In this tutorial we will join our Linux client (RHEL/CentOS 7/8) to Windows Domain Active Directory using adcli. The adcli will be using System Security Services Daemon (SSSD) to connect a CentOS/RHEL 7/8 system to Microsoft Active Directory Domain. You basically need two components to connect a RHEL system to Active Directory (AD).
One component, SSSD, interacts with the central identity and authentication source, and the other component, adcli, detects available domains and then you will have to manually configure the underlying RHEL system services, in this case SSSD, to connect to the domain.
Some more articles on similar topic:
- How to join Linux client to Windows AD Domain using realmd with SSSD (CentOS/RHEL 7/8)
- How to join Linux client to Windows AD Domain using adcli with SSSD (CentOS/RHEL 7/8)
- How to join Linux client to Windows AD Domain using winbind (CentOS/RHEL 7/8)
1. Overview on Linux integration with Windows domain using SSSD
The System Security Services Daemon (sssd) provides a set of daemons to manage access to remote directories and authenticate mechanisms, in our case, the Active Directory. The sssd service provides the NSS (Name Service Switch) and PAM (Pluggable Authentication Mechanism) interface for our system and a modular backend system to connect to multiple different account sources and the D-bus interface as well.
Identifying accounts on the remote Active Directory is performed over
LDAP and authentication is done via Kerberos to the AD domain. The LDAP
account search is referenced and calls for the
/usr/lib64/libnss_sss.so.2 NSS module and the /etc/nsswitch.conf
file. Authentication will be referenced using
/lib64/security/pam_nss.so.
We use SSSD to access a user directory for authentication and authorization through a common framework with user caching to permit offline logins. SSSD is the recommended component to connect a RHEL system with one of the following types of identity server:
- Active Directory
- Identity Management (IdM) in RHEL
- Any generic LDAP or Kerberos server
2. Lab Environment
For demonstrations in this article to join Linux to Windows AD Domain on RHEL/CentOS 7/8, we will use two virtual machines running in an Oracle VirtualBox installed on my Linux Server virtualization environment.
I have a Microsoft Server 2012R2 Active Directory Domain Controller with
the IP address 192.168.0.107 and the CentOS 8 client host with the IP
address 192.168.0.117. In this article I will only cover the part to
add Linux to Windows AD Domain on the client side.
So this article to add Linux to Windows AD Domain requires a pre-configured Windows Active Directory.
3. Pre-requisites to add Linux to Windows AD Domain
3.1 Update /etc/resolv.conf
Make sure RHEL/CentOS client machine is able to resolve Active Directory
servers. To do this update your /etc/resolv.conf with the IP address
of your Domain Controller on your RHEL / CentOS 7/8 client host.
[root@adcli-client ~]# cat /etc/resolv.conf
search www.golinuxcloud.com
nameserver 192.168.0.107
3.2 Verify Domain Name Resolution
Verify if the client is able to resolve the domain name:
[root@centos8 ~]# nslookup www.golinuxcloud.com
Server: 192.168.0.107
Address: 192.168.0.107#53
Name: www.golinuxcloud.com
Address: 192.168.0.107
Verify the configuration for name resolution. In particular, verify the DNS SRV records.
~]# host -t SRV _kerberos._udp.golinuxcloud.com.
_kerberos._udp.golinuxcloud.com has SRV record 0 100 88 win-71humtros3m.golinuxcloud.com.
~]# host -t SRV _ldap._tcp.golinuxcloud.com.
_ldap._tcp.golinuxcloud.com has SRV record 0 100 389 win-71humtros3m.golinuxcloud.com.
~]# host -t SRV _ldap._tcp.dc._msdcs.golinuxcloud.com
_ldap._tcp.dc._msdcs.golinuxcloud.com has SRV record 0 100 389 win-71humtros3m.golinuxcloud.com.
3.3 Ensuring support for common encryption types in AD and RHEL
By default, SSSD supports RC4, AES-128, and AES-256 Kerberos encryption types.
RC4 encryption has been deprecated and disabled by default in CentOS/RHEL 8, as it is considered less secure than the newer AES-128 and AES-256 encryption types. You can ignore this step if you are on RHEL/CentOS 7.
You can follow How to fix "KDC has no support for encryption type"? to enable RC4 encryption.
For more information access.redhat.com: Ensuring support for common encryption types in AD and RHEL
3.4 Install packages (RHEL/CentOS 8)
We will need the following packages installed on the CentOS/RHEL 8 client node:
[root@centos8 ~]# dnf -y install adcli sssd oddjob oddjob-mkhomedir samba-common-tools krb5-workstation authselect-compat
3.5 Install packages (RHEL/CentOS 7)
We will need the following packages installed on the CentOS/RHEL 7 client node:
[root@centos7 ~]# yum install adcli sssd authconfig oddjob oddjob-mkhomedir samba-common-tools krb5-workstation
Some brief overview on these individual packages:
- samba-common-tools: This denotes the shared tools for servers and clients
- oddjob: This is a D-bus service that runs the odd jobs for clients
- oddjob-mkhomedir: This is used with the odd job services to create home directories for AD accounts, if needed
- sssd: The System Security Services daemon can be used to divert client authentication as required
- adcli: These are the tools for joining and managing AD domains
- krb5-workstation: provides Kerberos klist command that are useful for verifying Kerberos-related configurations.
4. Using adcli to join Linux to Windows Domain
4.1 Discover the AD domain
You can use adcli info command which displays discovered information
about an Active Directory domain or an Active Directory domain
controller.
[root@centos8 ~]# adcli info www.golinuxcloud.com
[domain]
domain-name = GOLINUXCLOUD.COM
domain-short = GOLINUXCLOUD
domain-forest = GOLINUXCLOUD.COM
domain-controller = WIN-71HUMTROS3M.GOLINUXCLOUD.COM
domain-controller-site = Default-First-Site-Name
domain-controller-flags = pdc gc ldap ds kdc timeserv closest writable good-timeserv full-secret ads-web
domain-controller-usable = yes
domain-controllers = WIN-71HUMTROS3M.GOLINUXCLOUD.COM
[computer]
computer-site = Default-First-Site-Name
4.2 Join RHEL/CentOS 7/8 system to Windows AD domain
adcli join creates a computer account in the domain for the local
machine, and sets up a keytab for the machine. It does not configure an
authentication service (such as sssd).
[root@centos8 ~]# adcli join www.golinuxcloud.com
Password for [email protected]:
adcli: couldn't connect to www.golinuxcloud.com domain: Couldn't authenticate as: [email protected]: KDC has no support for encryption type
Here we are getting "KDC has no support for encryption type" because our Domain Controller is still using RC4 encryption which needs to be enabled on the client as I had informed in the pre-requisite section. This error is to demonstrate the ERROR which you may get if AES encryption is not used on the domain controller.
So, we update the crypto policy on the client and re-atempt the
adcli join command. By default, it prompts for the Administrator
password, but it's possible to specify another user with the -U <USER>
option:
[root@centos8 ~]# adcli join www.golinuxcloud.com
Password for [email protected]:
We can inspect the keytab with klist -kt, which should show several
entries that contain the client's hostname in some form:
[root@centos8 ~]# klist -kte
Keytab name: FILE:/etc/krb5.keytab
KVNO Timestamp Principal
---- ------------------- ------------------------------------------------------
2 03/05/2021 03:38:03 [email protected] (DEPRECATED:arcfour-hmac)
2 03/05/2021 03:38:03 [email protected] (aes128-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 [email protected] (aes256-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 host/[email protected] (DEPRECATED:arcfour-hmac)
2 03/05/2021 03:38:03 host/[email protected] (aes128-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 host/[email protected] (aes256-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 host/[email protected] (DEPRECATED:arcfour-hmac)
2 03/05/2021 03:38:03 host/[email protected] (aes128-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 host/[email protected] (aes256-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (DEPRECATED:arcfour-hmac)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (aes128-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (aes256-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (DEPRECATED:arcfour-hmac)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (aes128-cts-hmac-sha1-96)
2 03/05/2021 03:38:03 RestrictedKrbHost/[email protected] (aes256-cts-hmac-sha1-96)
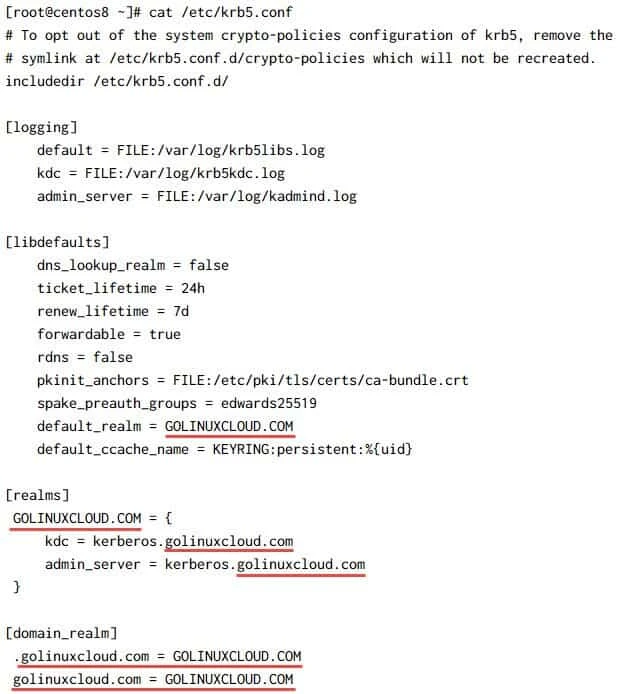
5. Configure Kerberos (/etc/krb5.conf)
Unlike realmd, adcli will not automatically configure SSSD and
Kerberos. So, we must manually configure these services to use with AD
domain. Having tidied the file, after removing comments for our domain,
the file looks similar to the following screenshot:
krb5.conf file, just
update the REALM by replacing EXAMPLE.COM with your DOMAIN.COM
6. Configure NSS and PAM
The Name Service Switch (NSS) configuration file, /etc/nsswitch.conf,
is used by various NSS libraries; one of the NSS libraries is
/usr/lib64/libnss_sss.so.2. The NSS configuration file determines the
sources from which you can obtain the name service information and its
order from a range of categories. Each category of information is
identified by a resource database name; this can be hosts for name
resolution and passwd for a database to locate user accounts.
The services that can use PAM are configured with the associated PAM
modules that they should use within a file in the /etc/pam.d
directory. The can be in individual files, such as /etc/pam.d/login,
or through command files that are referenced by many services (such as
/etc/pam.d/system-auth-ac).
6.1 On RHEL/CentOS 7
Use authconfig to set up the Name Service Switch
(/etc/nsswitch.conf) and PAM stacks(/etc/pam.d/password-auth and
/etc/pam.d/system-auth)
[root@centos7 ~]# authconfig --enablesssd --enablesssdauth --enablelocauthorize --enablemkhomedir --update
The above command will modify and add necessary entries in
/etc/nsswitch.conf, /etc/pam.d/password-auth and
/etc/pam.d/system-auth files. Next enable and start/restart
oddjobd.service
~]# systemctl enable --now oddjobd.service
6.2 On RHEL/CentOS 8
authconfig is replaced by authselect in RHEL/CentOS 8. So we will
use authselect to configure the respective PAM and NSS files which we
discussed in the previous section.
[root@centos8 ~]# authselect select sssd with-mkhomedir --force
Backup stored at /var/lib/authselect/backups/2021-03-02-12-08-32.O2GvBy
Profile "sssd" was selected.
The following nsswitch maps are overwritten by the profile:
- passwd
- group
- netgroup
- automount
- services
Make sure that SSSD service is configured and enabled. See SSSD documentation for more information.
- with-mkhomedir is selected, make sure pam_oddjob_mkhomedir module
is present and oddjobd service is enabled
- systemctl enable oddjobd.service
- systemctl start oddjobd.service
Next enable and start/restart oddjobd.service
~]# systemctl enable --now oddjobd.service
If we check for sss within /etc/nsswitch.conf, we can see all the
databases that rely on a particular library. The
grep command
can be used to isolate these entries, as shown in the following command:
# grep sss /etc/nsswitch.conf
passwd: sss files systemd
group: sss files systemd
netgroup: sss files
automount: sss files
services: sss files
The database names are explained here:
- passwd: This specifies the user accounts
- shadow: This denotes the password information
- group: This specifies the group accounts
- services: This denotes the service name resolution
- netgroup: This specifies the groups of hosts that can be used in access control rules
- automount: This denotes the directories to be auto-mounted by autofs
We can display the configuration that sssd uses with PAM using grep
again to filter sss from the /etc/pam.d/password-auth and
/etc/pam.d/system-auth file:
~]# grep sss /etc/pam.d/*
/etc/pam.d/password-auth:auth sufficient pam_sss.so forward_pass
/etc/pam.d/password-auth:account [default=bad success=ok user_unknown=ignore] pam_sss.so
/etc/pam.d/password-auth:password sufficient pam_sss.so use_authtok
/etc/pam.d/password-auth:session optional pam_sss.so
/etc/pam.d/system-auth:auth sufficient pam_sss.so forward_pass
/etc/pam.d/system-auth:account [default=bad success=ok user_unknown=ignore] pam_sss.so
/etc/pam.d/system-auth:password sufficient pam_sss.so use_authtok
/etc/pam.d/system-auth:session optional pam_sss.so
We can see that the authentication module is used for all possible triggers:
- auth: This is used during authentication
- account: This is used for account restrictions
- password: This is used for password change events
- session: This is used during a logged in session
7. Configure SSSD
With realmd again the SSSD configuration file i.e. /etc/sssd/sssd.conf
is automatically created and populated but with adcli we must manually
create and update this file. Edit /etc/sssd/sssd.conf and define a
single domain (you may have to create the file manually if the file does
not exist):
~]# cat /etc/sssd/sssd.conf
[sssd]
services = nss, pam
config_file_version = 2
domains = GOLINUXCLOUD.COM
[domain/GOLINUXCLOUD.COM]
id_provider = ad
override_homedir = /home/%d/%u
debug_level = 0
ldap_sasl_authid = SHORT_HOSTNAME$
[nss]
override_shell=/bin/bash
[pam]
Make sure /etc/sssd/sssd.conf is owned by root:root and permissions
are 600:
~]# chown root:root /etc/sssd/sssd.conf
# chmod 600 /etc/sssd/sssd.conf
~]# ls -l /etc/sssd/sssd.conf
-rw-------. 1 root root 208 Mar 2 17:39 /etc/sssd/sssd.conf
Enable and start/restart the SSSD service
~]# systemctl enable sssd
~]# systemctl restart sssd
Check the status of sssd.service:

8. Login as Active Directory User on Linux Client
Let us try to login to our Linux client using Windows AD user and verify if the home directory is automatically created. But first we need to check if our Linux client is able to get the user details of AD users:
~]# id GOLINUXCLOUD\\Administrator
uid=111800500(administrator) gid=111800513(domain users) groups=111800513(domain users),111800520(group policy creator owners),111800512(domain admins),111800572(denied rodc password replication group),111800518(schema admins),111800519(enterprise admins)
So our Administrator user from the AD is detected by the Linux client, so let' try to switch user to Administrator:
~]# su - GOLINUXCLOUD\\Administrator
Creating home directory for administrator.
Last login: Tue Mar 2 17:41:26 IST 2021 on pts/0
[administrator@centos8 ~]$ exit
logout
[root@centos8 ~]#
9. Create/Delete Active Directory users
This command is probably not one of the most useful tools given that
we can create the user, but can't enable the account or set the password
for the new user. In this way, the command is less useful than some of
the other tools with adcli.
Here we are creating an AD user "Amit Kumar" with username as amit:
~]# adcli create-user amit --domain=GOLINUXCLOUD.COM --display-name="Amit Kumar"
Password for [email protected]:
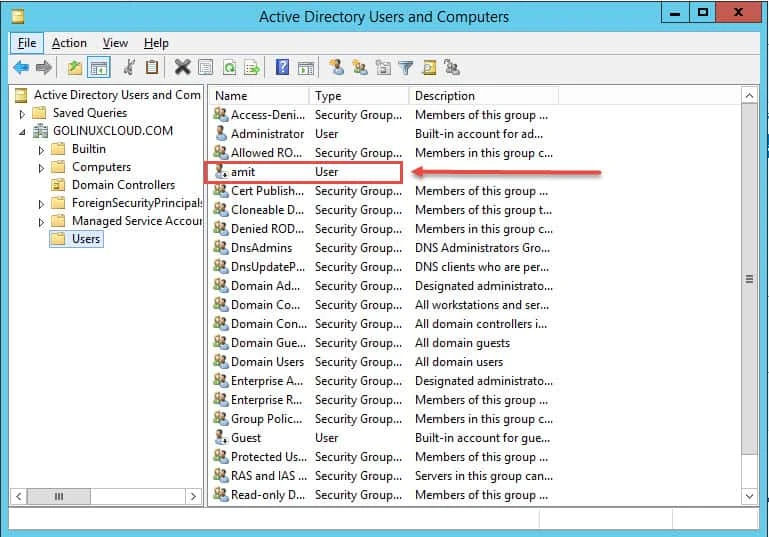
Now if we verify on Microsoft AD, this user is in disabled state:
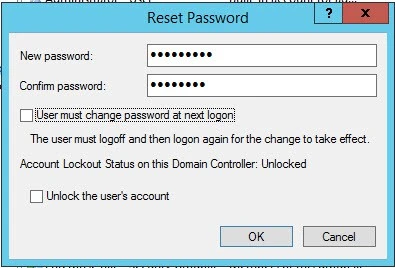
So we must first assign a password to this user. Right click the user and click on Reset Password. provide the password and click on OK
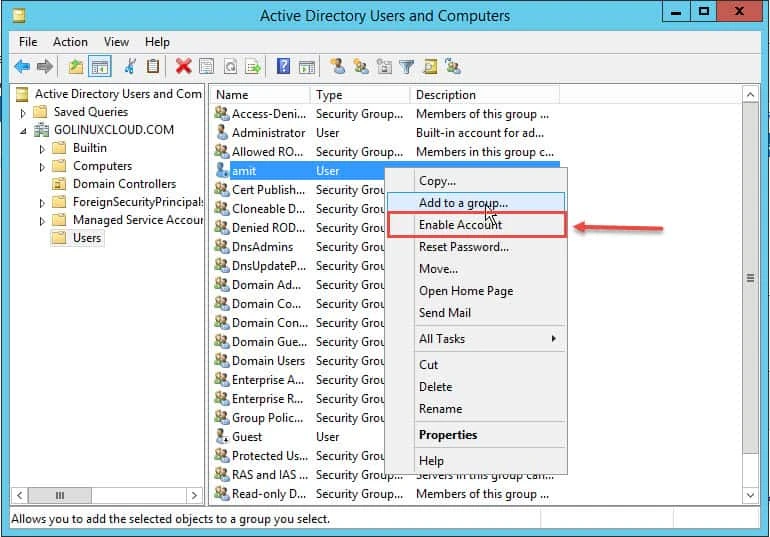
Now to enable the account you can right click on the user and select Enable Account
Now you can try to login using this new user on the Linux client:
~]# id GOLINUXCLOUD\\amit
uid=111801121(amit) gid=111800513(domain users) groups=111800513(domain users)
~]# su - GOLINUXCLOUD\\amit
Creating home directory for amit.
~]$ logout
To delete the account we just created, we will use the following command:
~]# adcli delete-user --domain=www.golinuxcloud.com amit
There are a whole bunch of commands which you can use with adcli, for more information you can check man page of adcli command
Summary
In this article, we looked at how to use the Active Directory as an identity store, utilizing users and groups on Linux. The ease of setting this up makes this a very usable and much-needed solution within corporations throughout the world.
There is a little bit of ground work required before setting up the time and DNS. Once this is set, then you can configure sssd to use Active Directory as an identity source with the command adcli.
With the RHEL system in the AD domain, we can manage this domain to a degree with adcli and give users' access to the Linux command line through a console or via SSH.
Related Searches: linux login with active directory, join linux server to active directory, add linux server to windows domain, linux active directory authentication, how to add a linux system to a windows domain, linux windows domain authentication, linux ad integration



![Samba Active Directory Setup [Step-by-Step]](/setup-samba-active-directory/samba_dc_hu_441d5c3dab5ff3e7.webp)