In this tutorial we will configure postfix to use third party GMAIL SMTP
Relay server so that our Linux server will be able to send mail to
external network using smtp.gmail.com
What is SMTP Relay
- SMTP Relay is a protocol that allows an external SMTP server to be used to send emails instead of hosting a local SMTP server.
- This will typically involve using a service such as MailJet, SendGrid or MailGun.
- These services avoid the necessity to configure and maintain your own SMTP server and often provide additional benefits such as analytics.
Lab Environment
I will use RHEL 8 to setup gmail smtp relay server with postfix. You can also use these same steps on CentOS environment.
Hostname: server.example.com
IP Address: 192.168.43.31
Pre-requisites
Disable sendmail
You should have only one MTA on your server, so if we are using postfix it is always recommended to stop the other MTA services.
# rpm -q sendmail
If sendmail is installed on your server then to stop and disable this service use
# systemctl disbale sendmail --now
Configure firewall
Since we are using firewalld we will add a rule using firewalld to allow smtp service
# firewall-cmd --permanent --add-service=smtp
Install Packages
Let's start with the steps to configure postfix with gmail smtp relay server. Install postfix and other dependency packages for SASL authentication
# dnf -y install postfix cyrus-sasl cyrus-sasl-lib cyrus-sasl-plain -y
Configure Postfix
Here I will share the basic and minimal recommended configuration for postfix. I have already explained individual parameters which we use in postfix server, so I will not explain this again here.
Look out for these parameters in your /etc/postfix/main.cf and modify
them according to your environment:
myhostname = server.example.com
mydomain = example.com
myorigin = $mydomain
mydestination = mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain
inet_interfaces = $myhostname, localhost
inet_protocols = ipv4
mynetworks = 192.168.43.0/24, 127.0.0.0/8
smtp_use_tls = yes
smtp_sasl_auth_enable = yes
smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd
smtp_sasl_security_options = noanonymous
smtp_sasl_tls_security_options = noanonymous
smtp_tls_CApath = /etc/pki/tls/certs
smtp_tls_CAfile = /etc/pki/tls/certs/ca-bundle.crt
relayhost param in /etc/postfix/main.cf as
we will define this using sasl_passwd file. Alternatively you can also
add here in main.cf but it will just be at two places.
Configure GMAIL as SMTP relay server
Next we must
setup authentication file,
in this tutorial we will create a new file /etc/postfix/sasl_passwd
and place the relayhost and login authentication related details
# cat /etc/postfix/sasl_passwd
[smtp.gmail.com]:587 :
Replace email-address with your gmail email address such as
[email protected]
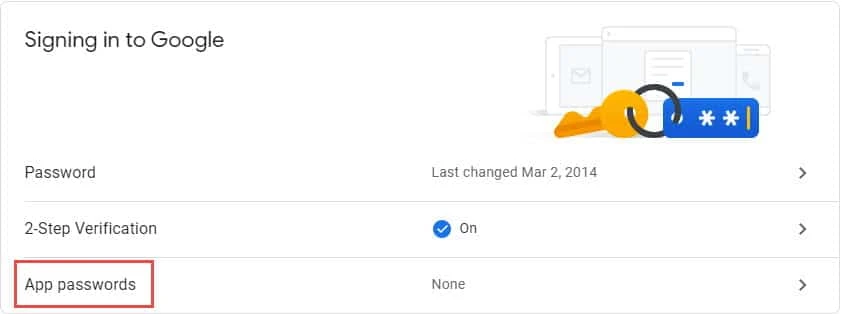
Collect App Password for GMAIL
Follow the below steps to get the app password
Visit https://www.google.com/settings/security using your gmail id which you plan to use for SMTP relay.
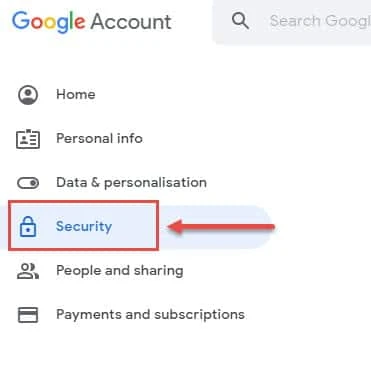
Login using your GMAIL ID, under Google Account click on Security
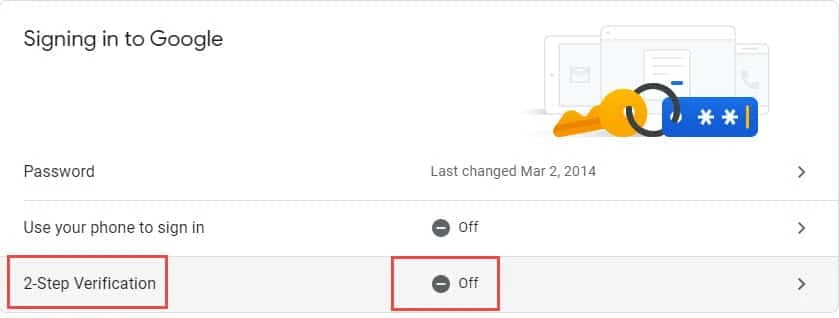
Enable 2-Step Verification (if not done already). We must enable 2-Step verification to be able to generate App Passwords
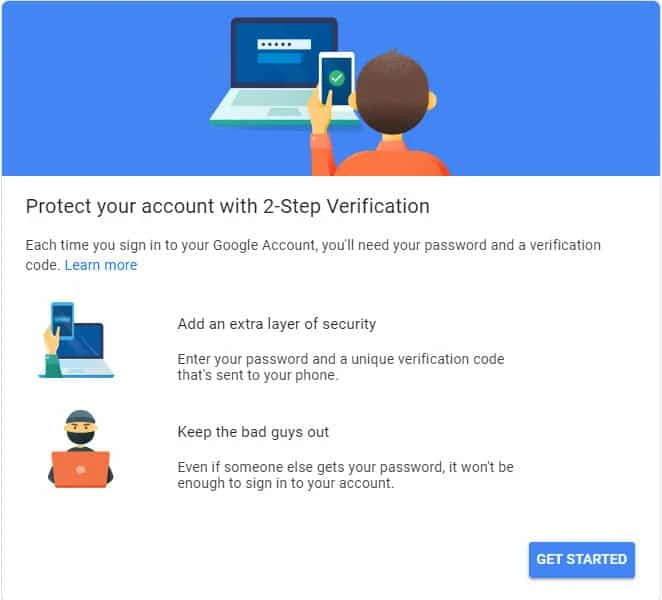
Click on Get Started and follow the on screen guide to complete the process. Due to security reasons, the console may prompt you for password multiple times.
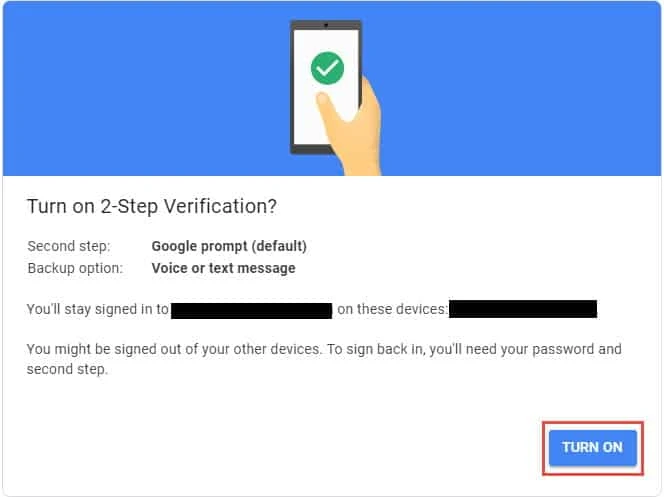
Once all the steps are completed, you will be presented with this screen which should contain details of the device using which you have enabled 2-Step Authentication. You will also have to login using your code sent to your backup device.
Now under Security section, you should get an option to enable App passwords
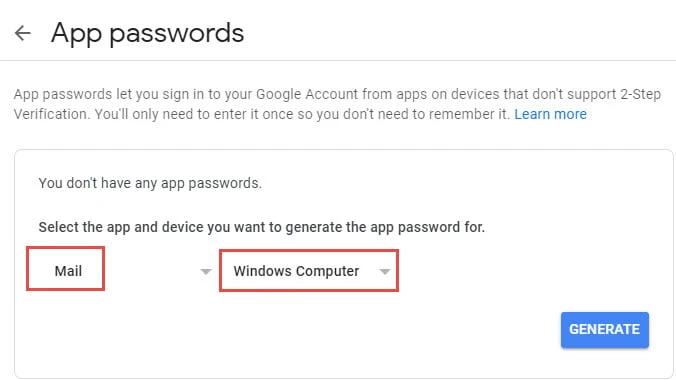
Select App passwords and enable one for Mail. You can define any device here, I have defined Windows Computer
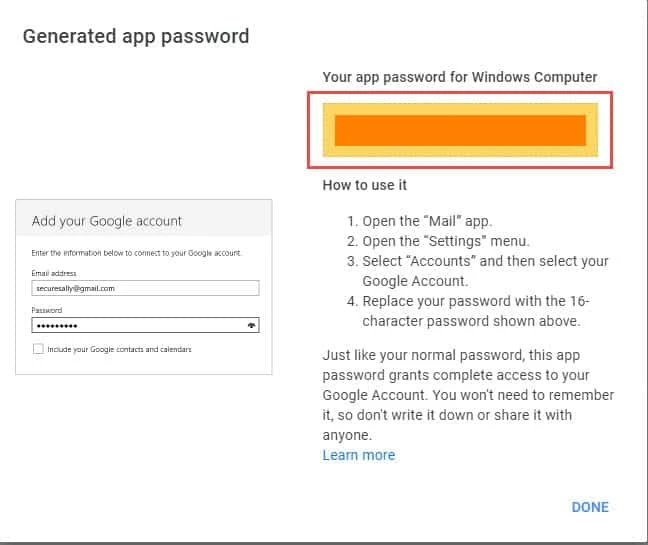
Once you click on GENERATE, in the next screen you will get your app
password which you must put in /etc/postfix/sasl_passwd file along
with your email address
Update the password database
Once you have placed the app password with the password file created,
use the postmap utility to generate the hash database containing the
mail credentials:
# postmap /etc/postfix/sasl_passwd
Before proceeding, take some additional steps to secure your postfix credentials:
# chown root:root /etc/postfix/sasl_passwd /etc/postfix/sasl_passwd.db
# chmod 0600 /etc/postfix/sasl_passwd /etc/postfix/sasl_passwd.db
Next restart the postfix service
# systemctl restart postfix.service
Check the status of postfix.service to make sure it has started successfully with no errors
# systemctl status postfix
● postfix.service - Postfix Mail Transport Agent
Loaded: loaded (/usr/lib/systemd/system/postfix.service; disabled; vendor preset: disabled)
Active: active (running) since Fri 2020-07-31 18:04:05 IST; 22min ago
Process: 3849 ExecStop=/usr/sbin/postfix stop (code=exited, status=0/SUCCESS)
Process: 3868 ExecStart=/usr/sbin/postfix start (code=exited, status=0/SUCCESS)
Process: 3866 ExecStartPre=/usr/libexec/postfix/chroot-update (code=exited, status=0/SUCCESS)
Process: 3863 ExecStartPre=/usr/libexec/postfix/aliasesdb (code=exited, status=0/SUCCESS)
Main PID: 3935 (master)
Tasks: 3 (limit: 26213)
Memory: 6.0M
CGroup: /system.slice/postfix.service
├─3935 /usr/libexec/postfix/master -w
├─3936 pickup -l -t unix -u
└─3937 qmgr -l -t unix -u
Jul 31 18:04:03 server.example.com systemd[1]: Stopped Postfix Mail Transport Agent.
Jul 31 18:04:04 server.example.com systemd[1]: Starting Postfix Mail Transport Agent...
Jul 31 18:04:05 server.example.com postfix/master[3935]: daemon started -- version 3.3.1, configuration /etc/postfix
Jul 31 18:04:05 server.example.com systemd[1]: Started Postfix Mail Transport Agent.
Verify by sending mail to external network
We will use mail client to send mails to external network
# mail [email protected]
Subject: Test Message
hello, how are you!
.
EOT
." (dot) to
end the mail writing and to initiate the send.
Observe the logs /var/log/messages to make sure the mail was sent
successfully. I prefer using
journalctl
to view LIVE runtime messages
Jul 31 18:42:21 server.example.com chronyd[1061]: Selected source 162.159.200.123
Jul 31 18:42:21 server.example.com sendmail[4081]: 06VDCLOr004081: from=root, size=240, class=0, nrcpts=1, msgid=<[email protected]>, relay=root@localhost
Jul 31 18:42:21 server.example.com postfix/smtpd[4074]: connect from localhost[127.0.0.1]
Jul 31 18:42:21 server.example.com sendmail[4081]: STARTTLS=client, relay=[127.0.0.1], version=TLSv1.3, verify=FAIL, cipher=TLS_AES_256_GCM_SHA384, bits=256/256
Jul 31 18:42:21 server.example.com postfix/smtpd[4074]: 8003D20440: client=localhost[127.0.0.1]
Jul 31 18:42:21 server.example.com postfix/cleanup[4078]: 8003D20440: message-id=<[email protected]>
Jul 31 18:42:21 server.example.com postfix/qmgr[4071]: 8003D20440: from=<[email protected]>, size=698, nrcpt=1 (queue active)
Jul 31 18:42:21 server.example.com sendmail[4081]: 06VDCLOr004081: [email protected], ctladdr=root (0/0), delay=00:00:00, xdelay=00:00:00, mailer=relay, pri=30240, relay=[127.0.0.1] [127.0.0.1], dsn=2.0.0, stat=Sent (Ok: queued as 8003D20440)
Jul 31 18:42:21 server.example.com postfix/smtpd[4074]: disconnect from localhost[127.0.0.1] ehlo=2 starttls=1 mail=1 rcpt=1 data=1 quit=1 commands=7
Jul 31 18:42:25 server.example.com postfix/smtp[4079]: 8003D20440: to=<[email protected]>, relay=smtp.gmail.com[74.125.200.109]:587, delay=4.3, delays=0.06/0/3.1/1.2, dsn=2.0.0, status=sent (250 2.0.0 OK 1596201145 lk16sm8543446pjb.13 - gsmtp)
Jul 31 18:42:25 server.example.com postfix/qmgr[4071]: 8003D20440: removed
Check the inbox of [email protected], and we have received the
mail from root
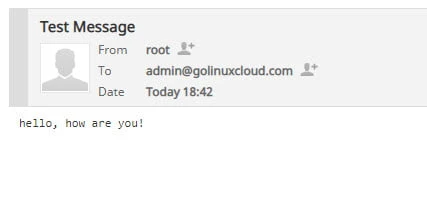
GMAIl SMTP relay Server is Working
Troubleshooting
Error-1: SASL authentication failure: No worthy mechs found
If you are getting this error:
Jul 31 15:31:00 server.example.com postfix/smtp[2466]: warning: SASL authentication failure: No worthy mechs found
Jul 31 15:31:00 server.example.com postfix/smtp[2466]: B2ECA2043E: SASL authentication failed; cannot authenticate to server smtp.gmail.com[74.125.200.108]: no mechanism available
Solution-1:
You must install cyrus-sasl cyrus-sasl-lib and cyrus-sasl-plain on
your postfix server.
Error-2: connect to smtp.gmail.com: Network is unreachable
If you are getting this error
Jul 31 16:36:38 server.example.com postfix/smtp[3275]: connect to smtp.gmail.com[2404:6800:4003:c01::6c]:587: Network is unreachable
Solution-2:
Make sure you are able to ping smtp.gmail.com
# ping smtp.gmail.com
PING smtp.gmail.com (74.125.200.109) 56(84) bytes of data.
64 bytes from sa-in-f109.1e100.net (74.125.200.109): icmp_seq=1 ttl=104 time=191 ms
64 bytes from sa-in-f109.1e100.net (74.125.200.109): icmp_seq=2 ttl=104 time=205 ms
^C
--- smtp.gmail.com ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 11ms
rtt min/avg/max/mdev = 191.053/198.029/205.006/6.990 ms
Next try to connect to smtp server using telnet
# telnet smtp.gmail.com 587
Trying 74.125.200.109...
Connected to smtp.gmail.com.
Escape character is '^]'.
220 smtp.gmail.com ESMTP e8sm9624845pfd.34 - gsmtp
If both of this is working then verify your inet_protocols value in
/etc/postfix/main.cf. Most of the time we put inet_protocols as all
when we are only using IPv4 or Ipv6 in the server so in such scenarios
these messages are expected
Change the value to ipv4 or ipv6 based on your environment
inet_protocols ipv4
Also modify inet_interfaces to all
inet_interfaces all
Error-3: SASL authentication failed; server smtp.gmail.com Username and Password not accepted
If you are getting below error:
Jul 31 16:36:10 server.example.com postfix/smtp[3263]: 712322046F: SASL authentication failed; server smtp.gmail.com[74.125.200.108] said: 535-5.7.8 Username and Password not accepted. Learn more at?535 5.7.8 https://support.google.com/mail/?p=BadCredentials d13sm642986pjz.3 - gsmtp
Solution-3
Make sure 2-Step authentication is enabled in your Gmail account and you
are using App Password for authentication as explained in this
tutorial
You should not use your Gmail account password for authentication
Conclusion
A complete, end-to-end email system consists of a Mail User Agent (MUA), Mail Transfer Agent (MTA), Mail Delivery Agent (MDA) and the SMTP protocol. CentOS 8 provides a number of options in terms of MTA solutions, one of the more popular being Postfix. In this tutorial we configured postfix to act as a mail server and to send and receive email using a third party GMAIL SMTP relay server.



![Convert Decimal to Fraction [7 Programming Languages]](/convert-decimal-to-fraction/convert-decimal-to-fraction_hu_947618e63f2bcbeb.webp)
![Where to set environment variables in Linux? [SOLVED]](/where-to-set-environment-variables-in-linux/set-env-variable_hu_878a57923c42afb8.webp)
![Exclude Users from Match Group in SSHD [SOLVED]](/exclude-users-from-match-group-sshd/exclude-users-matchgroup_hu_60d8fc7c4f68c7f5.webp)
![Add User to Group in Linux Efficiently [5 Methods]](/add-user-to-group-in-linux/add-user-to-group-linux_hu_c42f8254ff8ea14f.webp)
![How to PROPERLY delay reboot in Linux? [5 Methods]](/delay-reboot-in-linux/delay-reboot_hu_72714dbb333ab303.webp)
![Linux File Descriptors [In-Depth Tutorial]](/linux-file-descriptors/file-descriptors-1_hu_665cd0f292f2ecd.webp)
![How to Edit a File in Linux? [SOLVED]](/linux-how-to-edit-a-file/linux-edit-file_hu_56790211bb4240e6.webp)
![How to ignore certificate check in wget? [SOLVED]](/wget-ignore-certificate-error/wget-ignore-cert-check_hu_642b675c53189fd2.webp)