In this tutorial I will share you the steps to disable SELinux properly in Linux environment although it is not recommended instead you can choose to change active mode to Permissive. We will cover this topic in detail in this tutorial for your better understanding.
If you have already made up your mind then you can directly jump over to: Disable SELinux Permanently
What is SELinux?
- The default access controls that are active on a regular Linux system are based on Discretionary Access Control (DAC) mechanism
- Consider the
/etc/shadowfile, which contains the password and account information of the local Linux accounts - Without additional access control mechanisms in place, this file is readable and writable by any process that is owned by the root user, regardless of the purpose of the process on the system.
- Similarly lots of software daemons run as the Linux root user or have significant privileges on the system
- Errors within those daemons can easily lead to information leakage or might even lead to remotely exploitable vulnerabilities.
- SELinux implements Mandatory Access Control (MAC) unlike its DAC counterpart, gives the administrator full control over what is allowed on the system and what isn't.
Mandatorymeans that access control is enforced by the operating system and defined solely by the policy rules that the system administrator (or security administrator) has enabled- SELinux fundamentally answers the question:
May <subject> do <action> to <object>?, for example:May a web server access files in users' home directories? - A MAC system can be configured to only allow a limited number of processes to read from and write to the file. On such specifically configured systems, a user logged on as root cannot directly access the file or even move it around. He can't even change the attributes of the file:
# id
uid=0(root) gid=0(root)
# cat /etc/shadow
cat: /etc/shadow: Permission denied
# chmod a+r /etc/shadow
chmod: changing permissions of '/etc/shadow': Permission denied
Should I use SELinux?
- There is no plain simple answer to this question
- It all depends on requirements but the general recommendation is to keep this in Enforcing state
- SELinux enhances system security so if security is your primary concern then you must use SELinux in your environment
- Although I would suggest you can choose to keep it in
Permissivestate rather thanDisabled
SELinux states and modes
SELinux supports three major states that it can be in: disabled,
permissive, and enforcing. These states are set in the
/etc/selinux/config file, through the SELINUX variable
# egrep ^SELINUX= /etc/selinux/config
SELINUX=enforcing
The states are described as follows:
Enforcing
- This is the default, and recommended, mode of operatio
- This means SELinux is active and will enforce its policy on the system
- Violations are reported and also denied
- This is sometimes called host intrusion prevention, as it enforces the rules while logging the actions it takes.
Permissive
- SELinux is active but will not enforce its policy on the system
- Instead, any violation against the policy will be reported but remain allowed.
- This is sometimes called host intrusion detection as it works in a reporting-only mode.
Disabled
- The SELinux code disables further support, booting the system further without activating SELinux.
Check SELinux Status
There are a couple of methods using which you can check the status
of SELinux in your linux environment
We can use the getenforce command provided by the libselinux-utils
# getenforce
Enforcing
To get more details about this status use sestatus
# sestatus
SELinux status: enabled
SELinuxfs mount: /sys/fs/selinux
SELinux root directory: /etc/selinux
Loaded policy name: targeted
Current mode: enforcing
Mode from config file: enforcing
Policy MLS status: enabled
Policy deny_unknown status: allowed
Memory protection checking: actual (secure)
Max kernel policy version: 31
It is also possible to query the pseudo-file /sys/fs/selinux/enforce
to get similar information. If the file returns 1, then SELinux is in
the enforcing mode. If it returns 0, then it is in the permissive
mode:
# cat /sys/fs/selinux/enforce
1
Change SELinux mode runtime without reboot
- You can toggle the SELinux state between
PermissiveandEnforcingwithout and reboot. - Changing the state to permissive is not completely as
Disabledbut SELinux will not enforce any policy and instead only report violations. - To change the state of SELinux for runtime you can use
setenforce - Now
setenforcecan not disable SELinux but it can toggle betweenEnforcing (1)orPermissive (0)mode
To change the active mode to Permissive, use:
# setenforce 0
Or you can also change value of /sys/fs/selinux/enforce to 0
# echo 0 > /sys/fs/selinux/enforce
Verify the current mode
# getenforce
Permissive
To switch it back to <strong>Enforcing</strong>, use:
# setenforce 1
Or you can also change value of /sys/fs/selinux/enforce to 1
# echo 1 > /sys/fs/selinux/enforce
Verify the current mode
# getenforce
Enforcing
Disable SELinux mode using GRUB2
Using the setenforce command makes sense when we want to switch to the
permissive or enforcing mode at a point in time when we have
interactive access to the system.
But what if we need this on system boot?
If the system refuses to boot properly due to SELinux access controls,
we cannot edit the /etc/selinux/config file.
You can define either of the following parameters in
/etc/sysconfig/grub that take will precedence over the
/etc/selinux/config setting
Disable SELinux
- Use
selinux=0 - This informs the system to disable SELinux completely, and has the
same effect as setting
SELINUX=disabledin the config file. - When set, the other parameter (enforcing) is not consulted.
- Please remember that booting a system with SELinux disabled means that to enable it again, the file system must be relabeled completely.
Enable Permissive Mode
- Use
enforcing=0 - This informs the system to run SELinux in the permissive mode, and has
the same effect as setting
SELINUX=permissivein the config file.
Enable Enforcing Mode
- Use
enforcing=1 - This informs the system to run SELinux in the enforcing mode, and has
the same effect as setting
SELINUX=enforcingin the config file.
For example, SELinux is set to Enforcing as per /etc/selinux/config
# egrep ^SELINUX= /etc/selinux/config
SELINUX=enforcing
But I will go ahead and change SELinux to Permissive using GRUB2
# grep GRUB_CMDLINE_LINUX /etc/sysconfig/grub
GRUB_CMDLINE_LINUX="resume=/dev/mapper/rhel-swap rd.lvm.lv=rhel/root rd.lvm.lv=rhel/swap rhgb quiet biosdevname=0 net.ifnames=0 enforcing=0"
I have appended enforcing=0 at the end of GRUB_CMDLINE_LINUX
Next rebuild GRUB2 configuration file
# grub2-mkconfig -o /boot/grub2/grub.cfg
Generating grub configuration file ...
done
Reboot the server, post reboot I see that SELinux is in Permissive
mode even though it is marked as Enforcing in /etc/selinux/config
# getenforce
Permissive
/etc/selinux/config then these
GRUB2 kernel parameters for will not be considered
If the system fails to come UP then:
- Reboot the system until the GRUB2 boot screen comes up.
- Navigate with the arrow keys to the boot entry for which the SELinux state has to be altered. This is usually the default boot entry and already selected.
- Press the E key to edit the boot entry line. Do this before the GRUB2 timer reaches zero; otherwise, the system will continue to boot.
- Use the arrow keys to go to the end of the line that starts with
linux,linux16, orlinuxefi - Add
enforcing=0to the end of this line. - Press
Ctrl + Xto boot the entry.
Disable SELinux for single service
- Instead of changing SELinux mode to
Permissivefor entire system, you can set individual domains to permissive mode while the system runs inenforcingmode - To make a domain permissive, run the
semanage permissive -a <domain>command, where<domain>is the domain you want to make permissive. semanageis provided bypolicycoreutils-python-utilsrpm in RHEL and CentOS
For example, run the following command as the Linux root user to make
the httpd_t domain (the domain the Apache HTTP Server runs in)
permissive:
# semanage permissive -a httpd_t
From the /var/log/messages
May 30 16:24:52 client kernel: SELinux: Converting 2264 SID table entries...
May 30 16:24:54 client kernel: SELinux: policy capability network_peer_controls=1
May 30 16:24:54 client kernel: SELinux: policy capability open_perms=1
May 30 16:24:54 client kernel: SELinux: policy capability extended_socket_class=1
May 30 16:24:54 client kernel: SELinux: policy capability always_check_network=0
May 30 16:24:54 client kernel: SELinux: policy capability cgroup_seclabel=1
May 30 16:24:54 client kernel: SELinux: policy capability nnp_nosuid_transition=1
May 30 16:24:54 client dbus-daemon[1052]: [system] Reloaded configuration
When a domain is marked as permissive, the application should behave as if SELinux is not enabled on the system, making it easier for us to find out whether SELinux really is the cause of a permission issue.
With the same semanage command, we can list the currently defined
permissive domains.
# semanage permissive -l
Builtin Permissive Types
Customized Permissive Types
httpd_t
Another method for listing the custom permissive types (those not marked
as permissive through the distribution) is to use the semodule command
# semodule -l | grep permissive_
permissive_httpd_t
To remove the permissive mode from the domain, pass the -d
argument to the semanage command
# semanage permissive -d httpd_t
libsemanage.semanage_direct_remove_key: Removing last permissive_httpd_t module (no other permissive_httpd_t module exists at another priority).
Disable SELinux Permanently
If you still wish to disable SELinux then you need to modify
SELINUX=enforcing to SELINUX=disabled in /etc/selinux/config
# cat /etc/selinux/config
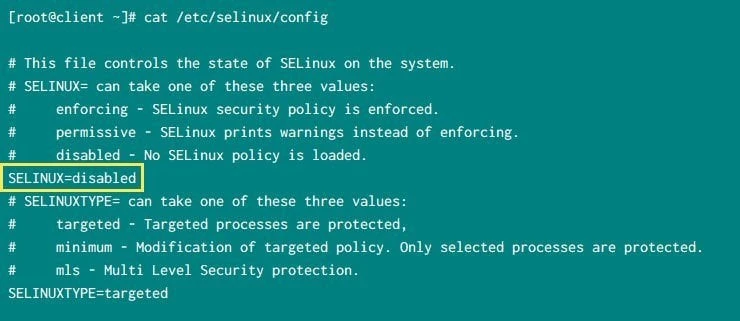
Disable SElinux
If the /etc/selinux/config file is changed, then the system needs to
be rebooted for the changes to take effect. So after modifying this
file go ahead and reboot your server
Post reboot verify the SELinux status
# getenforce
Disabled
Conclusion
In this tutorial we learned that SELinux is an important part of strengthening security of Linux servers. You can instead choose to use SELinux is Permissive mode rather than Disabled state. Or you can also choose to modify individual domain to be in permissive mode rather than making system wide changes.
Lastly I hope the steps from the article to disable SELinux on Linux was helpful. So, let me know your suggestions and feedback using the comment section.
References
I have used below external references for this tutorial guide
SELinux System
Administration
How
to disable SELinux protection for a specific Daemon/Service in Red Hat
Enterprise Linux.







![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_1295ec8cece3ddb1.webp)

