Azure Active Directory - Introduction
The ability to ensure safe and secure authentication to infrastructure resources is a quintessential organizational need in world where security breaches have become all too common.
In this article, we will explore and understand Azure’s identity and access services offering Azure Active Directory. We will first discuss some Identity and Access Management (IAM) basics to lay the foundation for conceptualizing and understanding Azure Active Directory.
Identity and Access Management (IAM) Basics
When discussing IAM, we’ll talk about three concepts i.e., principal, identity and authorization and we’ll discuss an example as well how the three concepts are applied.
- Principal: A principal in IAM terms refers to an unauthenticated entity. This is like an anonymous user.
- Identity: When a principal authenticates itself by supplying credentials, it then becomes an identity.
- Authorization: The actions that an identity is allowed or denied to perform are referred to as it’s authorizations.
Example to understand Principal, identity and Authorization
Consider a scenario where in you would like to set up a gmail account.
- When you first visit the website and sign up for a new account, you are an unauthenticated user i.e., a principal.
- After you’ve signed up and subsequently login, you will now be an identity since you have authenticated to gmail using your credentials.
- After authenticating you will be able to view, send and receive email for your email account. These rights/capabilities are your authorizations.
We hope this example helped clarify the three terms we introduced earlier.
Azure Active Directory
Azure Active Directory (more commonly known as Azure AD) is our Identity and Access Management service for the Azure cloud. Azure AD is a global service which implies that it spans all of the Azure cloud regions across the world. This service acts as our identity repository, where we can create and manage our identity resources like users and our groups, and we can also employ additional safeguards to improve the security for those identity resources by implementing measures like enabling multi-factor authentication, controlling resource access, and providing policy-based controls through the use of tools like conditional access policies.
Azure AD tenant architecture
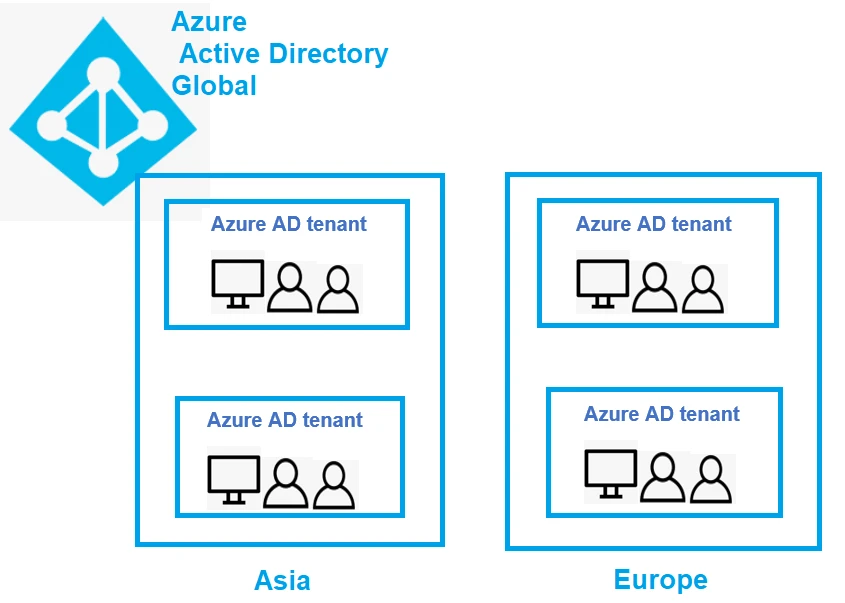
- Since Azure AD is a global service, this spans across various regions of the world and in those regions, we could provision our own instance of the service known as an Azure AD tenant, also known as an organization, and it could also be just referred to as Azure Active Directory.
- Within the Azure AD instance (tenant) we deploy is where we can create our users and have all of our identity resources and this is also the point of administration for our identity resources.
- Azure AD allows us to create multiple tenants, organizations, whichever terminology you find suitable to apply, they all refer to the same service.
- We can have several different instances of this service spanning around the world in various regions. The region in which your service is going to be provisioned, depends on how you're setting it up and what you're using to set it up.
- For example, if we create a subscription, we get a default
directory for the Azure AD service. If we create our subscription in
India region/location, then our default directory will be located in
India region. Now when we're talking about an Azure AD tenant, we need
to understand that since this represents our organization, we're going
to have a domain. We get a default domain, and this is going to look
something like
example.onmicrosoft.com. Although, we could use a custom domain if we want, likeexample.com, so that we can substitute it for usingexample.comrather than the Microsoft-provided domain. - Just to reiterate, an Azure AD tenant here represents an organization. So, our organization is analogous to an Azure AD tenant, which is equivalent to an Azure Active Directory.You'll hear all 3 of these terminologies, but they really refer to the same thing.
- You have your instance of the Azure Active Directory service that represents your organization and acts as your identity repository that you're then going to use to provide identity and access management for the resources that you have in the Azure cloud, inside of your subscriptions.
- There will be a trust relationship between the Azure AD tenant and these subscriptions because a subscription can only be associated in a trust relationship with one Azure AD tenant at a time. However, an Azure AD tenant can have multiple subscriptions.
Azure Active Directory Features
We’ll now discuss the different features of Azure Active Directory.
1. IAM platform
Azure AD is first and foremost an Identity and Access Management platform where we can have our identity resources exist in an identity repository and we can also use those identities to provide them access to resources, using entities like roles.
2. Identity security
Azure AD provides us with a number of security features to protect our identities from malicious attacks. These include enabling multi-factor authentication for our identities. Also have could implement Privileged Identity Management, which allows us to provide just-in-time or approval-based access for administrator roles. For example, if someone needs to assume administrator role in order to perform specific tasks, we can provide that in an approval-based style using Privileged Identity Management.
3. Collaboration and development
Azure AD provide us with some collaborative features like Azure AD business to business where we can invite external users into our Azure AD tenant. For example, if we want to invite a consultancy firm into our Azure AD tenant to do some work on some resources inside our Azure subscriptions, we could invite those users using these Azure AD B2B features. We could also create a separate type of tenant where we get Azure AD B2C features. This is not something that we use to provide access to entities like our Azure subscriptions, but rather access to our external-facing applications to provide our customers with identity and access management so that we can scale up the users for those external-facing applications.
4. Monitoring
Azure AD monitoring allows us to do perform auditing via things like audit logs, we can monitor the security and identity protection, and we can also perform real-time risk management based off of the user's actual actions at the time. We could monitor suspicious logins for employees. For example, an employee logging in from India at one time could not possibly login from the United States a couple of hours later. Such kind of logins could be flagged by Azure AD and we could take some action on it.
5. Identity integration
This allows us to combine Azure AD and on premises Active Directory and implement a hybrid identity solution and single sign-on using Azure AD.
6. Enterprise access
This allows us to take our applications and our devices that are registered with Azure AD and provide security for those both on-premises and in the cloud.
Azure Active Directory Licensing
Azure AD encompasses a few different licensing types:
- Free
- Office 365
- Premium P1
- Premium P2
With free, we are restricted to 500,000 directory objects, so our identity resources. With all of our license types, we have B2B collaboration enabled. Specifically, with our Premium P1 and our Premium P2, being the expensive tier, we are provided with numerous additional features like dynamic groups and conditional access.
So, if you're going to be using it for more of an enterprise use case where you want to be able to dynamically manage groups and provide conditional access policies for our users and manage external devices, then we probably want to opt for a Premium P1 or Premium P2 Azure AD license.
Given below is an exhaustive feature comparison
| Feature | Azure AD Free - Security defaults (enabled for all users) | Azure AD Free - Global Administrators only | Office 365 | Azure AD Premium P1 or P2 |
|---|---|---|---|---|
| Protect Azure AD tenant admin accounts with MFA | ● | ●(Azure AD Global Administrator accounts only) | ● | ● |
| Mobile app as a second factor | ● | ● | ● | ● |
| Phone call as a second factor | ● | ● | ● | |
| SMS as a second factor | ● | ● | ● | |
| Admin control over verification methods | ● | ● | ● | |
| Fraud alert | ● | |||
| MFA Reports | ● | |||
| Custom greetings for phone calls | ● | |||
| Custom caller ID for phone calls | ● | |||
| Trusted IPs | ● | |||
| Remember MFA for trusted devices | ● | ● | ● | |
| MFA for on-premises applications | ● |
What is the Difference Between Premium P1 and P2?
There are three core differences between P1 and P2.
- Firstly, P2 has Identity Protection, which lets you manage conditional access to apps.
- Secondly, P2 gives you Privileged Identity Management (PIM). That means you with additional management over privileged accounts.
- Finally, you get Access Reviews. All of these features are typically reserved for enterprises, and small businesses probably won’t require any of these features.
Comparing On-premises Active Directory and Azure AD
This article would be incomplete if we did not include a side-by-side comparison of Azure AD and on premises Active Directory. So, let’s quickly compare the two services at a glance.
| Active Directory on premises | Azure Active Directory |
|---|---|
| Comprise Organizational units (OUs) and Group Policy Objects (GPOs) | Comprises Administrative Units |
| Authentication through LDAP, Kerberos and NTLM | Authentication via SAML, oauth and WS-federation |
| Hierarchical structure | This has a flat directory structure |
| On premises solution | Cloud based global service |
Summary
In this article, we introduced the identity and access management offering provided by Azure i.e., Azure AD. We explained its architecture along with its different features. Finally, we compared the Azure AD pricing models based on features and also compared Azure AD to on premises Active Directory.
References
While writing this article, we referred to the official Microsoft documentation for Azure AD and also the Azure AD pricing page, links to which are provided below for further reading.
What is Azure Active
Directory
Azure Active Directory
Pricing





![Azure Web Application Firewall Deployment [Hands On]](/azure-waf-tutorial/azure_waf_hu_2f6e2af0cf3efd4b.webp)