS server may need the client to send extra information like secondary password, PIN, token, or card. It sends an “Access-Challenge” packet with these parameters. The packet is also sent when the RADIUS server desires to use a complex authentication mechanism like Extensible Authentication Protocol (EAP), which has man flavors such as:
- PEAP (Protected EAP)
- TLS (Transport Layer Security)
- TTLS (Tunneled TLS)
Following shows a truncated “Access-Challenge” packet in Wireshark.
Authorization
Authorization service is used to decide if a user has right to reach a service, based on user’s identity. Authorization is coupled with authentication service. The user must be successfully authenticated before the RADIUS server sends authorization information to the NAS. When the RADIUS server sends an “Access-Accept” packet to tell the NAS to let the client use the resources, it also includes authorization information in the RADIUS attributes. Once the NAS receives the packet, it grants access and privilege level which depends on the authorization information in the attributes.
Accounting
Accounting service is used to track user’s activity like how long the user was connected to the network, when the user joined the network, when the user disconnected from the network, how much resources (time, packets, bytes, and so on) the user consumed etc. This service is completely independent from Authentication and Authorization services. In short, it logs the user activity.
Implementing a AAA scenario
AAA services can be used to provide centralized infrastructure for reaching resources. Imagine that you have two network administration group, Network Admins and Network Operators who manage your network with different level of access privileges.
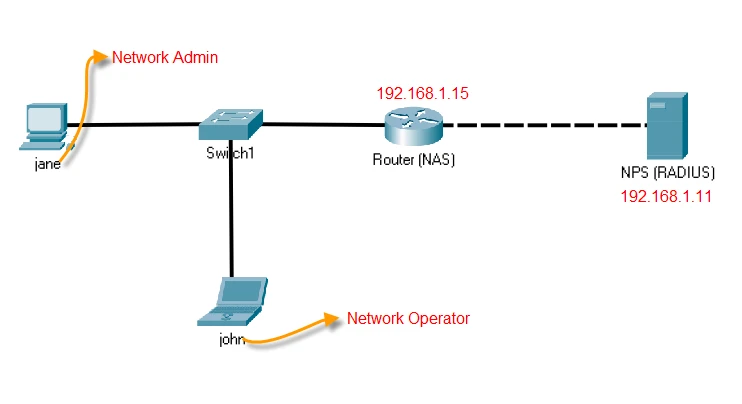
We will implement this scenario, using a Cisco router as a Network Access Server (NAS) and NPS as a RADIUS server that provides AAA services.
Step-1: Configure authentication on the router (NAS)
Enable aaa service globally.
!
aaa new-model
!
Define a RADIUS server with parameters like shared secret (key), IP address of the RADIUS server and ports for authentication and accounting.
!
radius server NPS
address ipv4 192.168.1.11 auth-port 1645 acct-port 1646
key celaldogan
!
Define a radius server group and associate previously defined RADIUS server name with the group.
!
aaa group server radius Radius_Servers
server name NPS
!
Define an authentication list which authenticates user against the RADIUS server and when the NAS fails to reach the RADIUS server, then it will use local database as backup source to authenticate the user.
!
aaa authentication login VTY_auth_list group Radius_Servers local
!
Associate the authentication list with Virtual Teletype (VTY) and finish the authentication configuration.
!
line vty 0 4
login authentication VTY_authentication_list
!
Although we have not configured the RADIUS server, I would like to show you a RADIUS “Access-Request” packet using Wireshark. I will login the router with “jane” user and password. The NAS will try to reach the RADIUS server but after couple of attempts, it will give up and use local database as authentication source.
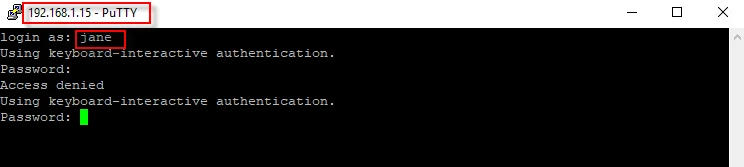
After trying to log in with jane’s credentials, let’s take a look in the packet level. Following is the “Access-Request” packet the NAS sent.
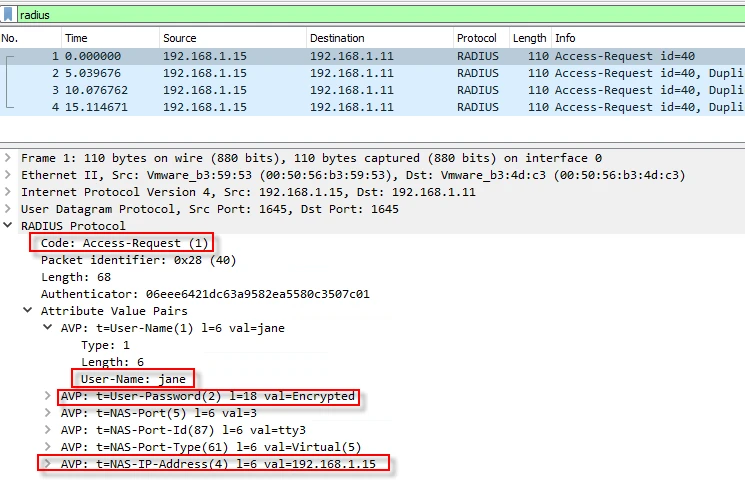
The NAS (router) creates an “Access-Request” packet with couple of attributes. In another saying, the router says “Hey RADIUS server, here is my credentials with some extra information like NAS-IP-Address (the routers IP), NAS-Port, NAS-Port-Id and NAS-Port-Type”. These are the default attributes sent in an “Access-Request” packet for Cisco’s routers and we can add some more attributes. For testing purpose, I will add one more attribute (Service-Type) with the command below.
!
radius-server attribute 6 on-for-login-auth
!
After applying the command, I logged in again. This time, the router added “Service-Type” attribute with value of “Login”. These kinds of attributes carry extra information from the RADIUS client (NAS) to the RADIUS server or vice versa. We can use this piece of information to create a filter (condition) on the RADIUS server. Following figure shows the details of the new “Access-Request” packet.
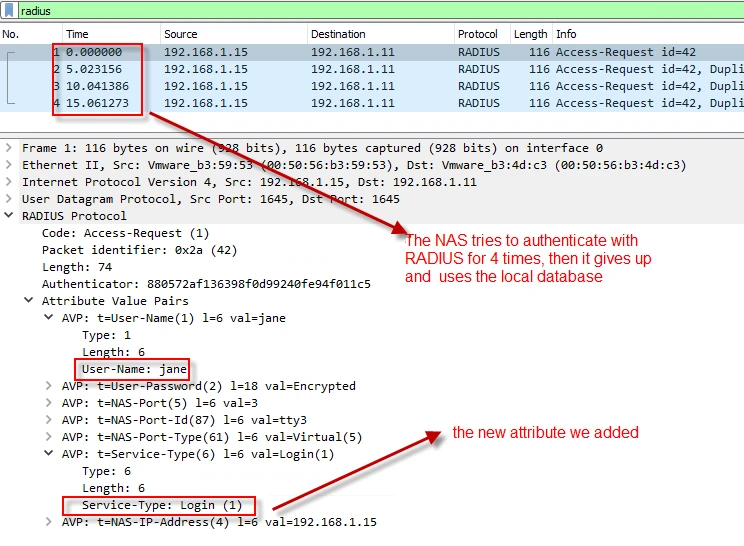
At this point, we are familiar with RADIUS “Access-Request” and attributes, so we can proceed further.
Step-2: Configure authorization on the router (NAS)
We will add the configuration below to complete authorization in this step.
Define a list for authorization. In case the NAS will not be able to reach the RADIUS server, the local database will be used.
!
aaa authorization exec VTY_author_list group Radius_Servers local
!
Associate the lists with VTY.
!
line vty 0 4
authorization exec VTY_author_list
!
Step-3: Configure accounting on the router (NAS)
We will add the configuration below to complete accounting in this step.
Define a list for accounting.
!
aaa accounting exec VTY_account_list start-stop group Radius_Servers
!
Associate the lists with VTY.
!
line vty 0 4
accounting exec VTY_account_list
!
All configuration on the NAS has finished. It is time to install NPS.
Network Policy Server (NPS) Installation
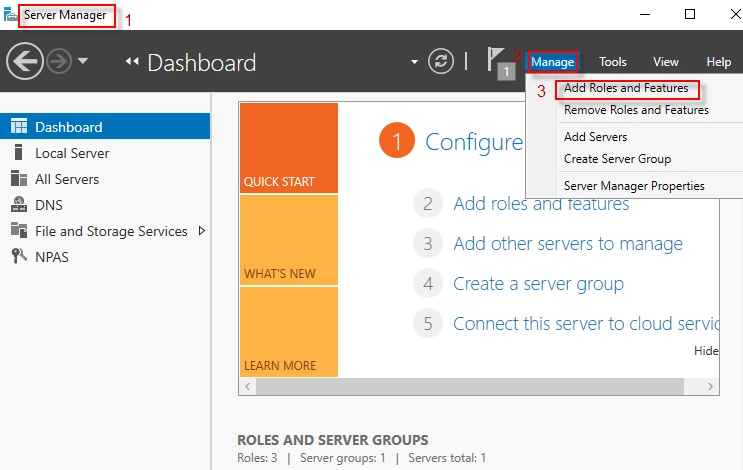
Step-1: Open Sever Manager Dashboard and navigate to Manage → Add Roles and Features
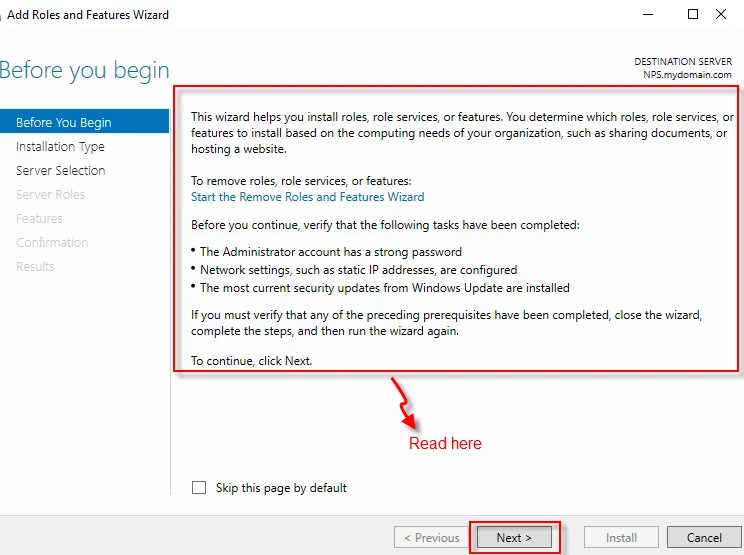
Step-2: After reading the wizard, click on “Next” button.
**
**
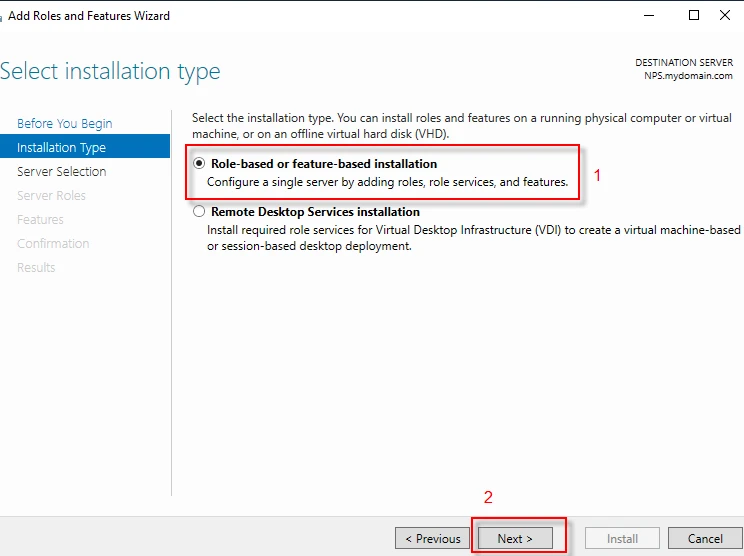
Step-3: Select “Role-based or feature-based installation” and click on “Next” button.
**
**
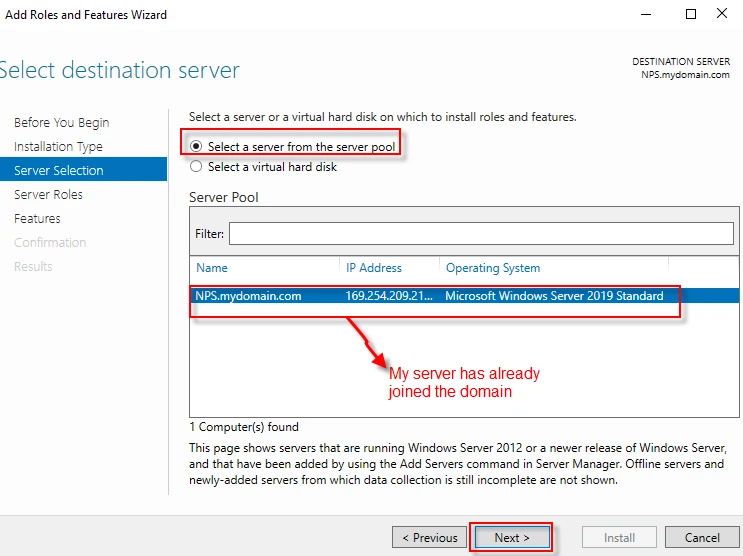
Step-4: Select a server from the server pool. Click “Next”. As you can see below, my server -NPS- has already joined the domain (mydomain.com).
**
**
Step-5: Select “Network Policy and Access Services” from “Roles” list. A window appears, follow the steps in the screenshot below and click “Next” to proceed.
**
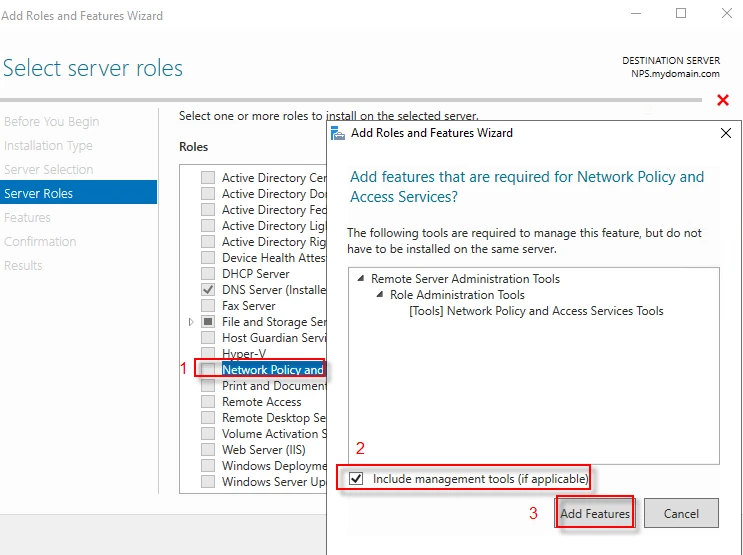
**
Step-6: Do not change anything, click “Next” to proceed.
**
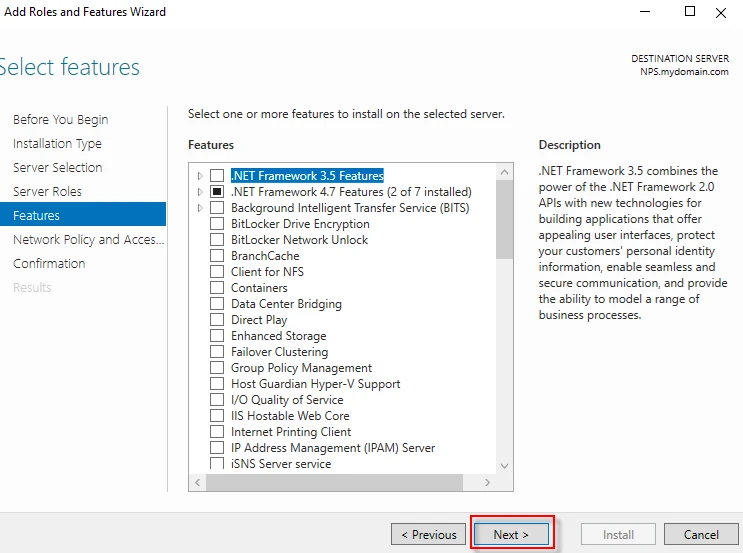
**
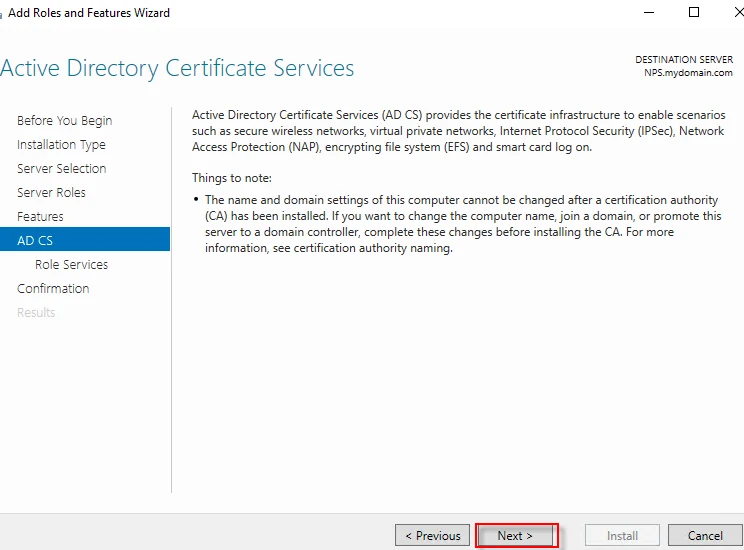
Step-7: Click “Next”.
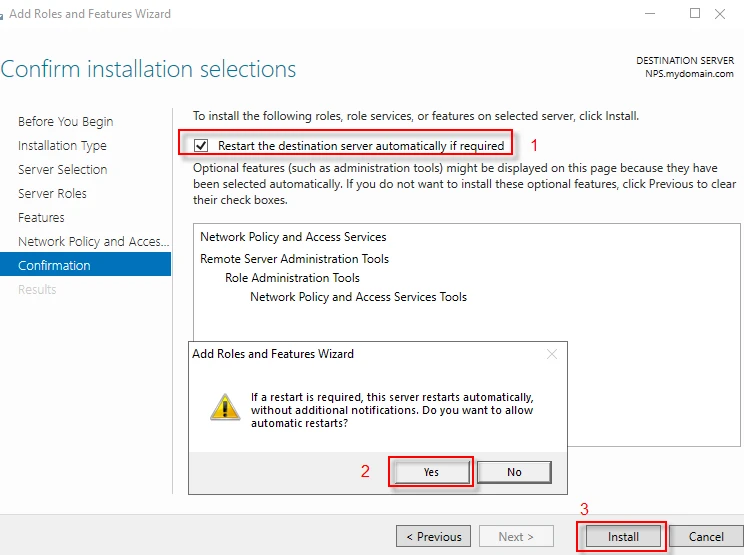
Step-8: Complete the installation with the following step.
Final thoughts
For sake of easy understanding, I will cut it here and keep the article short. In the next part, we will configure NPS server and test both the RADIUS server (NPS) and the NAS (router).




![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)


![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![How to use SFTP with IPv6 Address in Linux? [SOLVED]](/use-sftp-with-ipv6-address-in-linux/sftp-with-ipv6-address_hu_b3a4e89051cc85c6.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)