In my earlier article I had shared the
steps to install and configure FreeIPA Server in CentOS/RHEL 7. Now in this article I will share the steps to install and configure FreeIPA server in RHEL 8 and/or
CentOS 8. Now with RHEL 8 openldap-servers has been
deprecated also the ipa-server rpm is not available any
more. So the rpms to install and configure FreeIPA server in RHEL 8 has
changed which we will discuss in depth in this article.
FreeIPA is a way to create identity stores, centralized authentication, domain control for Kerberos and DNS services, and authorization policies all on Linux systems, using native Linux tools. While centralized identity/policy/authorization software is hardly new, FreeIPA is one of the only options that supports Linux/Unix domains. IPA stands for Identity,Policy andAuthentication.
FreeIPA v. LDAP: A More Focused Type of Service
At the most basic level, FreeIPA is a domain controller for Linux and Unix machines. FreeIPA defines the domain, using controlling servers and enrolled client machines. This provides centralized structure that has previously been unavailable to Linux/Unix environments, and it does it using native Linux applications and protocols.
FreeIPA does three things:
- Create a Linux-based and Linux-controlled domain. Both FreeIPA servers and FreeIPA clients are Linux or Unix machines. While FreeIPA can synchronize data with an Active Directory domain to allow integration with Windows servers, it is not an administrative tools for Windows machines and it does not support Windows clients. FreeIPA is a management tool for Linux domains.
- Centralize identity management and identity policies.
- Build on existing, native Linux applications and protocols. While FreeIPA has its own processes and configuration, its underlying technologies are familiar and trusted by Linux administrators and are well established on Linux systems.
Identity Management (FreeIPA) servers
- Identity Management servers are Red Hat Enterprise Linux systems that work as domain controllers (DCs). In most deployments, an integrated certificate authority (CA) is also installed with the IdM server.
- Servers are the central repositories for identity and policy information. They also host the services used by domain members.
Identity Management (FreeIPA) clients
- Identity Management clients are Red Hat Enterprise Linux systems enrolled with the servers and configured to use the Identity Management services on these servers.
- Clients interact with the Identity Management servers to access services provided by them. For example, clients use the Kerberos protocol to perform authentication and acquire tickets for enterprise SSO, use LDAP to get identity and policy infromation, use DNS to detect where the servers and services are located and how to connect to them.
- Identity Management servers are also embedded Identity Management clients. As clients enrolled with themselves, the servers provide the same functionality as other clients.
Pre-requisites to configure FreeIPA server in RHEL 8
Before you install and configure FreeIPA server in RHEL 8, ensure that the installation environment is suitably configured. You also need to provide certain information during the installation and configuration procedures, including realm names and certain usernames and passwords.
Hardware Recommendations
A basic user entry or a simple host entry with a certificate is approximately 5-10 kB in size, as is a simple host entry with a certificate. The most important hardware feature to size properly is RAM. While all deployments are different, depending on the number of users and groups and the type of data stored, there is a rule of thumb to use to help determine how much RAM to use:
- For 10,000 users and 100 groups: at least 3 GB of RAM and 1 GB swap space
- For 100,000 users and 50,000 groups: at least 16 GB of RAM and 4 GB of swap space
Verify the server host name
To configure freeipa server in RHEL 8, the host name must be a fully qualified domain name, such as server.example.com.
To verify the host name, use the hostname utility on the system where you want to install:
# hostname
ipa-server.example.com
The output of hostname must not be localhost or localhost6.
Below is an example of /etc/hosts file
[root@ipa-server ~]# cat /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
10.0.2.20 ipa-server.example.com ipa-server
Firewalld Configuration
It is important to open important ports before you configure FreeIPA Server in RHEL 8.
| Service | Ports | Protocol |
|---|---|---|
| HTTP/HTTPS | 80,443 | TCP |
| LDAP/LDAPS | 389,636 | TCP |
| Kerberos | 88,464 | TCP and UDP |
| DNS | 53 | TCP and UDP (optional) |
| NTP | 123 | UDP (optional) |
Add the firewalld services to the firewall by using the
firewall-cmd --add-service command. For example, to open the ports in
the default zone:
# firewall-cmd --permanent --add-service={freeipa-ldap,freeipa-ldaps,dns}
Reload the firewall-cmd configuration to ensure that the change takes
place immediately:
# firewall-cmd --reload
Install RPMs required to configure FreeIPA Server in RHEL 8
The packages required to install and configure FreeIPA server in RHEL 8 are shipped as a module. The IdM server module stream is called the DL1 stream, and you need to enable this stream before downloading packages from this stream.
[root@ipa-server ~]# yum module enable idm:DL1
Switching module streams does not alter installed packages
Switch to the RPMs delivered through the idm:DL1 stream:
[root@ipa-server ~]# yum distro-sync
Updating Subscription Management repositories.
Last metadata expiration check: 0:00:24 ago on Thu 26 Sep 2019 12:40:03 PM IST.
Dependencies resolved.
================================================================================================
Package Arch Version Repository Size
================================================================================================
Installing:
kernel-core x86_64 4.18.0-80.11.2.el8_0 ipa-server-for-x86_64-baseos-rpms 24 M
kernel x86_64 4.18.0-80.11.2.el8_0 ipa-server-for-x86_64-baseos-rpms 424 k
kernel-modules x86_64 4.18.0-80.11.2.el8_0 ipa-server-for-x86_64-baseos-rpms 20 M
<Output trimmed>
Installed:
kernel-core-4.18.0-80.11.2.el8_0.x86_64 kernel-4.18.0-80.11.2.el8_0.x86_64
kernel-modules-4.18.0-80.11.2.el8_0.x86_64 grub2-tools-efi-1:2.02-66.el8_0.1.x86_64
Removed:
kernel-4.18.0-80.el8.x86_64 kernel-core-4.18.0-80.el8.x86_64
kernel-modules-4.18.0-80.el8.x86_64
Complete!
If a new kernel was installed in the above step then it is a good idea to reboot the node to activate the new kernel. You can also check the next kernel version will will be loaded post reboot
[root@ipa-server ~]# reboot
To download the packages necessary to install and configure FreeIPA Server in RHEL 8 with Integrated DNS follow the below steps:
To download the packages necessary install and configure FreeIPA Server in RHEL 8 without an integrated DNS:
[root@ipa-server ~]# yum module install idm:DL1/server
[root@ipa-server ~]# yum module install idm:DL1/dns
Updating Subscription Management repositories.
Last metadata expiration check: 0:16:42 ago on Thu 26 Sep 2019 12:40:03 PM IST.
Dependencies resolved.
================================================================================================
Package Arch Version Repository Size
================================================================================================
Installing group/module packages:
ipa-server-dns noarch 4.7.1-11.module+el8+2842+7481110c
ipa-server-for-x86_64-appstream-rpms 177 k
Installing dependencies:
ldns x86_64 1.7.0-20.el8 ipa-server-for-x86_64-appstream-rpms 165 k
bind-dyndb-ldap x86_64 11.1-13.module+el8+2555+b334d87b
ipa-server-for-x86_64-appstream-rpms 130 k
opendnssec x86_64 1.4.14-1.module+el8+2555+b334d87b
ipa-server-for-x86_64-appstream-rpms 468 k
bind x86_64 32:9.11.4-17.P2.el8_0.1 ipa-server-for-x86_64-appstream-rpms 2.1 M
bind-pkcs11-utils x86_64 32:9.11.4-17.P2.el8_0.1 ipa-server-for-x86_64-appstream-rpms 225 k
bind-pkcs11-libs x86_64 32:9.11.4-17.P2.el8_0.1 ipa-server-for-x86_64-appstream-rpms 1.1 M
bind-pkcs11 x86_64 32:9.11.4-17.P2.el8_0.1 ipa-server-for-x86_64-appstream-rpms 378 k
<Output Trimmed>
Installed:
ipa-server-dns-4.7.1-11.module+el8+2842+7481110c.noarch
ldns-1.7.0-20.el8.x86_64
bind-dyndb-ldap-11.1-13.module+el8+2555+b334d87b.x86_64
opendnssec-1.4.14-1.module+el8+2555+b334d87b.x86_64
bind-32:9.11.4-17.P2.el8_0.1.x86_64
bind-pkcs11-utils-32:9.11.4-17.P2.el8_0.1.x86_64
bind-pkcs11-libs-32:9.11.4-17.P2.el8_0.1.x86_64
bind-pkcs11-32:9.11.4-17.P2.el8_0.1.x86_64
libitm-8.2.1-3.5.el8.x86_64
opencryptoki-3.10.0-3.el8.x86_64
opencryptoki-libs-3.10.0-3.el8.x86_64
sqlite-3.26.0-3.el8.x86_64
opencryptoki-icsftok-3.10.0-3.el8.x86_64
Complete!
Install & Configure FreeIPA Server in RHEL 8 with Integrated DNS and CA Certificate
The FreeIPA setup script creates a server instance, which includes configuring all of the required services for the FreeIPA domain:
- The network time daemon (ntpd)
- A 389 Directory Server instance
- A Kerberos key distribution center (KDC)
- Apache (httpd)
- An updated SELinux targeted policy
- The Active Directory WinSync plug-in
- A certificate authority
- Optional. A domain name service (DNS) server
To configure FreeIPA server in RHEL 8, execute ipa-server-install
script from the terminal. This script can accept user-defined settings
for services, like DNS and Kerberos, that are used by the FreeIPA
instance, or it can supply predefined values for minimal input from the
administrator.
[root@ipa-server ~]# ipa-server-install --allow-zone-overlap
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.7.1
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Do you want to configure integrated DNS (BIND)? [no]: yes
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
.
Example: master.example.com.
Server host name [ipa-server.example.com]:
Warning: skipping DNS resolution of host ipa-server.example.com
The domain name has been determined based on the host name.
Please confirm the domain name [example.com]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [EXAMPLE.COM]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Checking DNS domain example.com., please wait ...
DNS zone example.com. already exists in DNS and is handled by server(s): a.iana-servers.net., b.iana-servers.net. Please make sure that the domain is properly delegated to this IPA server.
Invalid IP address fe80::a00:27ff:fe26:9186 for ipa-server.example.com: cannot use link-local IP address fe80::a00:27ff:fe26:9186
Do you want to configure DNS forwarders? [yes]:
Following DNS servers are configured in /etc/resolv.conf: 8.8.8.8
Do you want to configure these servers as DNS forwarders? [yes]:
All DNS servers from /etc/resolv.conf were added. You can enter additional addresses now:
Enter an IP address for a DNS forwarder, or press Enter to skip:
Checking DNS forwarders, please wait ...
Do you want to search for missing reverse zones? [yes]:
Do you want to create reverse zone for IP 10.0.2.20 [yes]:
Please specify the reverse zone name [2.0.10.in-addr.arpa.]:
Using reverse zone(s) 2.0.10.in-addr.arpa.
The IPA Master Server will be configured with:
Hostname: ipa-server.example.com
IP address(es): 10.0.2.20
Domain name: example.com
Realm name: EXAMPLE.COM
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=EXAMPLE.COM
Subject base: O=EXAMPLE.COM
Chaining: self-signed
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 8.8.8.8
Forward policy: only
Reverse zone(s): 2.0.10.in-addr.arpa.
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Adding [10.0.2.20 ipa-server.example.com] to your /etc/hosts file
Synchronizing time
No SRV records of NTP servers found and no NTP server or pool address was provided.
Using default chrony configuration.
Attempting to sync time with chronyc.
Time synchronization was successful.
Configuring directory server (dirsrv). Estimated time: 30 seconds
<Output Trimmed>
Configured sudoers in /etc/nsswitch.conf
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
WARNING: The configuration pre-client installation is not managed by authselect and cannot be backed up. Uninstallation may not be able to revert to the original state.
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Configuring example.com as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificates stored in /root/cacert.p12
These files are required to create replicas. The password for these
files is the Directory Manager password
The ipa-server-install command was successful
This should configure FreeIPA server in RHEL 8 for you, Next verify your DNS zone configuration and record entries
[root@ipa-server ~]# dig +short ipa-server.example.com A
10.0.2.20
[root@ipa-server ~]# dig +short -x 10.0.2.20
ipa-server.example.com.
Authenticate to the Kerberos realm using the admin user's credentials to ensure that the user is properly configured and the Kerberos realm is accessible.
[root@ipa-server ~]# kinit admin
Password for [email protected]:
Use the klist command to verify the identity and the ticket granting
ticket (TGT) from the server:
[root@ipa-server ~]# klist
Ticket cache: KCM:0
Default principal: [email protected]
Valid starting Expires Service principal
09/26/2019 17:07:22 09/27/2019 17:07:18 krbtgt/[email protected]
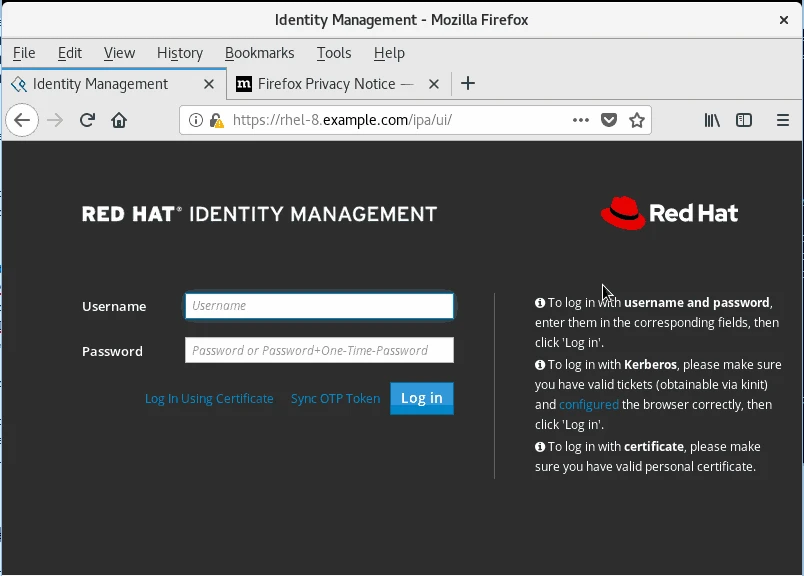
Access WebGUI of IPA Server
Once you successfully install and configure FreeIPA server in RHEL 8,you can also use the UI to access the IPA server. In order to use the web UI, the user must be authenticated with the FreeIPA Kerberos domain and have an active Kerberos ticket. Generally, the web UI can only be accessed from a FreeIPA server or client machine and the user must be locally authenticated. There are a couple of ways to work around this, either by configuring Kerberos on a non-domain machine to connect to the Kerberos domain or by password authentication to the UI.
To open the web UI:
- Get a valid Kerberos ticket using kinit
- Open the FreeIPA URL. The full URL is
https://IPAserver-FQDN/ipa/ui, but this service is also accessed simply by openinghttps://IPAserver-FQDN.
Sample screenshot:
Setting up system as FreeIPA Clients
Once you finish configure FreeIPA server in RHEL 8, proceed with setting up client nodes. Below are the set of tasks performed in the background while integrating a system as a client to FreeIPA server
- Retrieve the CA certificate for the FreeIPA CA.
- Create a separate Kerberos configuration to test the provided credentials. This enables a Kerberos connection to the FreeIPA XML-RPC server, necessary to join the FreeIPA client to the
- FreeIPA domain. This Kerberos configuration is ultimately discarded.
- Setting up the Kerberos configuration includes specifying the realm and domain details, and default ticket attributes. Forwardable tickets are configured by default, which facilitates
- connection to the administration interface from any operating system, and also provides for auditing of administration operations.
- Run the
ipa-joincommand to perform the actual join - Obtain a service principal for the host service and installs it into
/etc/krb5.keytab. For example,host/[email protected]. - Enable certmonger, retrieve an SSL server certificate, and install the certificate in /etc/pki/nssdb.
- Disable the nscd daemon.
- Configures SSSD or LDAP/KRB5, including NSS and PAM configuration files.
- Configures an OpenSSH server and client, as well as enabling the host to create DNS SSHFP records.
- Configure NTP.
Prerequisites
Ensure you have the credentials of a user authorized to enroll clients
into the Identity Management domain. This could be, for example, a
hostadmin user with the Enrollment Administrator role. We will use the
IPA admin credential for this purpose.
Update the DNS of IPA Server on the client node under /etc/resolv.conf
[root@ipa-client ~]# grep DNS /etc/sysconfig/network-scripts/ifcfg-enp0s3
DNS1=10.0.2.20
[root@ipa-client ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search example.com
nameserver 10.0.2.20
Restart the network services
[root@ipa-client ~]# systemctl restart network
Packages required to install an Identity Management client
In RHEL8, the packages necessary for installing an Identity Management client are shipped as a module. Two IdM streams provide IdM client packages:
- the
idm:clientstream - the
idm:DL1stream
Installing ipa-client packages from the idm:client stream
To download the packages necessary for installing an IdM client:
[root@ipa-client ~]# yum module install idm
Installing ipa-client packages from the idm:DL1 stream
To switch to the RPMs delivered through the idm:DL1 stream:
[root@ipa-client ~]# yum module enable idm:DL1 -y
Switching module streams does not alter installed packages
[root@ipa-client ~]# yum distro-sync -y
To download the packages necessary for installing an IdM client:
[root@ipa-client ~]# yum module install idm:DL1/client -y
Updating Subscription Management repositories.
Unable to read consumer identity
This system is not registered to Red Hat Subscription Management. You can use subscription-manager to register.
Last metadata expiration check: 0:02:49 ago on Thu 26 Sep 2019 05:09:38 PM IST.
Dependencies resolved.
==========================================================================================================
Package Arch Version Repository Size
==========================================================================================================
Installing group/module packages:
ipa-client x86_64 4.7.1-11.module+el8+2842+7481110c rhel_dvd_appstream 266 k
Installing dependencies:
certmonger x86_64 0.79.6-5.el8 rhel_dvd_appstream 654 k
ipa-client-common noarch 4.7.1-11.module+el8+2842+7481110c rhel_dvd_appstream 169 k
ipa-common noarch 4.7.1-11.module+el8+2842+7481110c rhel_dvd_appstream 725 k
nss-tools x86_64 3.41.0-5.el8 rhel_dvd_appstream 567 k
<Output trimmed>
python3-qrcode-core-5.1-11.module+el8+2555+b334d87b.noarch
python3-yubico-1.3.2-9.module+el8+2555+b334d87b.noarch
autofs-1:5.1.4-29.el8.x86_64
krb5-workstation-1.16.1-22.el8.x86_64
libkadm5-1.16.1-22.el8.x86_64
python3-dns-1.15.0-8.el8.noarch
python3-libipa_hbac-2.0.0-43.el8.x86_64
python3-sss-2.0.0-43.el8.x86_64
python3-sss-murmur-2.0.0-43.el8.x86_64
sssd-tools-2.0.0-43.el8.x86_64
Complete!
Installing an Identity Management client
Run the ipa-client-install utility on the system that you want to
configure as an Identity Management client. The installation script
attempts to obtain all the required settings, such as DNS records,
automatically.
--enable-dns-updates option to update the DNS records with the
IP address of the client system
# ipa-client-install
[root@ipa-client ~]# ipa-client-install
This program will set up IPA client.
Version 4.7.1
Discovery was successful!
Client hostname: ipa-client.example.com
Realm: EXAMPLE.COM
DNS Domain: example.com
IPA Server: ipa-server.example.com
BaseDN: dc=example,dc=com
Continue to configure the system with these values? [no]: yes
Synchronizing time
No SRV records of NTP servers found and no NTP server or pool address was provided.
Using default chrony configuration.
Attempting to sync time with chronyc.
Time synchronization was successful.
User authorized to enroll computers: admin
Password for [email protected]:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=EXAMPLE.COM
Issuer: CN=Certificate Authority,O=EXAMPLE.COM
Valid From: 2019-09-26 11:22:07
Valid Until: 2039-09-26 11:22:07
Enrolled in IPA realm EXAMPLE.COM
Created /etc/ipa/default.conf
Configured sudoers in /etc/nsswitch.conf
Configured /etc/sssd/sssd.conf
Configured /etc/krb5.conf for IPA realm EXAMPLE.COM
Systemwide CA database updated.
Hostname (ipa-client.example.com) does not have A/AAAA record.
Missing reverse record(s) for address(es): 10.0.2.14.
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Configuring example.com as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
Authenticate to the Kerberos realm using the admin user's credentials to ensure that the user is properly configured and the Kerberos realm is accessible.
[root@ipa-client ~]# kinit admin
Password for [email protected]:
Use the klist command to verify the identity and the ticket granting
ticket (TGT) from the server:
[root@ipa-client ~]# klist
Ticket cache: KCM:0
Default principal: [email protected]
Valid starting Expires Service principal
09/26/2019 17:17:38 09/27/2019 17:17:36 krbtgt/[email protected]
Uninstalling an Identity Management client
As an administrator, you can remove an Identity Management client from the environment.
Uninstalling a client removes the client from the Identity Management domain, along with all of the specific Identity Management configuration of system services, such as System Security Services Daemon (SSSD). This restores the previous configuration of the client system.
Run the ipa-client-install --uninstall command:
[root@ipa-client ~]# ipa-client-install --uninstall
Unenrolling client from IPA server
Removing Kerberos service principals from /etc/krb5.keytab
Disabling client Kerberos and LDAP configurations
Redundant SSSD configuration file /etc/sssd/sssd.conf was moved to /etc/sssd/sssd.conf.deleted
Restoring client configuration files
Unconfiguring the NIS domain.
nscd daemon is not installed, skip configuration
nslcd daemon is not installed, skip configuration
Systemwide CA database updated.
Client uninstall complete.
The original nsswitch.conf configuration has been restored.
You may need to restart services or reboot the machine.
Do you want to reboot the machine? [no]: no
The ipa-client-install command was successful
Lastly I hope the steps from the article to install and configure FreeIPA server in RHEL 8 and CentOS8 Linux was helpful. So, let me know your suggestions and feedback using the comment section.
References:
FreeIPA: Identity/Policy Management
Installing Idetity
Management



![Install and Configure OpenLDAP on Ubuntu [Step-By-Step]](/install-and-configure-openldap-on-ubuntu-step-by-step/install_configure_openldap_hu_e82422e1e818b92d.webp)
![OpenLDAP Migration Tutorial [Step-by-Step]](/openldap-migration-examples/openldap-migration_hu_fea6137887e532a5.webp)
![Configure multi-master replication OpenLDAP [Step-by-Step]](/multi-master-replication-openldap/multi-master-openldap_hu_bf0c27a7534cf311.webp)
![Samba Active Directory Setup [Step-by-Step]](/setup-samba-active-directory/samba_dc_hu_441d5c3dab5ff3e7.webp)