Recently a friend of mine contacted me and asked if I could help him to make sure if their web application was blocked by one of their Internet Service Providers (ISP) or not. He is working for a global company that located in multiple continents and countries across the world. They provide services from the headquarter to the branches and had a connectivity issue from a specific country. After investigating network trace (pcap) file captured from the client side, we indeed found the ISP was blocking the connections with Deep Packet Inspection (DPI).
Different methods to block website via ISP
In this article, we will explore the common blocking methods used by ISPs and how to find a workaround. ISPs around the world are blocking access to websites for variety reasons. Most commonly, they block them due to local policy, local laws and internet censorship. They extensively use the methods below.
Method-1: DNS Blocking
Domain Name System (DNS) blocking is one of the most common methods used by ISPs to filter internet users’ traffic. For better understanding, let’s assume a user would like to reach www.dw.com news portal without knowing it is blocked by the local ISP. Following figure shows the network topology.
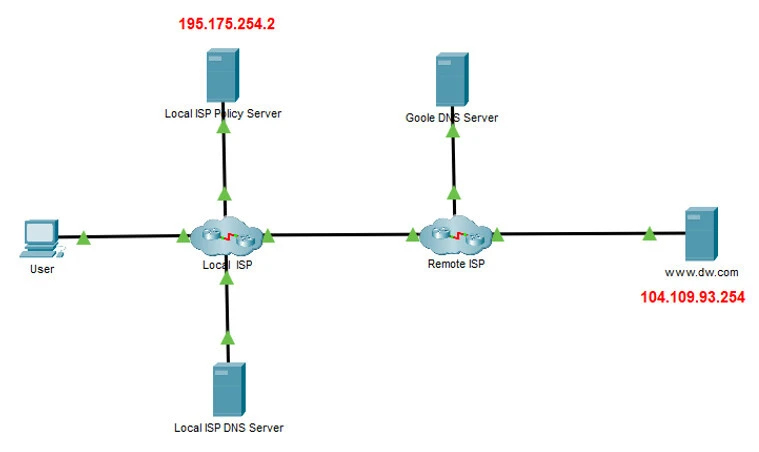
The user has two options for dealing with name resolution: Using the local ISP DNS server or using a third-party DNS server. When the user picks the first one, the requests will follow the steps below.
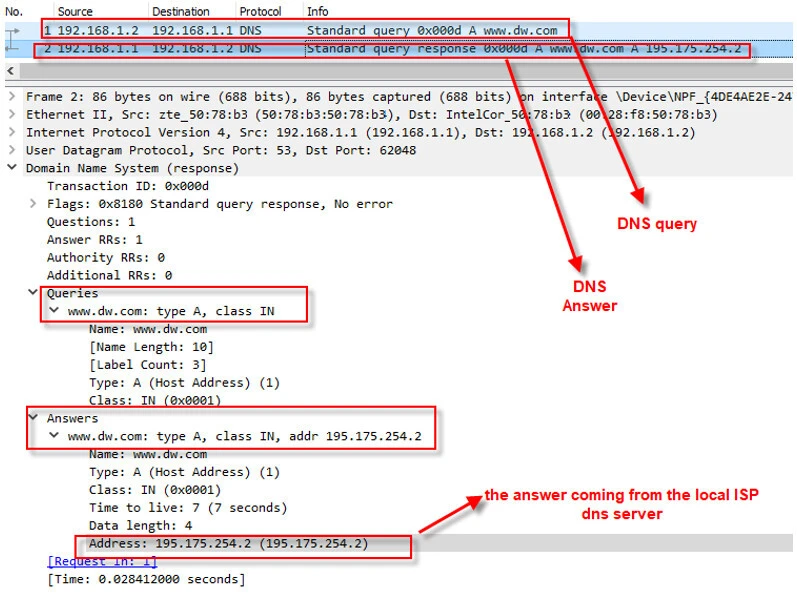
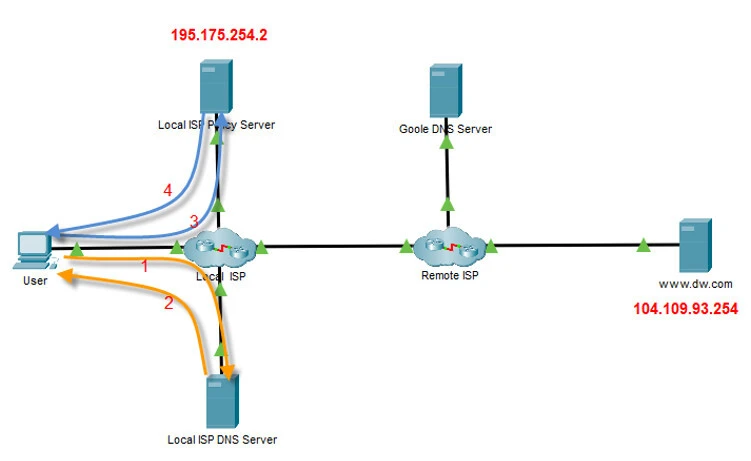
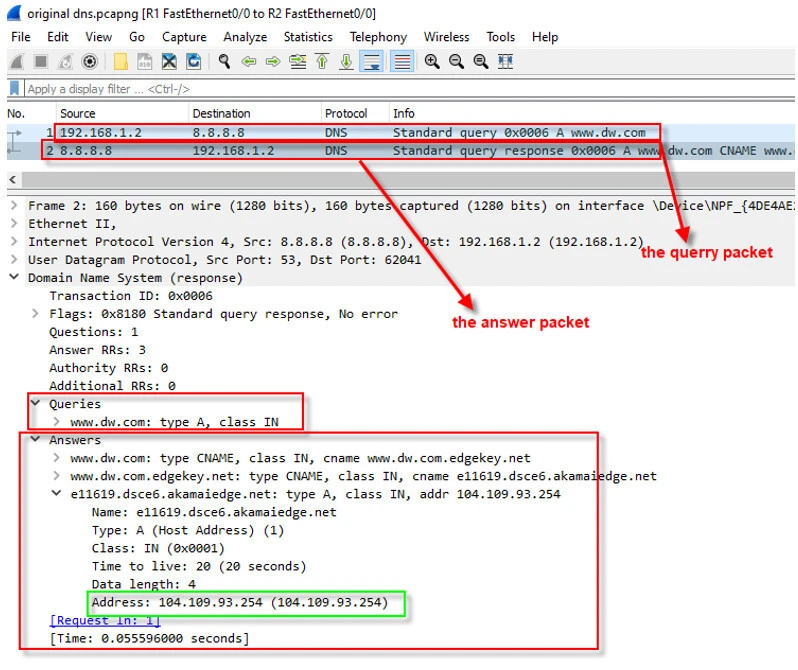
First, the user needs to resolve the IP address for www.dw.com and to achieve that, it sends a DNS query to the local ISP DNS server, before initiating a TCP connection to the www.dw.com server. The DNS server checks if the domain name ( www.dw.com) is in the blocked list and if it is so, then it will send an answer with IP address of policy server (195.175.254.2) instead the original web site IP address (104.109.93.254). Below figure shows the packet capture for the DNS request and response.
Once resolving the domain name into the IP address, the user starts a TCP 3-way handshaking with the local policy server and then sends a HTTP or HTTPS request. The server behavior changes depending on the protocol used (HTTP/HTTPS). When the request is made with HTTP, the server informs the user why he can not access that web server, showing him a law referenced message. In case of HTTPS, the policy server can not proof that it is the original web site ( www.dw.com) and due to this reason, it resets the TCP connection. All the steps, from domain name resolution to the HTTP/HTTPS request and response, are summarized below.
One of the ways to verify if your web site is blocked through DNS blocking method, you can use a third-party DNS server for name resolution and compare both of the name resolution result for the domain. If you resolve to different IP addresses, then there is a big chance you are being blocked by your ISP. nslookup, which is a command-line tool in both Windows and Linux, can be used to query a DNS server for the comparison like below.
Step-1: Open a command prompt or shell and type nslookup. To
query a different DNS server, type “server 8.8.8.8” and then type the
domain name.

Step-2: After initiation of the query, the DNS packets will follow the path below.
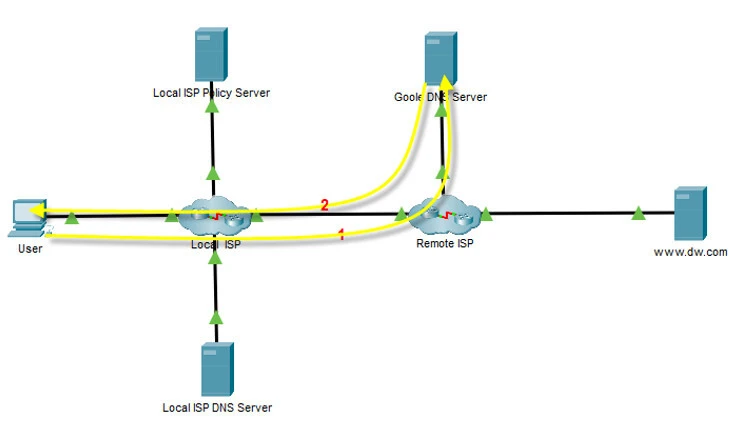
As seen below, the answer coming from google DNS server (8.8.8.8) is
different from previous DNS resolution, which indicates that the ISP is
blocking the web site.
You can also do the IP address comparison using platforms like ping.eu ( https://ping.eu/nslookup/). However, comparison of IP addresses can not be used when the web site uses a dynamic or constantly changed IP address. After figuring out the web site is blocked, changing the DNS server let you bypass DNS blocking. There are also some other methods (DNS over HTTPS (DoH), DNS over TLS (DoT) and using a VPN) which will not be covered in this article because they will make the article huge.
Method-2: IP Blocking
An ISP may block users accessing certain IP addresses, which is not common due to extensive usage of Content Delivery Network (CDN). With CDN, web sites IP addresses change dynamically which led ISPs to block irrelevant IP addresses. In addition to that, an IP address can be used by many web sites, which make it impossible to block it. However, it is still an option for ISPs. Routers and Firewalls can be used to block the traffic. Some of these devices can notify users about being blocked. As seen in the screenshot below, after resolving the domain name, the user initiates a TCP connection then the packet gets blocked by ISP. After that the user is informed with a special ICMP packet (Type 3, Code 13), which specifies the communication is blocked.
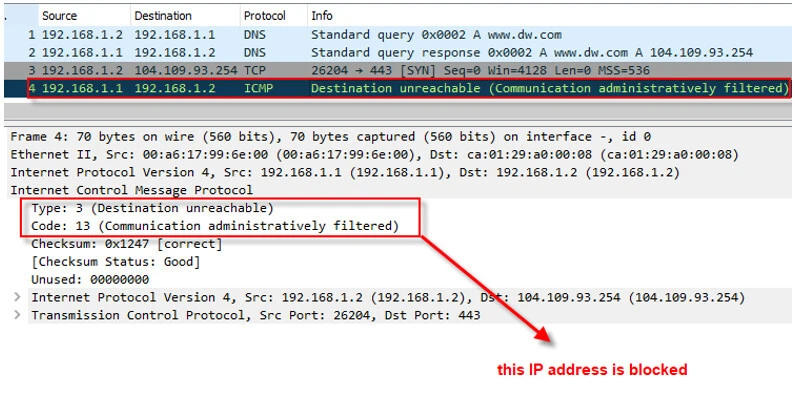
However, most of times ISPs do not inform the user like below. The user keeps retransmitting again and again until the connection times out.

Using a VPN or a proxy can get you around the restriction.
Deep Packet Inspection to check if ISP is blocking website
Deep packet inspection (DPI) is a method that allows a service provider to analyze network traffic. With DPI, ISPs can obtain many useful information and block web sites using this information. This is one of the most common methods used by them for filtering. Unlike IP blocking, this time the data in the application layer and TLS handshaking are used to find the web site to be blocked.
Imagine a user would like to access www.dw.com with using HTTP. Once finishing resolving the domain name and completing TCP 3-way handshaking, the user sends a HTTP GET request as below.
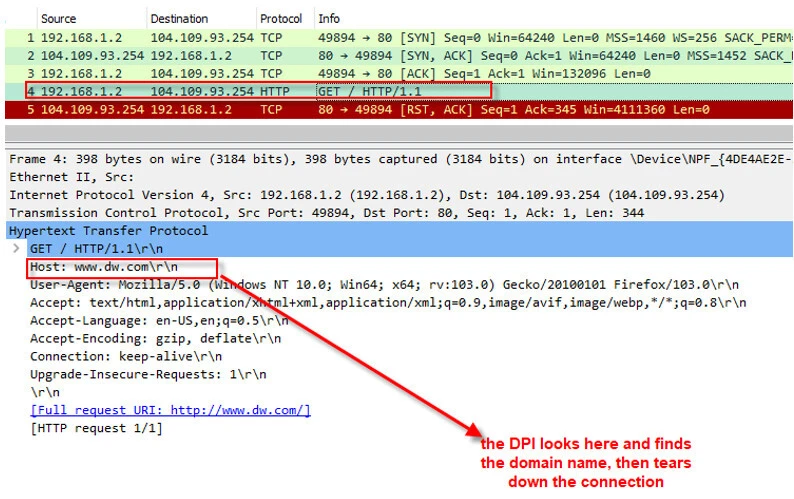
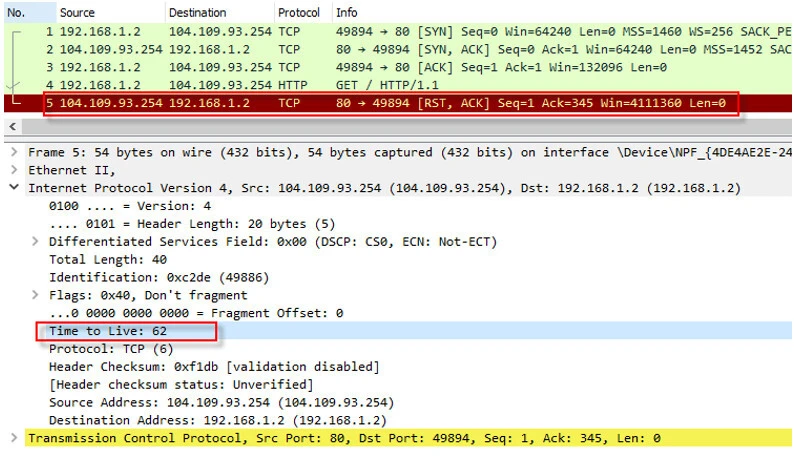
As the DPI receives this packet, it analyzes the HTTP header and checks if the “Host” field is in the blocked list. If it finds it in the blocked list, the connection gets finished with a packet in which TCP RST (Reset) flag is set. Sometimes we may get this packet from the web server due to many reasons. To make sure the RST packet is coming from the DPI (ISP), we need to check the packet TTL value in the IP header to find the distance between the user and the node that sent the RST packet. Following figure shows the details of the RST packet, which has TTL of 62.
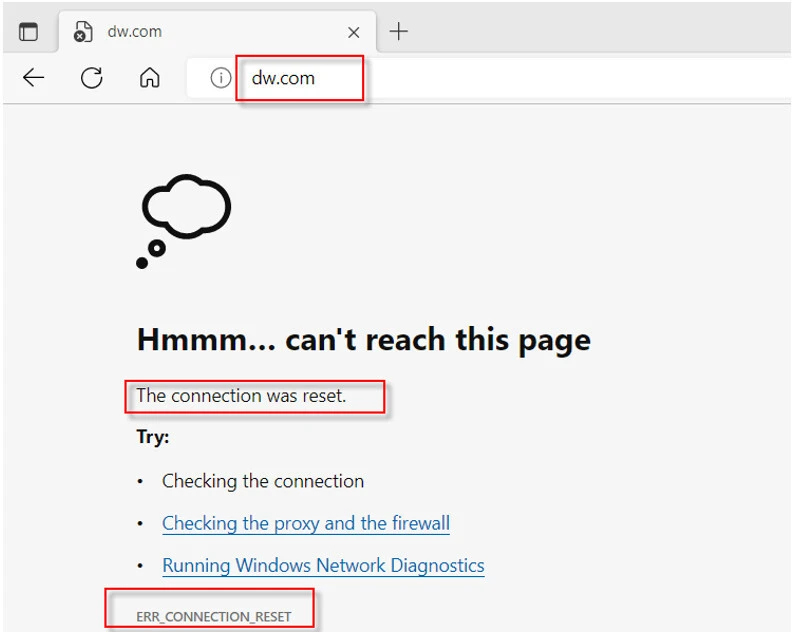
Edge browser shows the user the screenshot below during the blocking.
Most operating systems use an initial TTL value of 32, 64, 128, or 255. As seen in the packet the TTL value is 62, which strongly indicates that the RST packet is coming from 2 hops away (64-62=2). Since ww.dw.com can not be 2 hops away from the user, we can say that RST packet is coming from the ISP.
It is easy for DPI to analyze clear text protocols, but what about a protocol like HTTPS, through which the data is encrypted? Even if content of the request is encrypted, DPI is still able to get the domain name through Server Name Indication (SNI) field in the TLS Client Hello packet. This field is an extension for the TLS protocol to indicate a hostname in the TLS handshake. During DPI inspection, this field is checked to find the site to be blocked. Following screenshot shows a connection gets tore down.
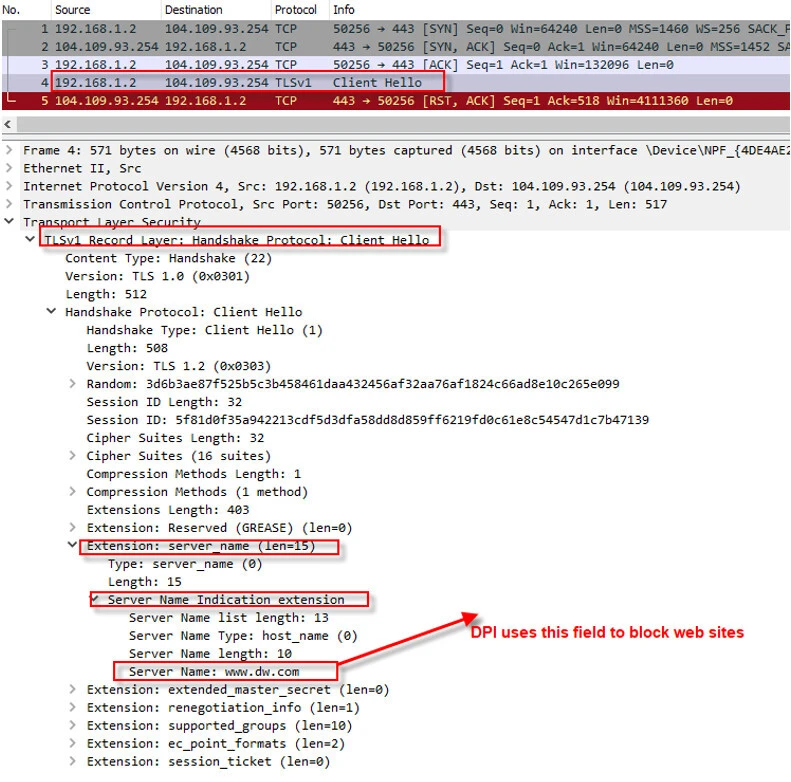
Firefox browser shows the user the screenshot below during the blocking.
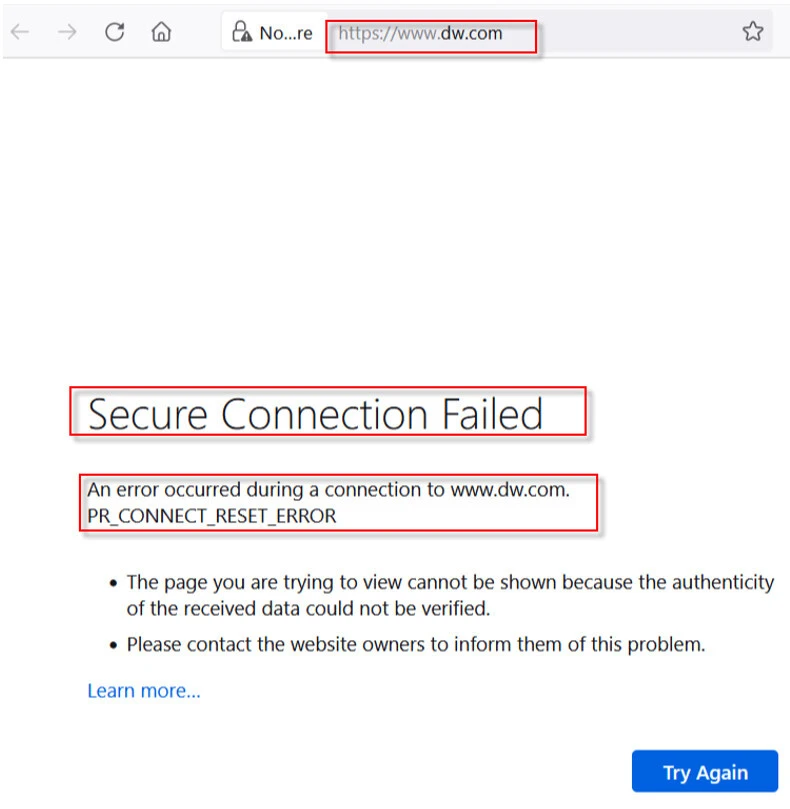
TLS have to use SNI when the IP address is shared between multiple web sites. As result of this, DPI is able to block HTTPS traffic as well. A VPN or proxy can let user to bypass the restriction.
Final Thoughts
In this article, we mostly focused on how to find if a web site is blocked or not via ISP. Most of times connections get dropped with a TCP RST packet. Finding the distance of the node sending this packet can reveal the source of the problem.
References
https://serverfault.com/questions/752123/how-does-an-isp-block-my-website-with-a-warning-message

![How to check if ISP is blocking website [Wireshark]](/how-to-check-if-isp-is-blocking-website/debug_blocked_website_wireshark-800w.webp)

![15 Top Wireshark IP Filters with Examples [Cheat Sheet]](/wireshark-ip-filters-cheat-sheet/wireshark-ip-filters_hu_a5537ce5e5966e33.webp)

