Overview on Azure Web Application Firewall (WAF)
A Web Application Firewall (WAF) protects applications from multiple application-layer attacks. it may be cross-site scripting, SQL injection, cookie poisoning, etc. As we are moving towards cloud modernization, we should consider application security in account while publishing applications on the internet.
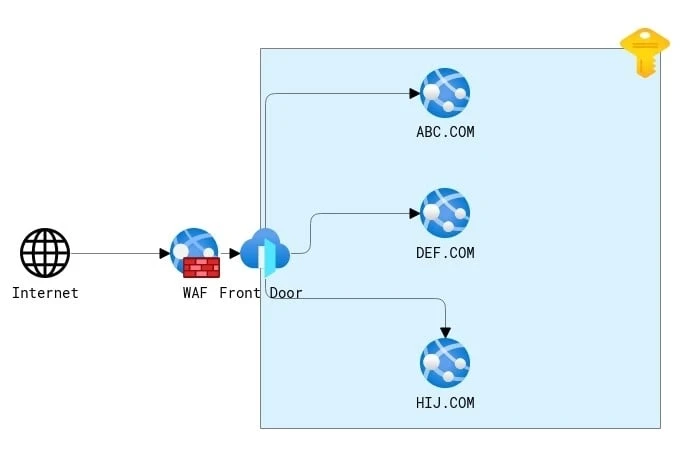
Azure provides Azure WAF service to provide their applications secure from internet attacks. it can be attached to the regional and global resources. Azure WAF is limited to working with Azure Front Door, Azure Application Gateway, and Azure CDN.
Prerequisite
- Azure Subscription
- Azure Front Door / Application Gateway for applying WAF
- Basic Understanding of WAF
Step 01: - Creating WAF Policy
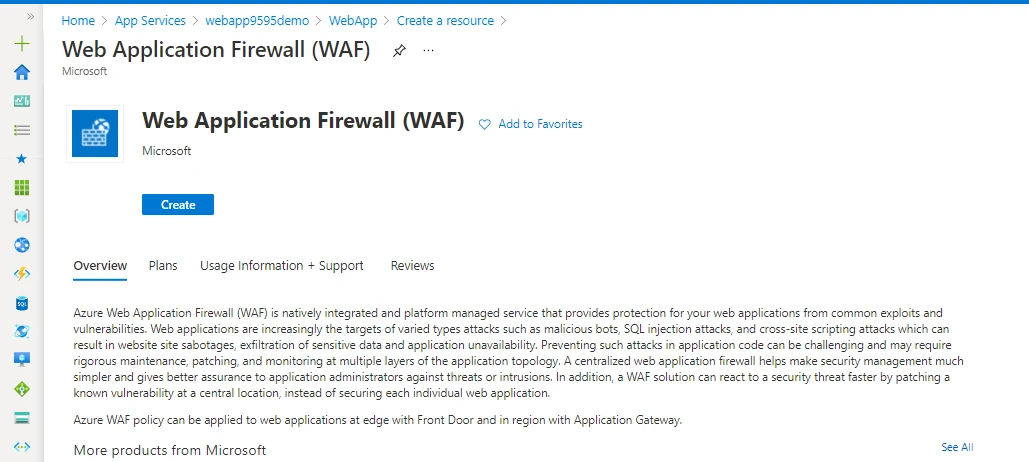
You can find WAF resources by simply searching it in your subscription as per the below image. You can get an overview of the service in the same pane.
Click on Create to start the wizard. In the Basics tab you can see where you want to use this WAF policy. as mentioned you can use the WAF policy for limited resources.
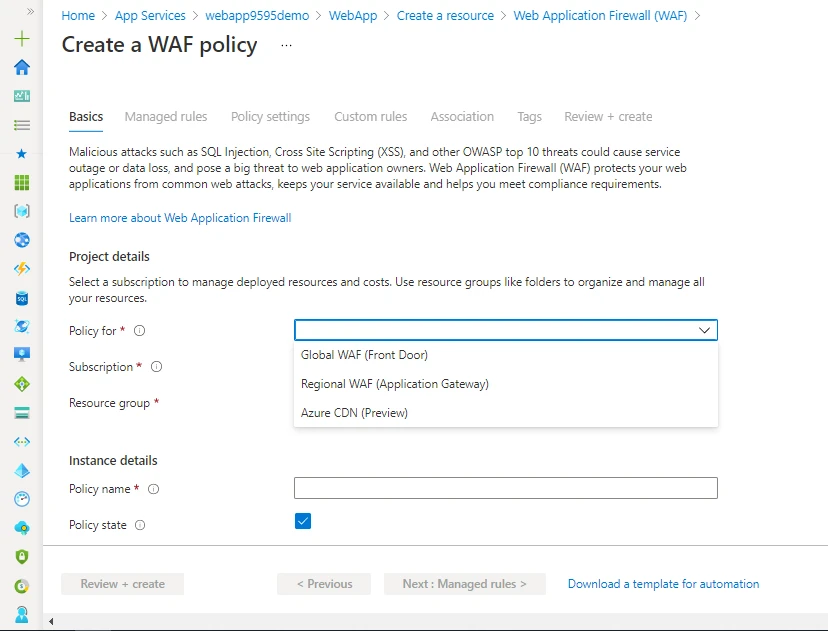
Next, you must give a name for your policy, like you can have multiple policies for multiple regional resources or multiple environments.

Here we have a very interesting option to check. Policy state and Policy mode.
Policy state: - You can create WAF and let it disable for time being and then later you can attach it to resource and enable.
Policy mode: - We have Detection and Prevention.
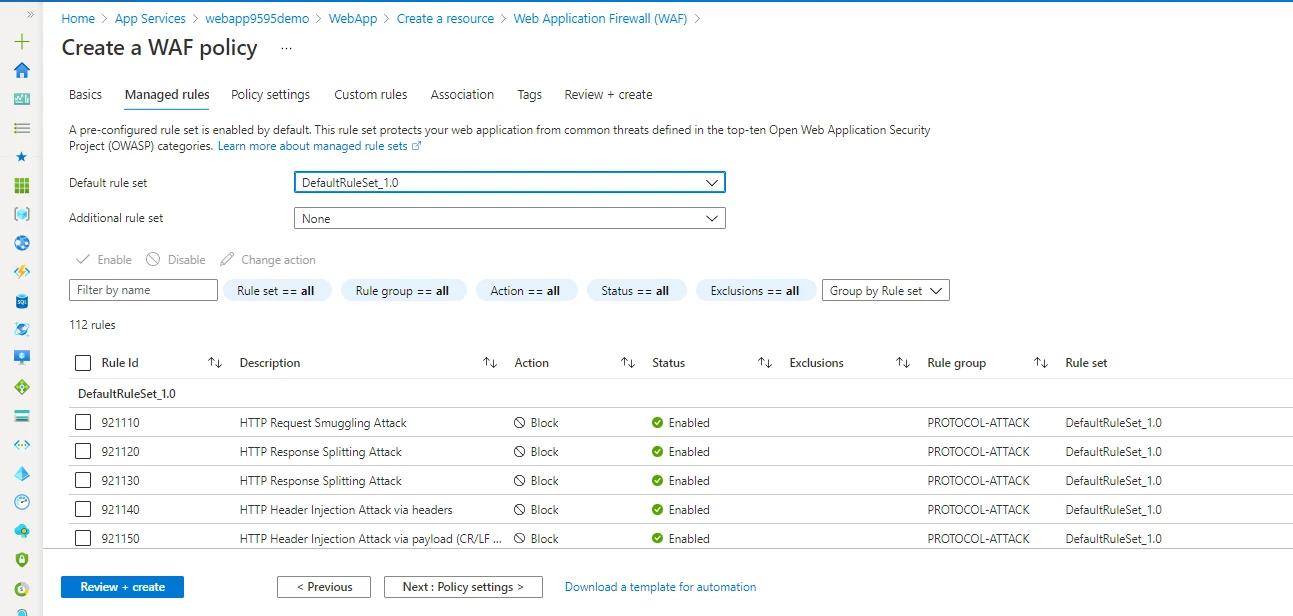
Next, we must select a rule set that can be associated with WAF. A pre-configured rule set is enabled by default. This ruleset protects your web application from common threats defined in the top-ten Open Web Application Security Project (OWASP) categories
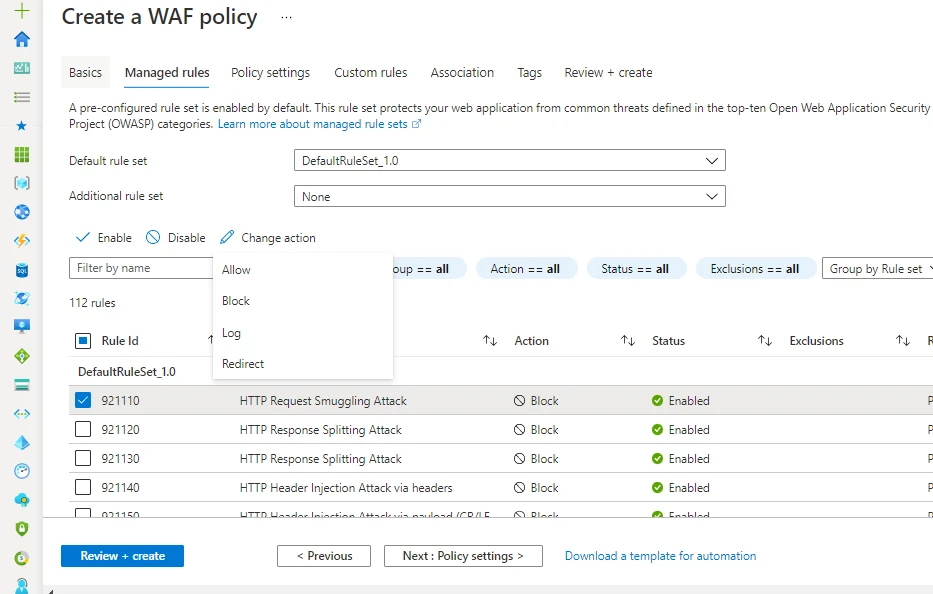
In the same way, you can change the behaviour of WAF rule action depending upon your application behaviour.
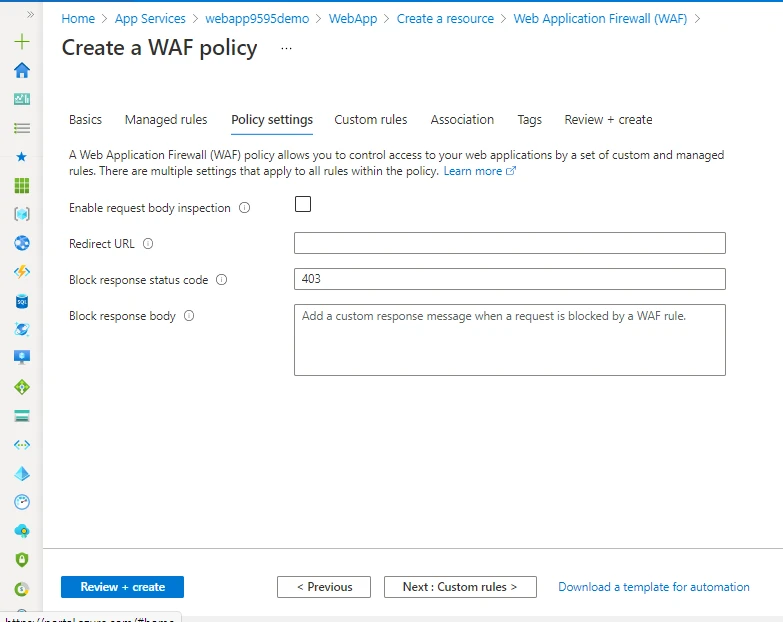
Policy setting helps you to create a response after something is blocked by your WAF. as per the above image you can set it up manually.
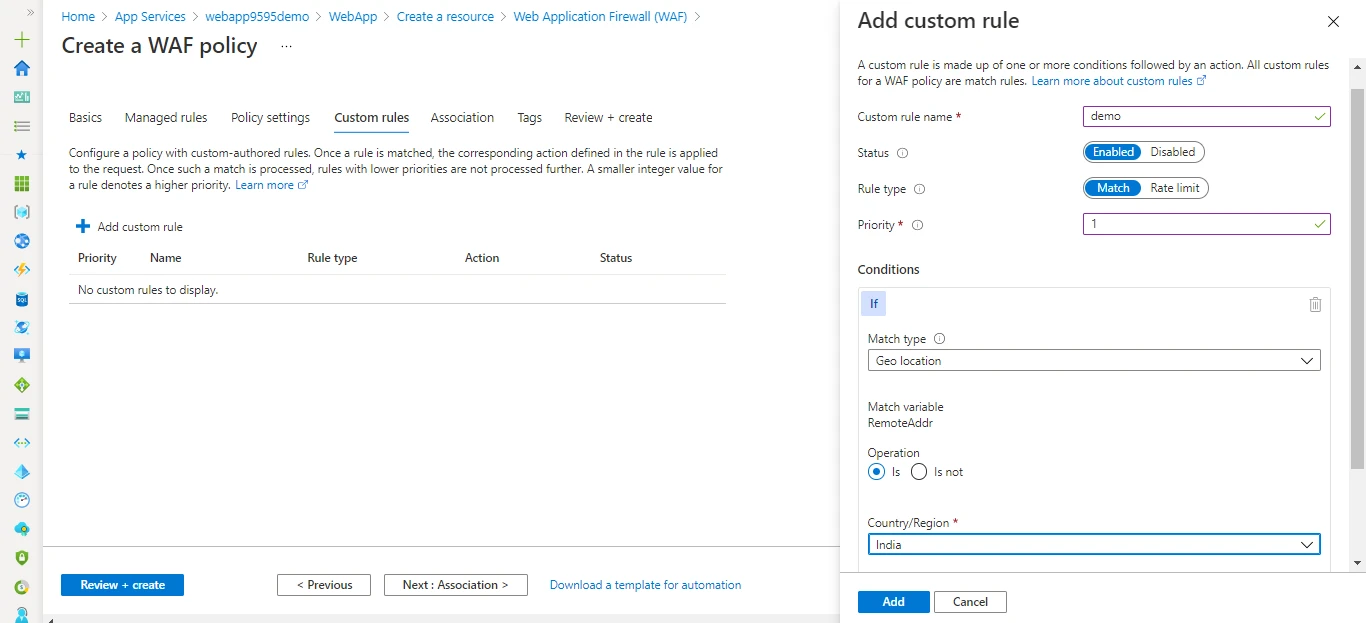
In the same way, we have options to create custom rules. as every organization has its own customization required to run its application.
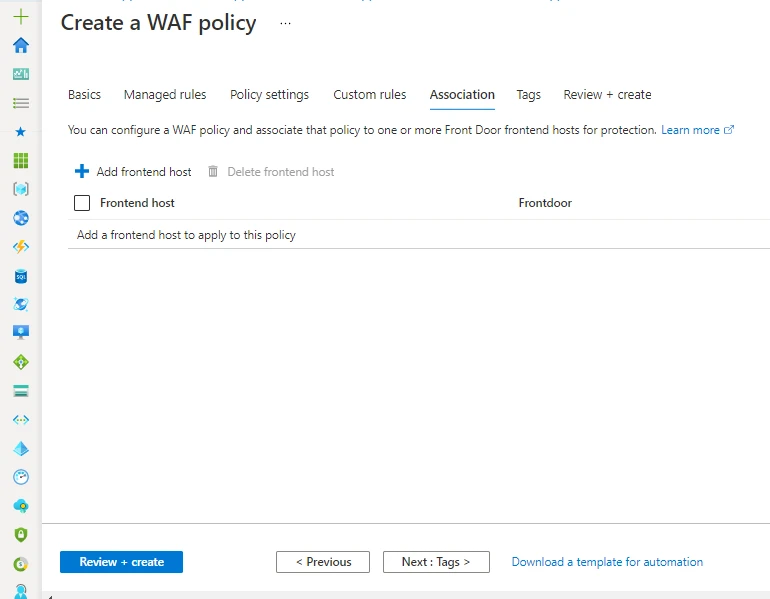
And the final part is to associate WAF with Azure Services. as discussed, you can associate WAF with Front Door, Application Gateway, or Azure CDN.
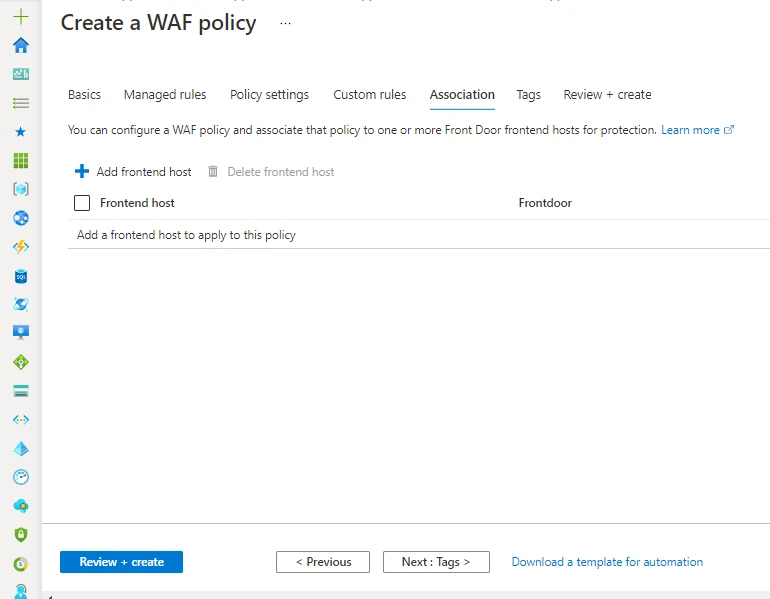
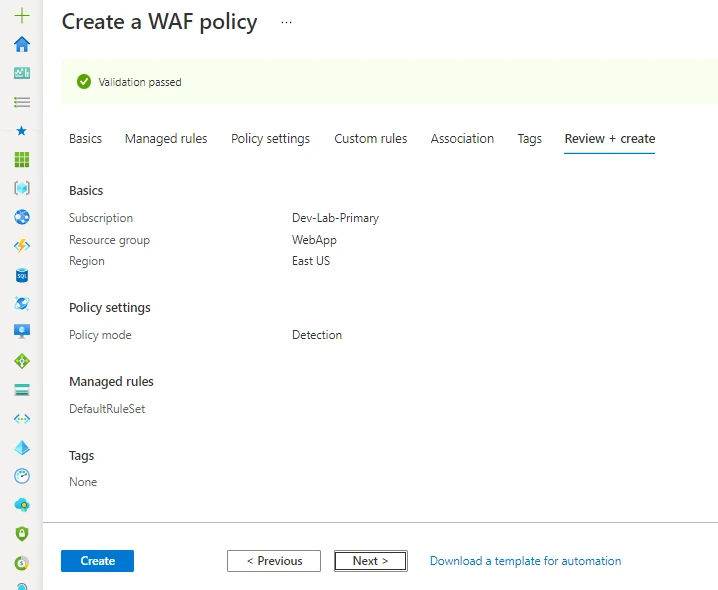
Now, you can review and create the WAF policy.
Step 02: - How to attach WAF to Azure Front Door
In the above step, we have created a WAF policy for the global resource Front Door. Now we must attach it to the Front door as per the below steps.
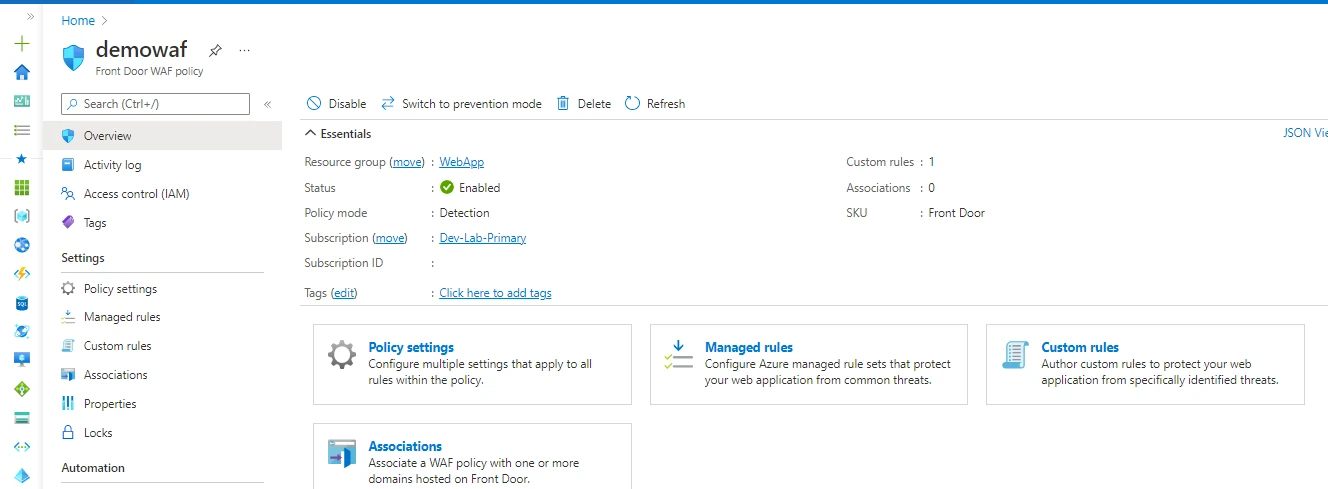
After creating the WAF policy you can see the overview page. here you can see a number of rules, their associations, and their status like prevention mode or detect mode and you can change it from here also.
Go to the Association's tab and here you can see Add frontend. Click on that option.
You will get a list of Front Doors in your subscription. from that drop-down menu select the required front door.
You can follow the below article to deploy Front Door.
https://www.golinuxcloud.com/azure-front-door-tutorial/

Once you attached the WAF you can see the under associations tab. you can attach a single WAF to multiple Front-end hosts.

You can check the same from the front door WAF option. As per the below image, you can see its frontend host and attached WAF policy.
Step 03: - Monitor and access WAF logs
Basically, it’s very important to monitor WAF logs to understand the behaviour of our application. it should not be the case that WAF is blocking legitimate requests.
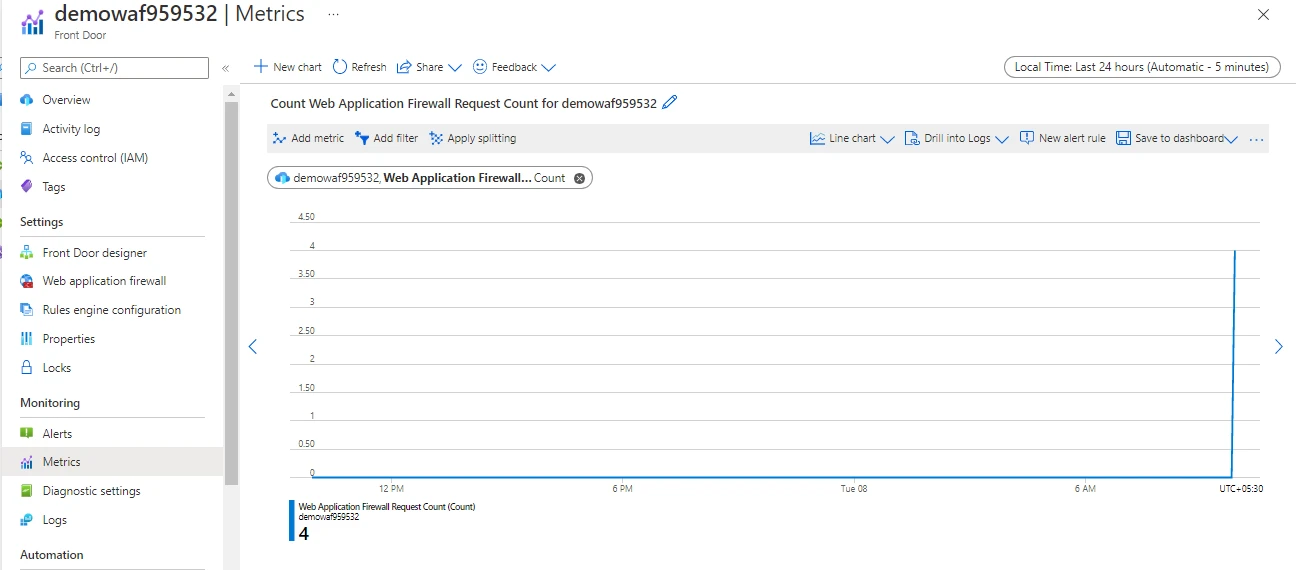
You can monitor WAF using Front Door metrics. As per the below image you can see we have to select WAF as a metric to show results.
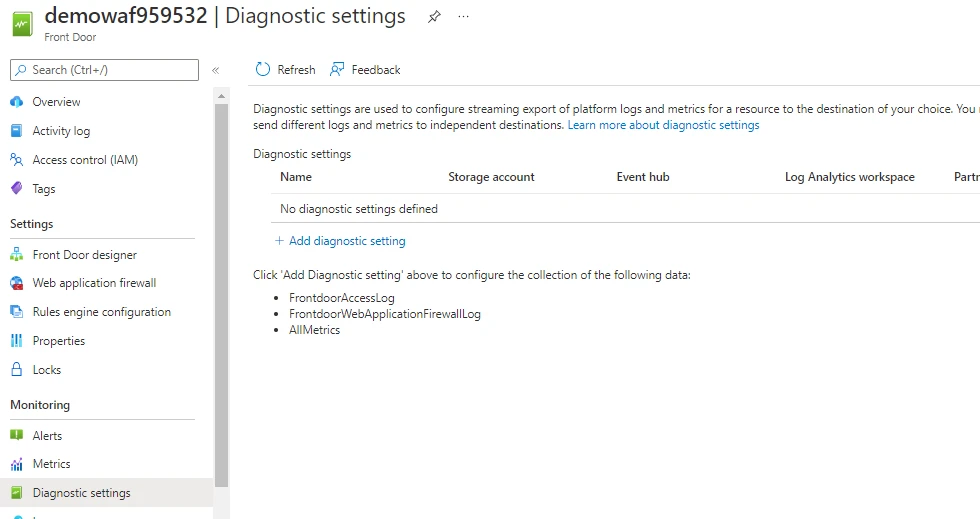
and for storing logs of WAF you must enable the diagnostic setting of the attached resource. you can see the below image on how to enable the diagnostic setting for storing WAF logs.
First, go to the Diagnostics setting. and click on add diagnostic setting
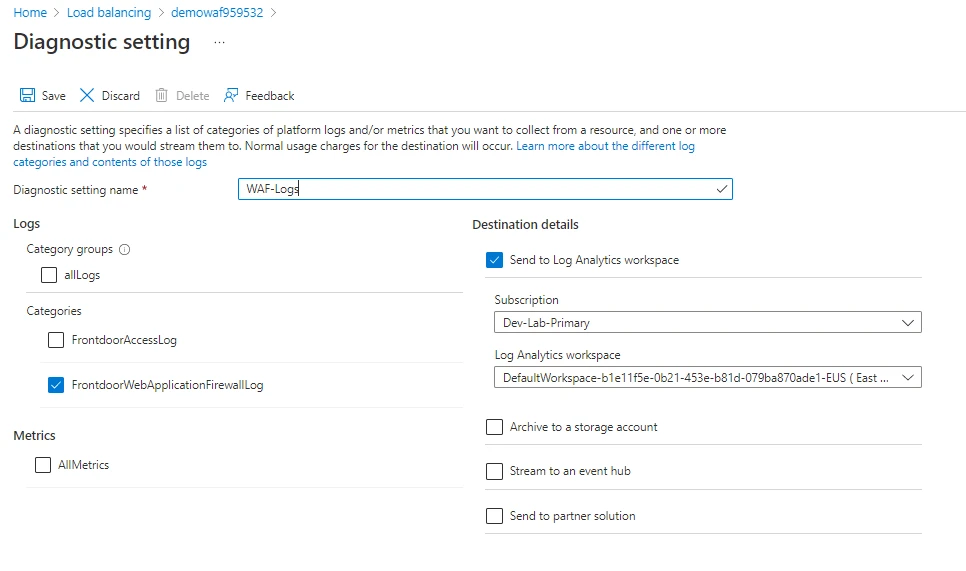
Next, you can see Categories where you can select which logs you to store and where you want to store them.
We have options to store logs into Log Analytics, Storage account and etc. mostly will use log analytics as it works with the front door hand in hand and gives is seamless results. but if you want to store logs for the long term, I recommend you store them in a storage account.
It takes time to populate log into log analytics to show the results. you can query it from logs.
Examine WAF logs using Azure Log Analytics - Azure Application Gateway | Microsoft Docs
Summary
Azure Web Application Firewall (WAF) is an advanced version of a traditional firewall that resides on the outer edge of the network, in front of the public side of a web application. It works based on specific security rule sets.
WAF intercepts & analyzes each and every HTTP request before they reach the web application. It protects web applications from the below threatening cyber-attacks. It detects suspicious network traffic and automatically filters the same.

![Azure Web Application Firewall Deployment [Hands On]](/azure-waf-tutorial/azure_waf-800w.webp)


![Azure Database for PostgreSQL Deployment [Step-By-Step]](/azure-database-for-postgresql-deployment/azure_database-1_hu_3928ddbe1d94e123.webp)

![How To Deploy Azure Cosmos DB [Step-by-Step]](/deploy-azure-cosmos-db/golinuxcloud-default_hu_f6c9f1c4d50174f9.webp)
![How to Install RabbitMQ on Azure [Step-by-Step]](/install-rabbitmq-on-azure/azure_install_rabbitmq_hu_c6dd595a881a96af.webp)
![How to deploy SQL Database on Azure [Step-by-Step]](/deploy-sql-database-on-azure/azure_deploy_database_hu_2cf055a64750f0d.webp)
![Deploy and Configure Azure Application Gateway [Step-by-Step]](/deploy-azure-application-gateway/azure_app_gateway_hu_1de3d66e91fab61.webp)
![Azure Database For MySQL Deployment [Step-By-Step]](/azure-database-for-mysql-deployment/azure_database_hu_f85ad473ed915ea7.webp)