What is Banner Grabbing
While doing reconnaissance on a target, we may use some of the information regarding our target which is readily available. In banner grabbing, penetration testers will look for banner information displayed while interacting with the target. Information contained in these banners may be of great use to the penetration testers while launching attacks on the target. Some of the information we can find out through banner grabbing include; the name of the software being used, the version of the software, and even the operating system that is used by the target.
In banner grabbing, penetration testers can easily find out the vulnerabilities related to the target by checking the information relating to software against a database of known vulnerabilities. Banner grabbing can be divided into two main types
Types of banner grabbing
Passive banner grabbing
In the passive method, the penetration tester does not interact with the target server. A third party software is deployed hence the pentester is not connected directly to the target. Penetration testers will use this software to analyze the packets received from the target server to get the information relating to the server. Intrusion detection systems hardly detect passive banner grabbing. There are also websites that can be used in passive banner grabbing such as Shodan.
Active banner grabbing
Active banner grabbing requires the penetration tester to send and analyze captured packets without the use of a “proxy” software. This type of banner grabbing is easily detected by the intrusion detection system since the penetration tester has to have a connection with the target server.
Requirements
- Have a running instance of Kali Linux
- Have a target server (In this guide we will be using Metasploitable)
- Knowledge of using the terminal
In this guide, I will guide you on how to use various tools to perform banner grabbing on aMetasploitable server.
Banner grabbing using various tools
Nmap
Various techniques can be employed while using Nmap for banner grabbing. These techniques are used depending on the type of information the penetration tester intends to obtain from the scan. We will use various methods to collect information related to our target metasploitable server.
To acquire information relating to a server on Nmap, we will scan a specific port running a service on the target server. We can include various flags to obtain detailed information.
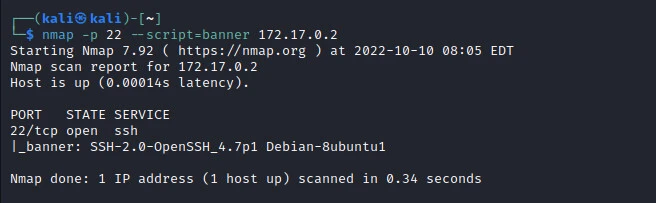
Nmap has a script “banner” to help a user while performing banner
grabbing. In our case, we want to obtain information relating to
services running on port 22 of our target server. To use the script we
will add -script=banneron our command as shown below.
nmap -p 22 --script=banner 172.17.0.2
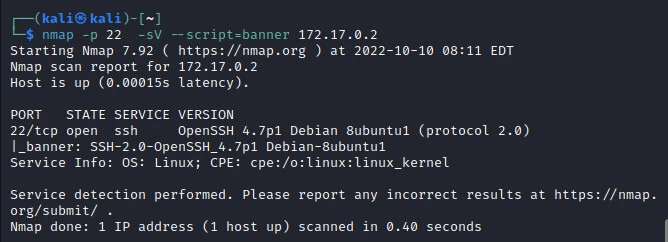
In advanced scanning, we can add more flags to help gather even more
information relating to the target server. We can add an -sV flag to
help us determine the software version that is being run as shown in the
image below.
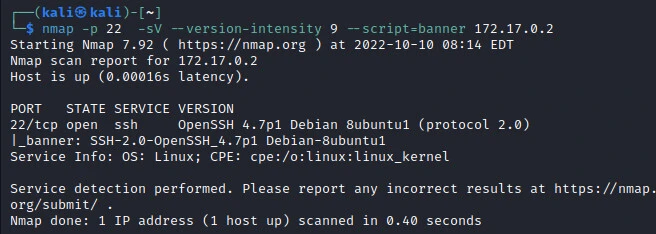
We can also increase or decrease the number of probes to use when
detecting the software version by changing the intensity level of the
scan with the argument, --version-intensity [0-9], just after
-sV flag. This
Nmap option
is incredibly effective against services running on non default ports
due to changes in the configuration.
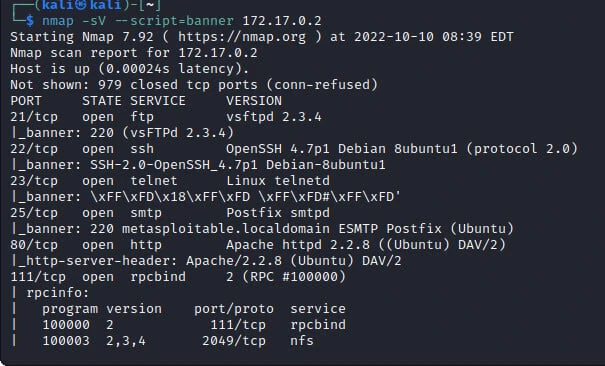
Nmap also allows us to scan for common ports by default. To use these options we just need to run a scan without specifying the target port. This will scan and return all the information related to the ports found as shown in the image below.
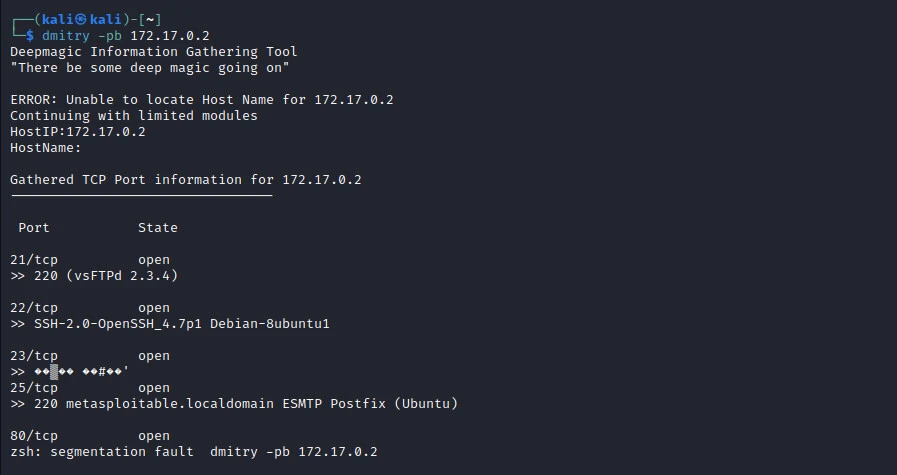
Dmitry
Deepmagic Information Gathering Tool can also be used for banner
grabbing. Dmitry is a tool used by penetration testers to gather all the
possible information related to a target domain. With Dmitry’s base
functionality a penetration tester can be able to gather the following
information related to a target host; email addresses, open ports,
possible target subdomains e.t.c. To use Dmitry for banner grabbing, we
will be adding -pb flag. This flag helps a penetration tester to
gather the banners for all the target hosts' open ports.
Netcat
This is a network utility tool that can be used by penetration testers to grab an FTP banner for our target. To get the banner information on Netcat we simply run the command
nc <target> <port>
Since we are using netcat for the FTP banner, we will use the FTP port which is 21 as shown in the image below.

As you can see in the image above, our target is using version 2.3.4.
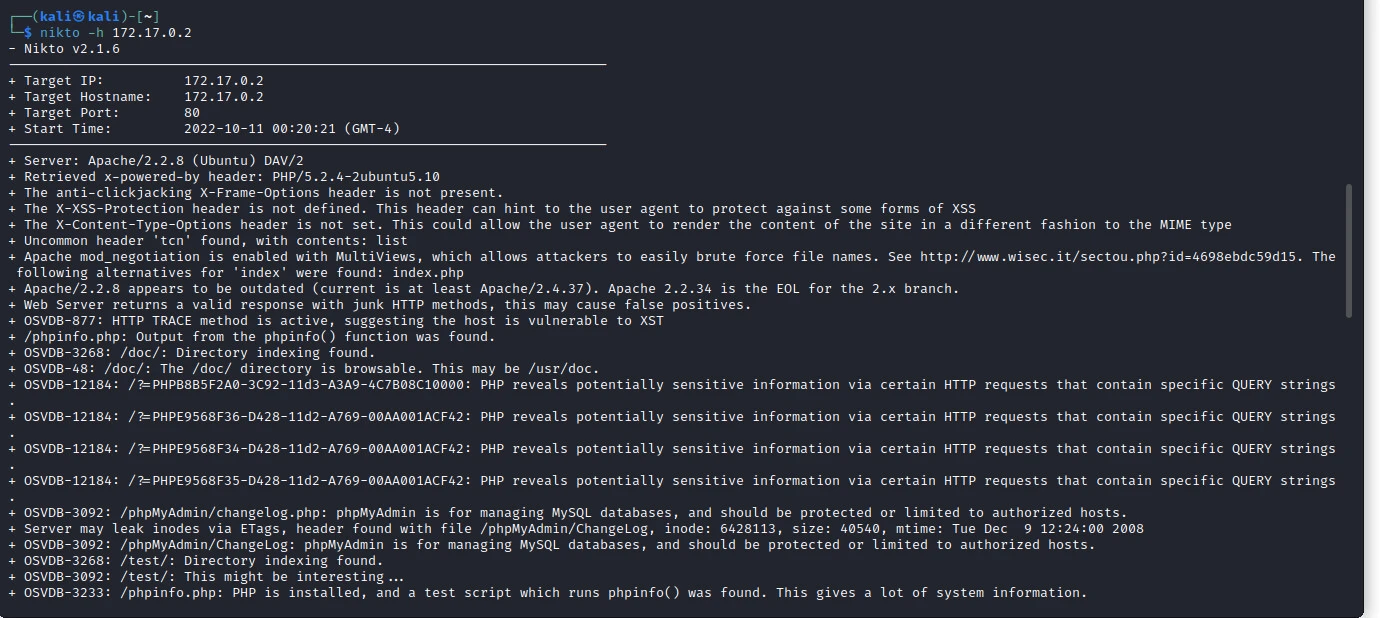
Nikto
Nikto is another tool that can be used for banner grabbing. It is an open source web application scanner. To capture details about the installed web server version, and configuration files among other useful information. To grab banners related to a target web server, we will run the below command.
nikto -h <target>
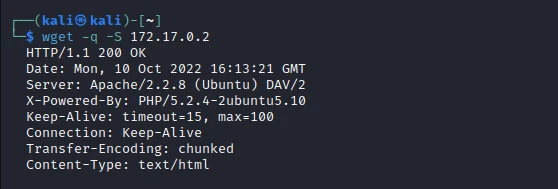
Wget
Wget is a command-line utility for downloading files from the web. The tool can be used to get banners from a target server. To use wget we will run the command shown below.
wget -q -S <target>
-q suppresses normal output while -Sflag will show the headers that
have been sent by the target.
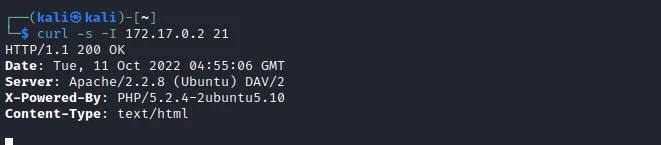
cURL
This is a command line interphase tool that a user can use to transfer data, using the libcurl library, from a remote server without the need for user interaction. cURL also can retrieve banner details of HTTP servers. To use it for banner grabbing, we simply run the command
curl -s -I <target>
In the above command, we have added 2 flags to ensure the effectiveness
of
cURL while
fetching banner information. -s is used to suppress error messages
being displayed and -I is to print the header information we are
fetching.
Conclusion
In the information gathering stage of penetration testing, banner grabbing is very useful as it helps the penetration testers to have knowledge of the target’s software versions. This will later serve as a starting point when looking for vulnerabilities within the target system. There are numerous tools we can use for banner grabbing during the reconnaissance stage depending on the type of banner grabbing you want to use. i.e. Active or passive banner grabbing. With the help of this guide, you can be able to perform banner grabbing on the target server for common services that are running on a target server.

![6 Banner Grabbing Tools with Examples [100% Working]](/banner-grabbing/banner_grabbing-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)