In this tutorial I will share step by step instructions to install and configure Samba as Active Directory Domain Controller (AD DC) using CentOS 8 Linux server. You may also want to look at FreeIPA which may not be a complete alternative to Windows AD but is an integrated Identity and Authentication solution for Linux/UNIX networked environments. You get a GUI access to manage and control all the user authentications and servers in your organization.
Creating an Active Directory DC implies that we need to have many different services (DNS, Kerberos, LDAP, etc.) working in perfect coordination. Luckily the Samba team has done a great job in easing this process, but it is not simple yet.
Samba as an AD DC only supports:
- Integrated LDAP server as AD back end.
- Heimdal Kerberos Key Distribution Center (KDC).
Lab Environment
I have brought up a CentOS 8 Virtual Machine using Oracle VirtualBox to setup my Samba Domain Controller. Below are the VM specs
| Component | Value |
|---|---|
| FQDN | samba-ad.example.com |
| IP Address | 192.168.43.154 |
| OS | CentOS 8 |
| RAM | 6 GB |
| Storage | 30GB |
| vCPU | 4 |
1. Pre-requisites
According to the officialSambadocumentation, there are a few steps we must complete before installing an Active Directory domain controller in Samba.
1.1 Check FileSystem Support
To set up shares with extended access control list (ACL) support, the
file system hosting the share must have the user and system xattr name
space enabled. On a Samba Active Directory (AD) domain controller (DC),
samba-tool verifies this setting automatically for the file system the
Sysvol share is created on.
Ensure that your kernel has the following options enabled:
CONFIG_EXT4_FS_POSIX_ACL=y
CONFIG_EXT4_FS_SECURITY=y
To check this, first check the kernel version which is loaded on your server
[root@samba-ad ~]# uname -r
4.18.0-147.5.1.el8_1.x86_64
Next check the boot configuration file of this kernel version
[root@samba-ad ~]# grep -E "CONFIG_EXT4_FS_SECURITY|CONFIG_EXT4_FS_POSIX_ACL" /boot/config-4.18.0-147.5.1.el8_1.x86_64
CONFIG_EXT4_FS_POSIX_ACL=y
CONFIG_EXT4_FS_SECURITY=y
1.2 Configure hosts file
Verify that the /etc/hosts file on the DC correctly resolves the fully-qualified domain name (FQDN) and short host name to the LAN IP address of the DC. For example:
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
192.168.43.154 samba-ad samba-ad.example.com
1.3 Perform Cleanup
If you previously ran a Samba installation on this host or else you can skip this section:
Verify that no Samba processes are running:
# ps ax | egrep "samba|smbd|nmbd|winbindd
If the output lists any samba, smbd, nmbd, or winbindd
processes, shut down the processes.
Remove the existing smb.conf file. To list the path to the file:
# smbd -b | grep "CONFIGFILE"
CONFIGFILE: /usr/local/samba/etc/samba/smb.conf
Remove all Samba database files, such as *.tdb and *.ldb files. To
list the folders containing Samba databases:
# smbd -b | egrep "LOCKDIR|STATEDIR|CACHEDIR|PRIVATE_DIR"
LOCKDIR: /usr/local/samba/var/lock/
STATEDIR: /usr/local/samba/var/locks/
CACHEDIR: /usr/local/samba/var/cache/
PRIVATE_DIR: /usr/local/samba/private/
Remove an existing /etc/krb5.conf file:
[root@samba-ad ~]# rm /etc/krb5.conf
rm: remove regular file '/etc/krb5.conf'? y
1.4 Enable Required Repositories
For CentOS 8 we would need following additional repositories apart from the ones which are enabled by default with CentOS 8.
EPEL repo is not
part of the default CentOS installation but we can install
epel-release rpm to install this repo
[root@samba-ad ~]# yum -y install epel-release
Next install dnf-plugins-core to be able to enable repo using
yum config-manager and later enable PowerTools repo from CentOS
[root@samba-ad ~]# yum -y install dnf-plugins-core
[root@samba-ad ~]# yum config-manager --set-enabled PowerTools
The list of enabled repos on my server.
[root@samba-ad ~]# yum repolist
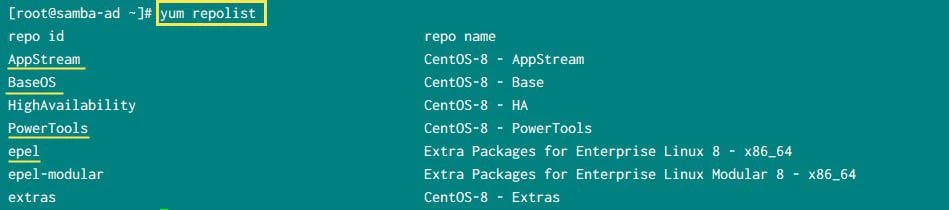
CentOS 8 repositories for Samba AD
2. Install Dependency Packages
Install the following packages to build Samba as an Active Directory (AD) domain controller (DC) on a minimal Red Hat Enterprise Linux (RHEL) 8 or CentOS 8 installation:
[root@samba-ad ~]# yum -y install docbook-style-xsl gcc gdb gnutls-devel gpgme-devel jansson-devel \
keyutils-libs-devel krb5-workstation libacl-devel libaio-devel \
libarchive-devel libattr-devel libblkid-devel libtasn1 libtasn1-tools \
libxml2-devel libxslt lmdb-devel openldap-devel pam-devel perl \
perl-ExtUtils-MakeMaker perl-Parse-Yapp popt-devel python3-cryptography \
python3-dns python3-gpg python36-devel readline-devel rpcgen systemd-devel \
tar zlib-devel
3. Download latest stable samba build
At the time of writing this tutorial, 4.12.5 was the latest available stable samba build. You can manually navigate to https://download.samba.org/pub/samba/stable and download the latest stable build.
[root@samba-ad ~]# wget https://download.samba.org/pub/samba/stable/samba-4.12.5.tar.gz
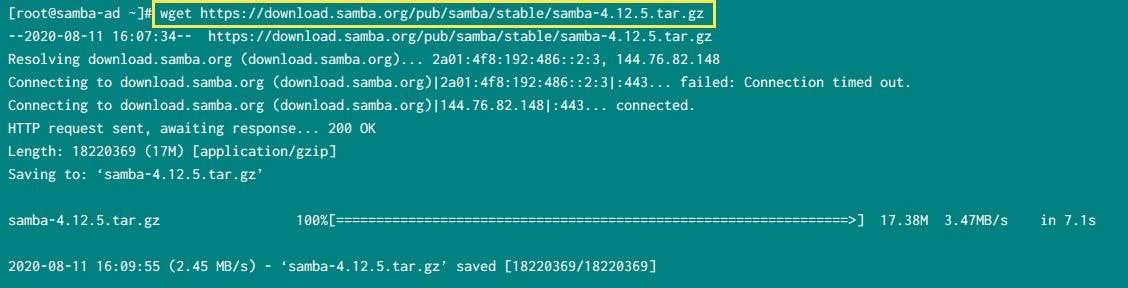
Download Samba4
Once downloaded, extract the content of this archive
[root@samba-ad ~]# tar -xzvf samba-4.12.5.tar.gz
Change into the directory with the extracted sources:
[root@samba-ad ~]# cd samba-4.12.5
The configure script is located in the root of the sources directory.
The main purpose of the script is to create a Makefile which is used
by the command make. The configure script enables you to set various
options, like installation paths. We will execute it without any
additional options.
[root@samba-ad ~]# ./configure
<Output trimmed>
If the configure script exits without an error, you see the following output:
'configure' finished successfully (2m32.681s)
If you observe any errors, check the official documentation for more help
To start the compilation, run make as shown below. This may take some time to complete so you can go and have some coffee in the mean time.
The make command is able to run multiple jobs in parallel. For
example, to run 2 make sub-tasks at the same time to decrease the
execution time, run:
# make -j 2
[root@samba-ad ~]# make
<Output trimmed>
If the installation exits without an error, you see the following output:
Waf: Leaving directory `/root/samba-4.12.5/bin/default'
Build commands will be stored in bin/default/compile_commands.json
'build' finished successfully (32m20.012s)
To install the compiled software, you require root permissions to write to the destination directories and set the correct permissions.
[root@samba-ad ~]# make install
<Output trimmed>
If the installation exits without an error, you see the following output:
Waf: Leaving directory `/root/samba-4.12.5/bin/default'
Build commands will be stored in bin/default/compile_commands.json
'install' finished successfully (8m56.726s)
4. Set environment variable
If you have defined a custom PATH for your samba binaries with configure
then you can modify the PATH accordingly. Since I have configure samba
Active Directory with default values, I will execute the below command
to add the samba binary paths into the PATH variable to avoid writing
the full path of the samba commands
export PATH=/usr/local/samba/bin/:/usr/local/samba/sbin/:$PATH
Executing this will update PATH variable only for current session, to
make this permanent for root user, add this into the user root's
.bash_profile or if you want normal users also to be able to access
samba commands then you can just add this in /etc/profile

update environment variable
5. Provisioning Samba Active Directory
Provisioning consists of setting up all the infrastructure needed for a Samba Active Directory domain to run such as LDAP, Kerberos, and DNS servers. The Samba AD provisioning process creates the AD databases and adds initial records, such as the domain administrator account and required DNS entries.
--use-rfc2307parameter to thesamba-tool
domain provisioncommand. This enables you to store Unix attributes in
AD, such as user IDs (UID), home directories paths, group IDs (GID).
Enabling the NIS extensions has no disadvantages. However, enabling them
in an existing domain requires manually extending the AD schema.
[root@samba-ad samba-4.12.5]# samba-tool domain provision --use-rfc2307 --interactive --option="interfaces= lo eth1" --option="bind interfaces only=yes"
Realm [EXAMPLE.COM]: EXAMPLE.COM <-- provide the realm name
Domain [EXAMPLE]: EXAMPLE <-- provide the domain name
Server Role (dc, member, standalone) [dc]: dc <-- Since we are configuring samba active directory, we use dc
DNS backend (SAMBA_INTERNAL, BIND9_FLATFILE, BIND9_DLZ, NONE) [SAMBA_INTERNAL]: SAMBA_INTERNAL <-- We will let samba configure it's own DNS and zone files
DNS forwarder IP address (write 'none' to disable forwarding) [192.168.43.154]: 8.8.8.8 <-- We will use google's dns
Administrator password: <-- Provide the Administrator user's password
Retype password:
INFO 2020-08-11 15:40:59,849 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2133: Looking up IPv4 addresses
INFO 2020-08-11 15:40:59,849 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2150: Looking up IPv6 addresses
INFO 2020-08-11 15:41:01,763 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2305: Setting up secrets.ldb
INFO 2020-08-11 15:41:01,798 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2311: Setting up the registry
INFO 2020-08-11 15:41:01,839 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2314: Setting up the privileges database
INFO 2020-08-11 15:41:01,925 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2317: Setting up idmap db
INFO 2020-08-11 15:41:01,984 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2324: Setting up SAM db
INFO 2020-08-11 15:41:01,998 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #897: Setting up sam.ldb partitions and settings
INFO 2020-08-11 15:41:01,999 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #909: Setting up sam.ldb rootDSE
INFO 2020-08-11 15:41:02,011 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1338: Pre-loading the Samba 4 and AD schema
Unable to determine the DomainSID, can not enforce uniqueness constraint on local domainSIDs
INFO 2020-08-11 15:41:02,075 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1416: Adding DomainDN: DC=example,DC=com
INFO 2020-08-11 15:41:02,102 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1448: Adding configuration container
INFO 2020-08-11 15:41:02,129 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1463: Setting up sam.ldb schema
INFO 2020-08-11 15:41:12,465 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1481: Setting up sam.ldb configuration data
INFO 2020-08-11 15:41:13,108 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1522: Setting up display specifiers
INFO 2020-08-11 15:41:20,575 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1530: Modifying display specifiers and extended rights
INFO 2020-08-11 15:41:20,714 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1537: Adding users container
INFO 2020-08-11 15:41:20,719 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1543: Modifying users container
INFO 2020-08-11 15:41:20,722 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1546: Adding computers container
INFO 2020-08-11 15:41:20,727 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1552: Modifying computers container
INFO 2020-08-11 15:41:20,730 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1556: Setting up sam.ldb data
INFO 2020-08-11 15:41:21,320 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1586: Setting up well known security principals
INFO 2020-08-11 15:41:21,476 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1600: Setting up sam.ldb users and groups
INFO 2020-08-11 15:41:22,590 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #1608: Setting up self join
Repacking database from v1 to v2 format (first record CN=ms-net-ieee-80211-GP-PolicyGUID,CN=Schema,CN=Configuration,DC=example,DC=com)
Repack: re-packed 10000 records so far
Repacking database from v1 to v2 format (first record CN=IntellimirrorSCP-Display,CN=816,CN=DisplaySpecifiers,CN=Configuration,DC=example,DC=com)
Repacking database from v1 to v2 format (first record CN=Group Policy Creator Owners,CN=Users,DC=example,DC=com)
INFO 2020-08-11 15:41:27,599 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/sambadns.py #1130: Adding DNS accounts
INFO 2020-08-11 15:41:27,649 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/sambadns.py #1164: Creating CN=MicrosoftDNS,CN=System,DC=example,DC=com
INFO 2020-08-11 15:41:27,740 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/sambadns.py #1177: Creating DomainDnsZones and ForestDnsZones partitions
INFO 2020-08-11 15:41:27,885 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/sambadns.py #1182: Populating DomainDnsZones and ForestDnsZones partitions
Repacking database from v1 to v2 format (first record DC=_msdcs,DC=example.com,CN=MicrosoftDNS,DC=DomainDnsZones,DC=example,DC=com)
Repacking database from v1 to v2 format (first record DC=@,DC=_msdcs.example.com,CN=MicrosoftDNS,DC=ForestDnsZones,DC=example,DC=com)
INFO 2020-08-11 15:41:28,439 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2037: Setting up sam.ldb rootDSE marking as synchronized
INFO 2020-08-11 15:41:28,449 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2042: Fixing provision GUIDs
INFO 2020-08-11 15:41:32,080 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2377: A Kerberos configuration suitable for Samba AD has been generated at /usr/local/samba/private/krb5.conf
INFO 2020-08-11 15:41:32,080 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2378: Merge the contents of this file with your system krb5.conf or replace it with this one. Do not create a symlink!
INFO 2020-08-11 15:41:32,531 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #2107: Setting up fake yp server settings
INFO 2020-08-11 15:41:32,795 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #490: Once the above files are installed, your Samba AD server will be ready to use
INFO 2020-08-11 15:41:32,796 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #494: Server Role: active directory domain controller
INFO 2020-08-11 15:41:32,796 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #495: Hostname: samba-ad
INFO 2020-08-11 15:41:32,796 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #496: NetBIOS Domain: EXAMPLE
INFO 2020-08-11 15:41:32,797 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #497: DNS Domain: example.com
INFO 2020-08-11 15:41:32,797 pid:53118 /usr/local/samba/lib64/python3.6/site-packages/samba/provision/__init__.py #498: DOMAIN SID: S-1-5-21-2126248986-2501897089-2532841763
6. Configure the DNS Resolver
Domain members in an AD use DNS to locate services, such as LDAP and Kerberos. For that, they need to use a DNS server that is able to resolve the AD DNS zone.
On your DC, set the AD DNS domain in the search and the IP of your DC in
the nameserver parameter of the /etc/resolv.conf file. For example:
[root@samba-ad samba-4.12.5]# cat /etc/resolv.conf
# Generated by NetworkManager
search example.com
nameserver 192.168.43.154
7. Start Samba Service
Execute from the terminal as root user
# samba
We don't have any systemd service to manage samba service, although you
can
create a systemd unit file. Once you execute the above command, it will start the
samba service
[root@samba-ad ~]# ps -ef | grep samba
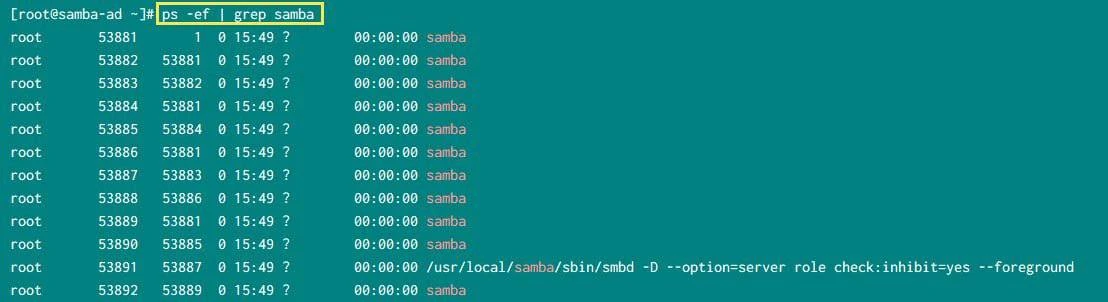
Start Samba Active Directory service
8. Verify Samba Service
After launching the Samba service we can check that everything is
working as expected. If we executetestparmwe’ll see that our server
is recognized as an Active Directory DC.
[root@samba-ad ~]# testparm
Load smb config files from /usr/local/samba/etc/smb.conf
Loaded services file OK.
Server role: ROLE_ACTIVE_DIRECTORY_DC
Press enter to see a dump of your service definitions
# Global parameters
[global]
dns forwarder = 8.8.8.8
passdb backend = samba_dsdb
realm = EXAMPLE.COM
server role = active directory domain controller
workgroup = EXAMPLE
rpc_server:tcpip = no
rpc_daemon:spoolssd = embedded
rpc_server:spoolss = embedded
rpc_server:winreg = embedded
rpc_server:ntsvcs = embedded
rpc_server:eventlog = embedded
rpc_server:srvsvc = embedded
rpc_server:svcctl = embedded
rpc_server:default = external
winbindd:use external pipes = true
idmap_ldb:use rfc2307 = yes
idmap config * : backend = tdb
map archive = No
vfs objects = dfs_samba4 acl_xattr
[sysvol]
path = /usr/local/samba/var/locks/sysvol
read only = No
[netlogon]
path = /usr/local/samba/var/locks/sysvol/example.com/scripts
read only = No
Testing samba4
# smbclient --version
Version 4.12.5
This should show you a version starting with "Version 4.0.XXXXX"
Now try this command:
# smbclient -L localhost -U%
and check if you get a proper reply with all the shared directories
including sysvol and netlogon. The 'netlogon' and 'sysvol'
shares are basic shares needed for Active Directory server operation.
To test that authentication is working, you should try to connect to the
netlogon share using the administrator password you set earlier.
[root@samba-ad samba-4.12.5]# smbclient //localhost/netlogon -Uadministrator%Abhideep@12 -c 'ls'
. D 0 Tue Aug 11 15:32:02 2020
.. D 0 Tue Aug 11 15:32:23 2020
22185808 blocks of size 1024. 4609788 blocks available
9. Create Reverse Zone
You can optionally add a reverse lookup zone.
[root@samba-ad samba-4.12.5]# samba-tool dns zonecreate 192.168.43.154 43.168.192.in-addr.arpa -U administrator
Password for [EXAMPLE\administrator]:
Zone 43.168.192.in-addr.arpa created successfully
If you need more than one reverse zone (multiple subnets), just run the above command again but with the data for the other subnet.
The reverse zone is directly live without restarting Samba or BIND.
10. Configure Network Time Synchronization
If we want our Active Directory to work properly, synchronizing the time
is mandatory. We will use chronyd for time synchronization
Steps to configure Chrony as NTP Server & Client (CentOS/RHEL 8)
11. Configuring Kerberos
In an AD, Kerberos is used to authenticate users, machines, and services. During the provisioning, Samba created a Kerberos configuration file for your DC. Copy this file to your operating system's Kerberos configuration. For example:
[root@samba-ad samba-4.12.5]# cp /usr/local/samba/private/krb5.conf /etc/krb5.conf
The pre-created Kerberos configuration uses DNS service (SRV) resource records to locate the KDC.
12. Verifying DNS
The tcp-based _ldap SRV record in the domain:
[root@samba-ad samba-4.12.5]# host -t SRV _ldap._tcp.example.com.
_ldap._tcp.example.com has SRV record 0 100 389 samba-ad.example.com.
The udp-based _kerberos SRV resource record in the domain:
[root@samba-ad samba-4.12.5]# host -t SRV _kerberos._udp.example.com.
_kerberos._udp.example.com has SRV record 0 100 88 samba-ad.example.com.
The A record of the domain controller:
[root@samba-ad samba-4.12.5]# host -t A samba-ad.example.com.
samba-ad.example.com has address 192.168.43.154
13. Verifying Kerberos
Request a Kerberos ticket for the domain administrator account:
[root@samba-ad samba-4.12.5]# kinit Administrator
Password for [email protected]:
Warning: Your password will expire in 41 days on Tue 22 Sep 2020 03:41:22 PM IST
List the cached Kerberos tickets:
[root@samba-ad samba-4.12.5]# klist
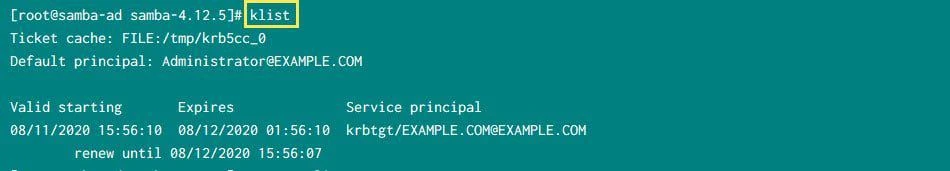
List Kerberos Tickets
14. Configure Firewall
We are using firewalld in our CentOS 8 environment so we will use
firewalld to enable ports and services part of Samba Active Directory
[root@samba-ad ~]# firewall-cmd --add-service={dns,ldap,ldaps,kerberos}
success
[root@samba-ad ~]# firewall-cmd --add-port={389/udp,135/tcp,135/udp,138/udp,138/tcp,137/tcp,137/udp,139/udp,139/tcp,445/tcp,445/udp,3268/udp,3268/tcp,3269/tcp,3269/udp,49152/tcp}
success
15. Managing Samba AD Domain Controller
We have already provisioned the new Samba Active Directory domain with samba-tool . In addition, though, there are many more things that we can do with this versatile tool. For instance, we can list the current users.
[root@samba-ad ~]# samba-tool user list
krbtgt
Administrator
Guest
We can also create an additional user
[root@samba-ad ~]# samba-tool user create deepak
New Password:
Retype Password:
User 'deepak' created successfully
Now verify the list of users
[root@samba-ad ~]# samba-tool user list
deepak
krbtgt
Administrator
Guest
To list the available groups
[root@samba-ad ~]# samba-tool user list
We can also add the user we just created to the Domain Admins group
[root@samba-ad ~]# samba-tool group addmembers "Domain Admins" deepak
Added members to group Domain Admins
Verify the list of members from "Domain Admins" group
[root@samba-ad ~]# samba-tool group listmembers "Domain Admins"
deepak
Administrator
Conclusion
In this tutorial we have successfully setup a Samba Active Directory Domain Controller using Samba4 on CentOS 8 Linux server. The provisioning step would be same across all Linux distributions, although the dependency package to be installed will vary based on different Linux distros. We have used an interactive method for provisioning the Samba4 AD but you can also provide all the values as input and perform non-interactive configuration.
Lastly I hope the steps from the article to configure Samba AD DC on CentOS 8Linux was helpful. So, let me know your suggestions and feedback using the comment section.
References
I have used below external references for this tutorial guide
Setting
up Samba as Active Directory as Domain Controller



![Samba Active Directory Setup [Step-by-Step]](/setup-samba-active-directory/samba_dc_hu_441d5c3dab5ff3e7.webp)