Hashing cannot be reversed as opposed to encryption. Taking an informed guess of the password, processing it through the hashing algorithm, and comparing the output with the hash you already have are the only techniques to "retrieve" the passphrase from the hash. The tools available for cracking hashes are pretty sophisticated; John the Ripper and Hashcat jointly offer a large number of hash types including all kinds of excellent features and great execution optimizations, as you would anticipate from such a big and time-consuming task.
Nevertheless, in the end, it's the hardware that poses the major challenge, not the software. In this guide, we will be installing and demonstrating how we can use hashview for cracking hash by checking for a passphrase hash against a world list.
Requirements
- PC running on Ubuntu. (You can check out the guide on how to dual-boot Ubuntu).
- A file containing hashes to be cracked.
- A wordlist.
- Knowledge of using a terminal.
Hashcat Overview
This is a password-cracking tool that can be used in cracking the hash of some of the most complex password formats. To achieve that, it offers versatility, efficiency, and multiple methods of cracking a particular passphrase. Hashcat also supports the use of previously generated dictionaries, brute force, and even rainbow tables techniques when cracking hash for efficiency. Some of the features that make hashcat the perfect tool for cracking hash include;
- It supports multiple threads when cracking hash.
- It is supported on various common operating systems and supports multiple hashes (Linux, Windows, and OSX ).
- Sessions can be stopped and automatically restored. At startup, they distinguish retrieved hashes from the output file.
- Both hex files are supported. (hex-charset and hex-salt)
- Threads can be configured and executed based on priority.
- Performance and optimization-focused implementations of more than 90 algorithms are possible.
- Specialized rules can be used to enhance any of the attack modes.
- It supports multiple hashing algorithms (MD4, MD5, SHA1, MySQL, etc.)
In this guide, we will be cracking hash on a Ubuntu operating system.
Install Hashcat
Before cracking the hash, we have to install hashcat. Hashcat can either be used via the command line interface or using hashview which is a web-based version of hashcat and has added features not available via the command line. In this guide, I will be showing you how to install and use hashcat from the command line and hashview to crack hash on a web platform.
Hashcat command line installation
To install hashcat on the command line interface is as easy as installing other tools. We first need to ensure that the system's packages are up to date by running the following commands.
sudo apt update
sudo apt upgrade
Ensure you have an active internet connection before running these commands. Once the update is done, we can now install hashcat via apt and start cracking hash.
sudo apt install hashcat
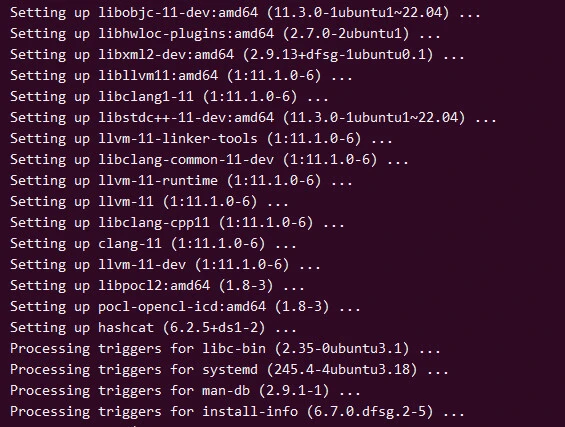
After the installation is complete, we can now use hashcat via the command line for cracking hashes.
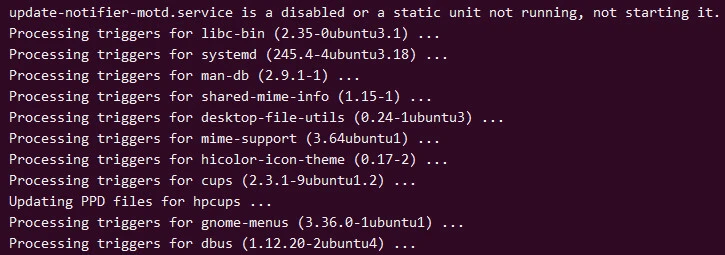
Install Hashview
Installing hashview is different from installing hashcat. Hashview is just hashcat but it has a graphical user interface. While using hashview for cracking hashes, the user doesn't need to know the commands to be used. He just needs to provide a file with a list of hashes, a word list to check against, and other required information. To use hashview, we first need to install the server and then add the agent.
Step-1: Installing MySQL
The first step is to set up the database to use with hashview. Hashview uses a MySQL database therefore we install it.
sudo apt install mysql-server
After installation is complete we start MySQL service using the command.
sudo service mysql start
We can now run a secure installation of the MySQL server using the command.
sudo mysql_secure_installation
Step-2: Configuring MySQL
When the installation is complete, we are now ready to create an account for use with hashview while cracking hashes on our database server.
To create an account we fire up a terminal and run
sudo mysql
We then create a user using the command;
CREATE USER 'yourusername'@'localhost' IDENTIFIED BY 'YOURPASSWORD!';Grant privileges to the created account.
GRANT ALL PRIVILEGES ON hashview.* TO 'hashview'@'localhost';
FLUSH PRIVILEGES;and finally, create a hashview database
create database hashview;We now have the database ready for use. The database will be storing hash files, accounts information, jobs created by a user, and other required information while cracking hashes.
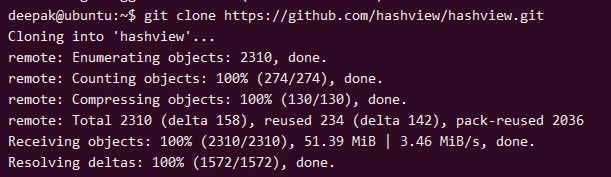
Step-3: Installing hashview server
To install hash view we first need to install the dependencies required for hashview to run.
sudo apt-get install python3 python3-pip python3-flask
We then clone hashview server files from its GitHub repository as shown below.
git clone https://github.com/hashview/hashview.git
Next, we navigate into the directory of the downloaded files to install the required dependencies.
cd hashview
pip install -r requirements.txt
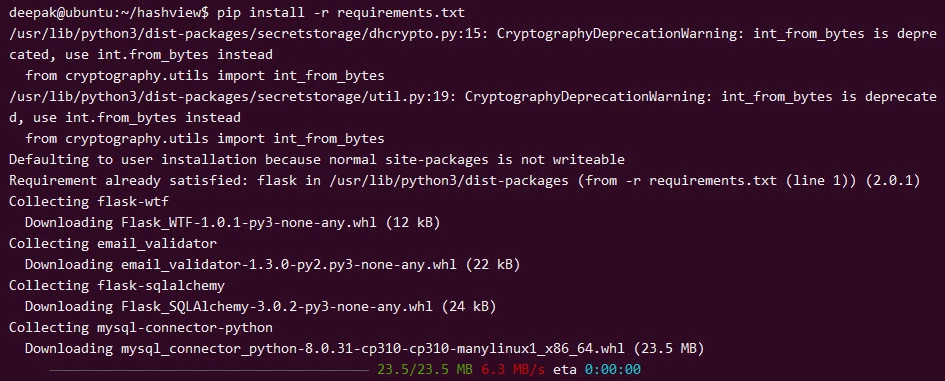
After the installation is done, we can now set up hashview by running the setup file.
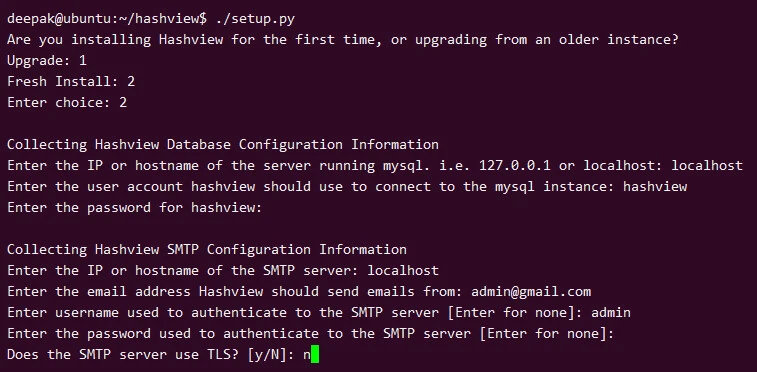
./setup.py
When we run the setup, we are required to provide the database information such as the database IP, account to use, SMTP configuration, and other information relating to that instance of hashview.
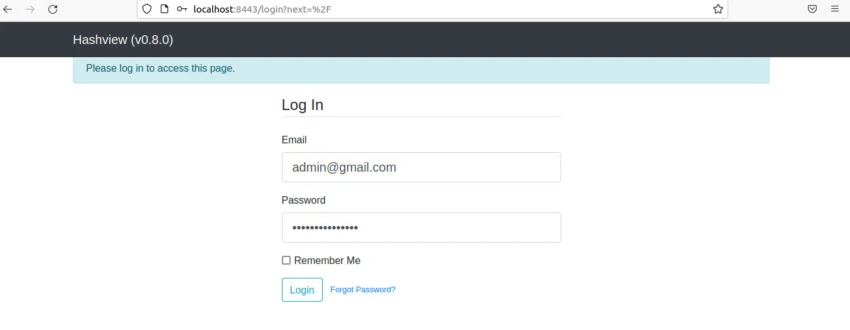
After setup, we can now run the server instance of hashview. To access the running instance, we will use a web browser of choice as shown in the image below. We are required to navigate to http://localhost:8443 and log in using the login details we provided during the setup.
The hashview server is ready for use. The next step is to add a hashview-agent to help in cracking hashes.
Step-4: Installing a hashview agent** **
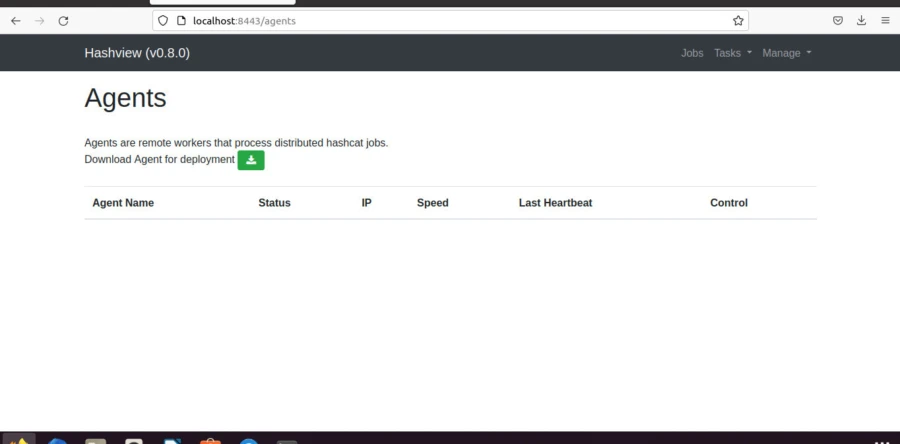
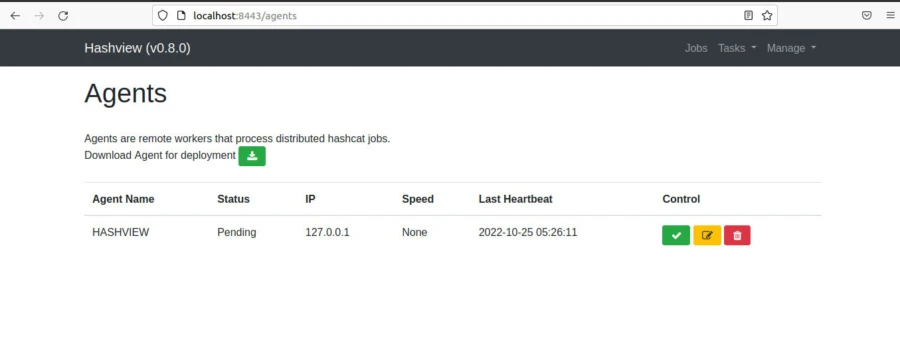
Installing a hashview-agent for cracking hashes using hashview is dead simple. We first download a hashview-agent from within the hashview server by navigating to the agents' option as shown in the image below.
When the download completes we navigate into the directory where we downloaded the hashview-agent and extract it using the commands below.
cd Downloads
tar -xzvf hashview-agent.0.8.0.tgz
We navigate into the newly created directory and install the required dependencies.
pip install -r requirements.txt
After installation is complete we are now ready to run and configure the agent for use while cracking hashes.
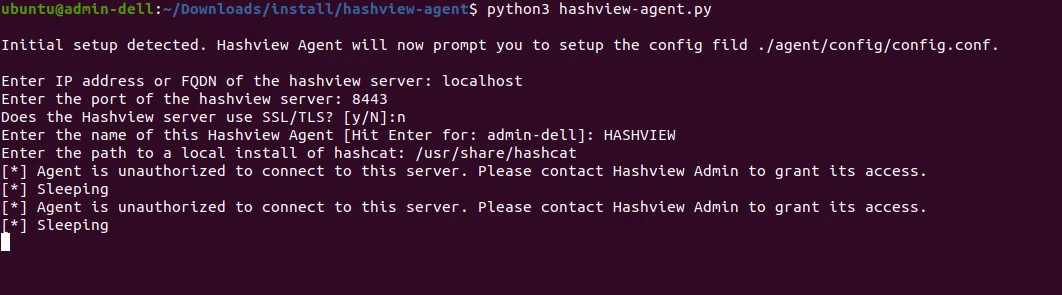
python3 hashview-agent.py
we are required to provide server information before we can add the hashview agent as shown in the image below.
When we navigate back to the agents' page on hashview, we have to allow the agent for us to use it in cracking hashes as shown in the image below.
Step-5: Let's start cracking hashes
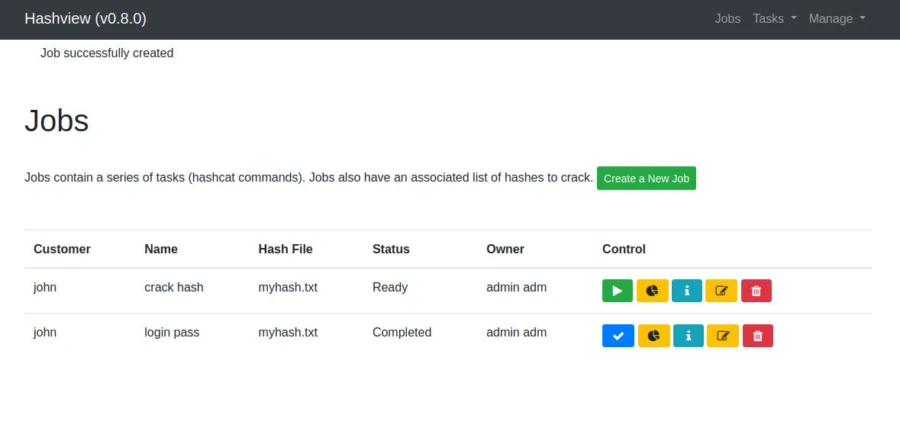
Once the agent is allowed, we can now create a job by navigating to the jobs page. When creating a job on hashview, we are required to provide information such as the hash file from which we are cracking the hashes, the name of the job, the customer, and the world list file to use for that job. Once everything is set up we can now start the cracking job. With hashview, we can perform unattended cracking by adding to be notified via email when a hash has been cracked.
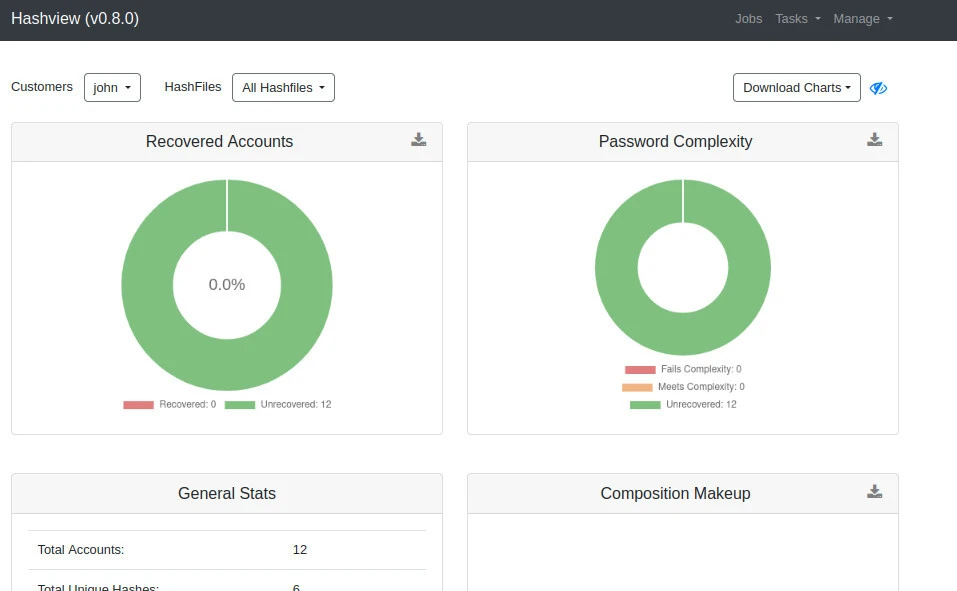
Within hashview, we can view general cracking analytics or analytics relating to a specific job. Some of the information that can be found include; Number of cracked hashes and the number of hashes that have not been found. You can also download all cracked and uncracked hashes as a text document.
Conclusion
In the above guide, we were able to install and use hashview for cracking hashes. Although there are advanced tools such as hashview and hashcat, the efficiency of these tools depends largely on the hardware capabilities of the device that is being used. The efficiency of hashview while cracking hashes can be improved by using world lists which have commonly used passphrases. In our next article on cracking hashes, we will be cracking hashes from the world list we will generate.







![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_1295ec8cece3ddb1.webp)

