How to join RHEL 8 system to an Active Directory server using Samba Winbind. How to authenticate RHEL 8 server against to a Windows 2003 R2 / 2008 / 2008 R2 / 2012 AD domain. How to add CentOS 8 to Windows Domain Controller. Step by Step Guide to add CentOS 8 to Windows Domain Controller. Steps to join RHEL 8 to Active Directory. How to join CentOS 8 to Active Directory on Windows Server. Steps to join CentOS 8 to Windows Domain Controller running on WIndows Server 2012. Steps to join linux to windows active directory.
The winbind service is part of the Samba suite. It enables a Linux server to become a full member in Windows domains and to use Windows users and group accounts in Linux.
Some more articles on similar topic:
- How to join Linux client to Windows AD Domain using realmd with SSSD (CentOS/RHEL 7/8)
- How to join Linux client to Windows AD Domain using adcli with SSSD (CentOS/RHEL 7/8)
- How to join Linux client to Windows AD Domain using winbind (CentOS/RHEL 7/8)
1. An overview of the lab environment
For demonstrations of this article to add CentOS 8 to Windows Domain Controller (Active Directory), we will use virtual machines running in an Oracle VirtualBox installed on my Linux Server virtualization environment.
We have a Microsoft Server 2012R2 Active Directory Domain Controller with the IP address 192.168.0.107, CentOS 8 host with the IP address 192.168.0.117 and RHEL 8 with IP Address 192.168.0.106. In this article I will only cover the part to add CentOS 8 to Windows Domain Controller on the client side. So this article requires a pre-configured Windows Active Directory.
I have only used snippets from my CentOS 8 Server but I have verified the steps on both RHEL 8 and CentOS 8.
2. Preparing the Linux Client to join Windows Active Directory
To add CentOS 8 to Windows Domain Controller, we need to change the DNS settings so that the Active Directory domain DNS server is queried first:
[root@centos-8 ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search www.golinuxcloud.com
nameserver 192.168.0.107
Here 192.168.0.107 is the IP Address of my Windows Active Directory
which is also configured as DNS Server.
To make sure that our server can resolve hostname, either through
queries to the DNS server or to the internal /etc/hosts file, we can
use the getent command.
[root@centos-8 ~]# getent hosts www.golinuxcloud.com
192.168.0.107 www.golinuxcloud.com
3. Install WInbind Package(s)
To add CentOS 8 to Windows Domain Controller we will install the required samba packages on our client host
[root@centos-8 ~]# dnf install samba samba-client samba-winbind samba-winbind-clients oddjob oddjob-mkhomedir
4. Configure Winbind with smb.conf
Configure /etc/samba/smb.conf by replacing the existing content under
[global] section with the following content to add Linux to windows
active directory. Modify the realm and workgroup value as per your
environment.
You can also useRed Hat's AD Integration Helper to help generate optimal configuration values for connecting to your organizations Active Directory.
[global]
workgroup = GOLINUXCLOUD
realm = GOLINUXCLOUD.COM
security = ads
idmap config * : backend = autorid
idmap config * : range = 100000-19999999
idmap config * : rangesize = 1000000
template homedir = /home/%D/%U
template shell = /bin/bash
winbind use default domain = false
winbind offline logon = true
log file = /var/log/samba/log.%m
max log size = 50
log level = 0
security=ads describes the membership in an Active Directory domain.
The parameters idmap* and winbind enum* map Windows users and groups to Unix users and groups.
Usually system users and groups are assigned IDs in the range from 0 to 999, and local users and groups are assigned IDs starting from 1000. With this in mind, it seems pretty reasonable to start assigning IDs to domain users and groups starting from 1000000. We should also differentiate between the domain users and groups and the local built-in accounts existing on a member server, such as the local administrator, the local guest, and so on. These two groups must not overlap, so we assign the range 1000000 to 19999999 to domain built-in user and group accounts
Run the following command to verify that you can resolve the standard SRV records:
[root@centos8 ~]# host -t SRV _kerberos._udp.golinuxcloud.com.
_kerberos._udp.golinuxcloud.com has SRV record 0 100 88 win-71humtros3m.golinuxcloud.com.
[root@centos8 ~]# host -t SRV _ldap._tcp.golinuxcloud.com.
_ldap._tcp.golinuxcloud.com has SRV record 0 100 389 win-71humtros3m.golinuxcloud.com.
Stop the winbind service if it is in running state:
[root@centos8 ~]# systemctl stop winbind
5. Join/Add CentOS 8 to Windows Domain Controller
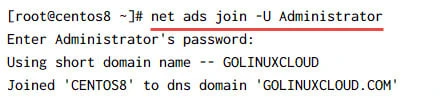
We join the Linux client with Windows Active Directory by executing
net ads join -U Administrator on the client host:
It is possible that you may get the following ERROR while joining Linux client to Windows AD using Samba Winbind.
Joined 'centos-8' to dns domain 'GOLINUXCLOUD.COM'
DNS Update for centos-8.golinuxcloud.com failed: ERROR_DNS_UPDATE_FAILED
DNS update failed: NT_STATUS_UNSUCCESSFUL
5.1 How to fix "DNS Update for DOMAIN failed. ERROR_DNS_UPDATE_FAILED"?
You can either choose to avoid doing any DNS updates while you add CentOS 8 to Windows Domain Controller by using
# net ads join -U Administrator --no-dns-updates www.golinuxcloud.com
Or to fix ERROR_DNS_UPDATE_FAILED error observed above, perform the
following steps
Add following information to /etc/hosts.
# echo "127.0.0.1 `hostname` `hostname -a`" >> /etc/hosts
Make sure that the IP address of the DNS server is in
/etc/resolv.conf. The IP address should be the DNS server you want to
update the new DNS 'A' record.
# cat /etc/resolv.conf
search www.golinuxcloud.com
nameserver 192.168.0.107
On your Windows Domain Controller, select "DNS Manager" for your server.
Select your server in the Forward Lookup Zone and right click to open
Properties. Select the Dynamic updates to "Secure only" or
"Nonsecure and secure" on the Windows DNS server.
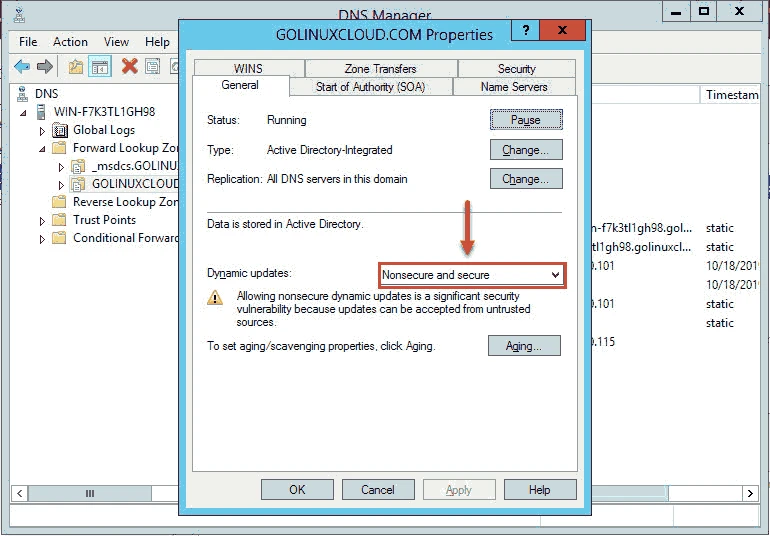
Next restart the DNS service to activate the changes and re-try to add CentOS 8 to Windows Domain Controller
[root@centos-8 ~]# net ads join -U Administrator www.golinuxcloud.com
Enter Administrator's password:
Using short domain name -- GOLINUXCLOUD
Joined 'centos-8' to dns domain 'GOLINUXCLOUD.COM'
6. Verify connectivity between Linux client and Windows AD
We can easily check that the server is a member of the domain with the
testparm command.
[root@centos-8 ~]# testparm
Load smb config files from /etc/samba/smb.conf
Loaded services file OK.
Server role: ROLE_DOMAIN_MEMBER
Press enter to see a dump of your service definitions
# Global parameters
[global]
log file = /var/log/samba/log.%m
max log size = 50
realm = GOLINUXCLOUD.COM
security = ADS
template shell = /bin/bash
winbind offline logon = Yes
workgroup = GOLINUXCLOUD
idmap config * : rangesize = 1000000
idmap config * : range = 100000-19999999
idmap config * : backend = autorid
[homes]
browseable = No
comment = Home Directories
inherit acls = Yes
read only = No
valid users = %S %D%w%S
[printers]
browseable = No
comment = All Printers
create mask = 0600
path = /var/tmp
printable = Yes
[print$]
comment = Printer Drivers
create mask = 0664
directory mask = 0775
force group = @printadmin
path = /var/lib/samba/drivers
write list = @printadmin root
After successfully joining Linux server to Windows Active Directory, it is essential that you restart Winbind and enable the service to auto start at boot:
[root@centos-8 ~]# systemctl enable winbind --now
Created symlink /etc/systemd/system/multi-user.target.wants/winbind.service → /usr/lib/systemd/system/winbind.service.
Check the status of Winbind service
[root@centos-8 ~]# systemctl status winbind
● winbind.service - Samba Winbind Daemon
Loaded: loaded (/usr/lib/systemd/system/winbind.service; enabled; vendor preset: disabled)
Active: active (running) since Fri 2019-10-18 14:48:25 IST; 20s ago
Docs: man:winbindd(8)
man:samba(7)
man:smb.conf(5)
Main PID: 1756 (winbindd)
Status: "winbindd: ready to serve connections..."
Tasks: 2 (limit: 11506)
Memory: 6.6M
CGroup: /system.slice/winbind.service
├─1756 /usr/sbin/winbindd --foreground --no-process-group
└─1758 /usr/sbin/winbindd --foreground --no-process-group
Oct 18 14:48:25 centos-8.golinuxcloud.com systemd[1]: Starting Samba Winbind Daemon...
7. Client Validation
After you add CentOS 8 to Windows Domain Controller it is necessary that you run some checks on the client host i.e. CentOS 8 to make sure it is able to reach Active Directory properly.
You can test whether everything is working properly with wbinfo -t.
The command runs an encrypted RPC call, which is only possible if the
server really is a member in the domain:
[root@centos-8 ~]# wbinfo -t
checking the trust secret for domain GOLINUXCLOUD via RPC calls succeeded
List AD users.
[root@centos-8 ~]# wbinfo -u
GOLINUXCLOUD\administrator
GOLINUXCLOUD\guest
GOLINUXCLOUD\krbtgt
List AD groups.
[root@centos-8 ~]# wbinfo -g
GOLINUXCLOUD\winrmremotewmiusers__
GOLINUXCLOUD\domain computers
GOLINUXCLOUD\domain controllers
GOLINUXCLOUD\schema admins
GOLINUXCLOUD\enterprise admins
GOLINUXCLOUD\cert publishers
GOLINUXCLOUD\domain admins
GOLINUXCLOUD\domain users
GOLINUXCLOUD\domain guests
GOLINUXCLOUD\group policy creator owners
GOLINUXCLOUD\ras and ias servers
GOLINUXCLOUD\allowed rodc password replication group
GOLINUXCLOUD\denied rodc password replication group
GOLINUXCLOUD\read-only domain controllers
GOLINUXCLOUD\enterprise read-only domain controllers
GOLINUXCLOUD\cloneable domain controllers
GOLINUXCLOUD\protected users
GOLINUXCLOUD\dnsadmins
GOLINUXCLOUD\dnsupdateproxy
8. Configure the NSS and PAM stack for authentication
Execute the following command to configure NSS and PAM stack. We use
with-mkhomedir to make sure the home directory for active directory
users are automatically created when they login.
[root@centos8 ~]# authselect select winbind with-mkhomedir --force
Backup stored at /var/lib/authselect/backups/2021-03-03-19-16-20.jS4CgG
Profile "winbind" was selected.
The following nsswitch maps are overwritten by the profile:
- passwd
- group
Make sure that winbind service is configured and enabled. See winbind documentation for more information.
- with-mkhomedir is selected, make sure pam_oddjob_mkhomedir module
is present and oddjobd service is enabled
- systemctl enable oddjobd.service
- systemctl start oddjobd.service
Ensure that /etc/nsswitch.conf has the following passwd and group
entries. In this file, you have to tell Linux that it should use Winbind
before trying to authenticate locally on Linux.
passwd: files winbind
group: files winbind
Enable and start/restart oddjobd service:
[root@centos8 ~]# systemctl enable oddjobd --now
Test resolving AD users and groups and authentication of users.
[root@centos8 ~]# getent passwd GOLINUXCLOUD\\administrator
GOLINUXCLOUD\administrator:*:1100500:1100513::/home/GOLINUXCLOUD/administrator:/bin/bash
[root@centos8 ~]# id GOLINUXCLOUD\\administrator
uid=1100500(GOLINUXCLOUD\administrator) gid=1100513(GOLINUXCLOUD\domain users) groups=1100513(GOLINUXCLOUD\domain users),1100500(GOLINUXCLOUD\administrator),1100572(GOLINUXCLOUD\denied rodc password replication group),1100518(GOLINUXCLOUD\schema admins),1100519(GOLINUXCLOUD\enterprise admins),1100520(GOLINUXCLOUD\group policy creator owners),1100512(GOLINUXCLOUD\domain admins),100001(BUILTIN\users),100000(BUILTIN\administrators)
9. Login as Active Directory User on Linux Client
Now you can try to login as any of the Active Directory user on this
CentOS 8 client. You don't need to manually create home directory for
the domain users as that would be handled by
/usr/lib64/security/pam_oddjob_mkhomedir.so module provided by
oddjob-mkhomedir rpm.
[root@centos8 ~]# su - GOLINUXCLOUD\\Administrator
Creating home directory for GOLINUXCLOUD\administrator.
Last login: Thu Mar 4 00:46:12 IST 2021 on pts/0
[GOLINUXCLOUD\administrator@centos8 ~]$ pwd
/home/GOLINUXCLOUD/administrator
As you see the the home directory for our Administrator user was automatically created at the first login.
In the next article I will share the steps to Integrate Samba Shares with Active Directory (Linux & Windows)
Summary
Winbind can be used with different idmap backends idmap_tdb,
idmap_ldap, idmap_rid, idmap_sss and idmap_ad. These backends
will help the Red Hat Enterprise Linux system figure out the SID to
uid/gid mappings. If you are using winbind, you will need to choose most
appropriate backend for your environment. i.e. If this is for a single
system, where keeping the uid/gid info the same across multiple systems
is not important. The default tdb backend may be appropriate. If you
need uid/gid info to be consistent across many systems, one of the other
backends will be more appropriate. i.e: autorid or rid.
Lastly I hope the steps from the article to join/add CentOS 8 to Windows Domain Controller on Linux was helpful. So, let me know your suggestions and feedback using the comment section.
Related Searches: join centos 8 to windows domain. rhel 8 active directory authentication. rhel 8 oddjob. centos 8 samba active directory. realm join. join centos to windows domain. how to join domain in redhat linux. centos 8 samba active directory. join centos 8 to windows domain