How to configure apache http server to transfer files? Steps to configure apache HTTP server over TLS/SSL to transfer files. How to configure Apache server using TLS/SSL to upload and transfer file using curl. How to transfer files over https? How to upload file using curl to an HTTPS server. How to configure HTTP server using LIMIT to allow download and upload of a file or directory using curl in Linux.
Earlier I had written an article with 5 different commands to securely transfer files between multiple hosts. Now you can consider HTTPS also as one of the possible options to securely transfer files (upload and download) between multiple hosts over the network.
In this article I will share the steps to configure an apache HTTP server using TLS/SSL and then transfer file to HTTPS server using curl (uploading a file). I am using CentOS 7.4 to demonstrate the steps from this article. I will configure a very basic HTTP server with not much customization as Apache can be very complex if we enter into using all the features. But since we are concentrating on configuring an HTTPS server to upload and download a file (transfer a file), we will configure a basic HTTPS server.
Install Apache
The very first thing we have to do is install the apache rpm before we start configuring our web server.
[root@node2 ~]# yum -y install httpd
Next we will create some dummy file and directory and publish it on our webserver.
[root@node2 ~]# cd /var/www/html/
[root@node2 html]# mkdir secret
[root@node2 html]# chmod 777 secret
I am creating an alias /web which will redirect to
/var/www/html/secret. Also we have defined directive. The directive
limits the scope of the enclosed directives by URL. It is similar to the
directive, and starts a subsection which is terminated with a directive.
sections are processed in the order they appear in the configuration
file, after the sections and .htaccess files are read, and after the
sections.
The purpose of the directive is to restrict the effect of the access controls to the nominated HTTP methods. For all other methods, the access restrictions that are enclosed in the bracket will have no effect.
[root@node2 ~]# vim /etc/httpd/conf/httpd.conf
Alias /web "/var/www/html/secret"
<Directory "/var/www/html/secret">
Options Indexes MultiViews FollowSymLinks Includes ExecCGI
AllowOverride None
Allow from all
Require all granted
</Directory>
<Location /web>
Dav On
<LimitExcept GET HEAD OPTIONS PUT>
Order Allow,Deny
Allow from all
</LimitExcept>
</Location>
Next restart the httpd services to make the changes affect.
[root@node2 ~]# systemctl restart httpd
Check the service status.
[root@node2 ~]# systemctl status httpd
● httpd.service - The Apache HTTP Server
Loaded: loaded (/usr/lib/systemd/system/httpd.service; enabled; vendor preset: disabled)
Active: active (running) since Sun 2019-04-14 13:52:04 IST; 9min ago
Docs: man:httpd(8)
man:apachectl(8)
Main PID: 3134 (httpd)
Status: "Total requests: 0; Current requests/sec: 0; Current traffic: 0 B/sec"
Tasks: 6
CGroup: /system.slice/httpd.service
├─3134 /usr/sbin/httpd -DFOREGROUND
├─3255 /usr/sbin/httpd -DFOREGROUND
├─3256 /usr/sbin/httpd -DFOREGROUND
├─3257 /usr/sbin/httpd -DFOREGROUND
├─3259 /usr/sbin/httpd -DFOREGROUND
└─3260 /usr/sbin/httpd -DFOREGROUND
Apr 14 13:52:04 node2.example.com systemd[1]: Starting The Apache HTTP Server...
Apr 14 13:52:04 node2.example.com systemd[1]: Started The Apache HTTP Server.
Enable the httpd service to make it reboot persistent.
[root@node2 ~]# systemctl enable httpd
Created symlink from /etc/systemd/system/multi-user.target.wants/httpd.service to /usr/lib/systemd/system/httpd.service.
Create TLS/SSL certificates
We will store all our key and certificates inside
"/etc/pki/tls/certs/"
Let us start by creating 2048 bit SSL key
[root@node2 html]# cd /etc/pki/tls/certs/
[root@node2 certs]# openssl genpkey -algorithm rsa -pkeyopt rsa_keygen_bits:2048 -out node2.example.com.key
........+++
.....................................................+++
Verify the created key "node2.example.com.key"
[root@node2 certs]# ls -ltr
total 16
-rwxr-xr-x. 1 root root 829 Oct 31 04:12 renew-dummy-cert
-rw-r--r--. 1 root root 2516 Oct 31 04:12 Makefile
-rwxr-xr-x. 1 root root 610 Oct 31 04:12 make-dummy-cert
lrwxrwxrwx. 1 root root 55 Feb 17 17:28 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
lrwxrwxrwx. 1 root root 49 Feb 17 17:28 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
-rw-r--r--. 1 root root 1704 Apr 14 11:26 node2.example.com.key
Once the key is generated, next generate a Certificate Request (CSR). You can encrypt the key using a passphrase which will be prompted at the end.
[root@node2 certs]# openssl req -new -key node2.example.com.key -out node2.example.com.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:IN
State or Province Name (full name) []:KARNATAKA
Locality Name (eg, city) [Default City]:BANGALORE
Organization Name (eg, company) [Default Company Ltd]:GoLinuxCloud
Organizational Unit Name (eg, section) []:TEST
Common Name (eg, your name or your server's hostname) []:node2.example.com
Email Address []:[email protected]
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
Verify the CSR file
[root@node2 certs]# ls -ltr
total 20
-rwxr-xr-x. 1 root root 829 Oct 31 04:12 renew-dummy-cert
-rw-r--r--. 1 root root 2516 Oct 31 04:12 Makefile
-rwxr-xr-x. 1 root root 610 Oct 31 04:12 make-dummy-cert
lrwxrwxrwx. 1 root root 55 Feb 17 17:28 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
lrwxrwxrwx. 1 root root 49 Feb 17 17:28 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
-rw-r--r--. 1 root root 1704 Apr 14 11:26 node2.example.com.key
-rw-r--r--. 1 root root 1078 Apr 14 11:28 node2.example.com.csr
Lastly sign the certificate and create a CRT file
[root@node2 certs]# openssl x509 -req -days 365 -signkey node2.example.com.key -in node2.example.com.csr -out node2.exam ple.com.crt
Signature ok
subject=/C=IN/ST=KARNATAKA/L=BANGALORE/O=GoLinuxCloud/OU=TEST/CN=node2.example.com/[email protected]
Getting Private key
Verify the CRT file
[root@node2 certs]# ls -ltr
total 24
-rwxr-xr-x. 1 root root 829 Oct 31 04:12 renew-dummy-cert
-rw-r--r--. 1 root root 2516 Oct 31 04:12 Makefile
-rwxr-xr-x. 1 root root 610 Oct 31 04:12 make-dummy-cert
lrwxrwxrwx. 1 root root 55 Feb 17 17:28 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
lrwxrwxrwx. 1 root root 49 Feb 17 17:28 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
-rw-r--r--. 1 root root 1704 Apr 14 11:26 node2.example.com.key
-rw-r--r--. 1 root root 1078 Apr 14 11:28 node2.example.com.csr
-rw-r--r--. 1 root root 1354 Apr 14 11:29 node2.example.com.crt
So now we have all the keys what we need to configure our apache server with SSL.
Module Management (mod_ssl)
The Apache web server includes many modular features. For example, it’s
not possible to set up SSL-secured websites without the mod_ssl
package, which includes the mod_ssl.so module along with the
ssl.conf configuration file.
A number of other similar systems are organised in modules. Loaded
modules are included in standard Apache configuration files with the
LoadModule directive. A full list of available modules is located in
the /usr/lib64/httpd/modules directory, but available modules aren’t
used unless they’re loaded with the LoadModule directive in
appropriate Apache configuration files within the
/etc/httpd/conf.modules.d directory.
So we will install mod_ssl using 'yum' command
[root@node2 certs]# yum install openssl mod_ssl -y
Configure SSL
Next we will
configure our apache with SSL
keys. Add the below content at the end of
"/etc/httpd/conf.d/ssl.conf" file.
[root@node2 ~]# vim /etc/httpd/conf.d/ssl.conf
<VirtualHost *:443>
DocumentRoot "/var/www/html"
ServerName node2.example.com:443
SSLCertificateFile /etc/pki/tls/certs/node2.example.com.crt
SSLCertificateKeyFile /etc/pki/tls/certs/node2.example.com.key
</VirtualHost>
Restart the httpd service
[root@node2 ~]# systemctl restart httpd
Next verify your web server. Connect to node2.example.com using https.
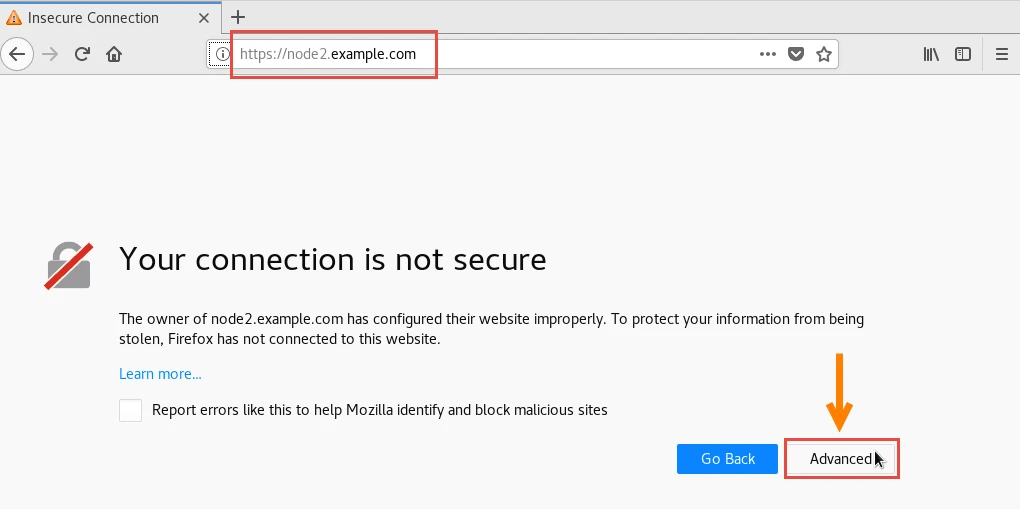
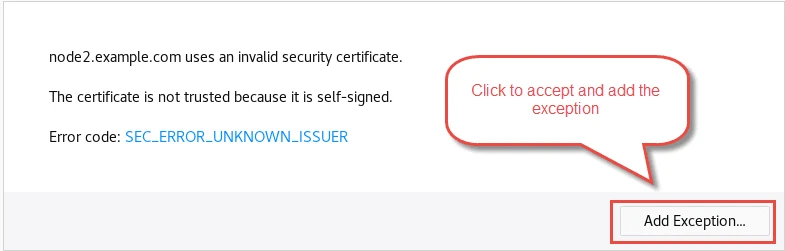
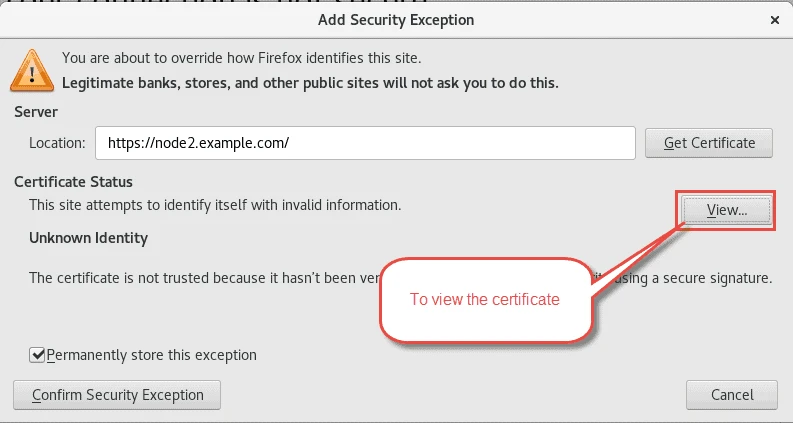
Below is the certificate which we have generated
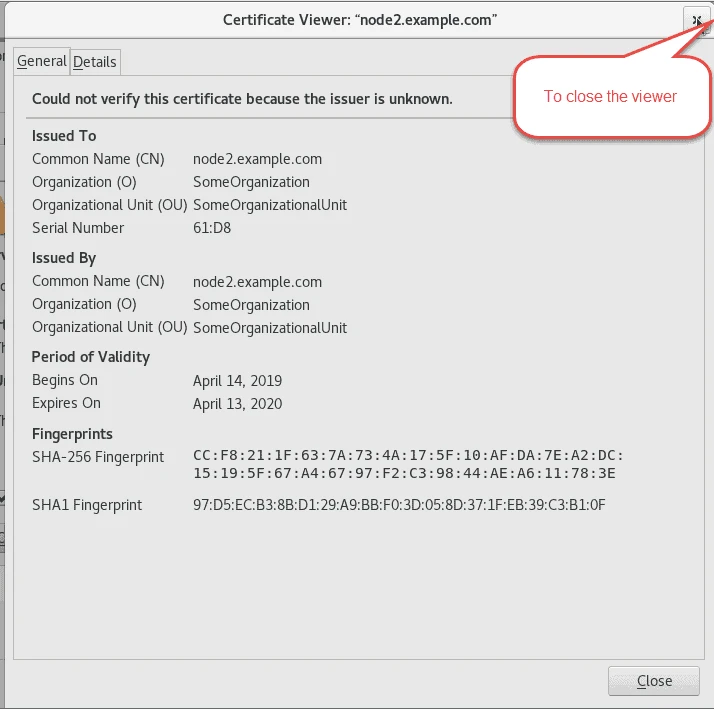
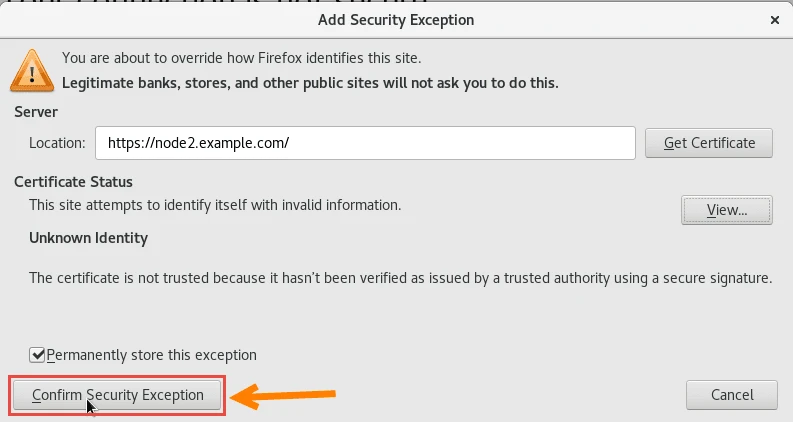
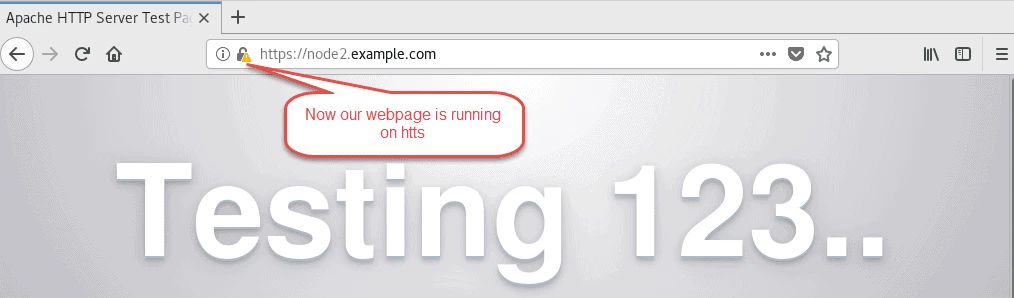
So our apache server is properly configured with SSL.
Disable SELinux
For the sake of this article we have disabled SELinux policy.
Change SELINUX in /etc/selinux/config to Disabled as shown below
SELINUX=disabled
and reboot the node.
Once the node comes up, check the selinux status
[root@node2 ~]# getenforce
Disabled
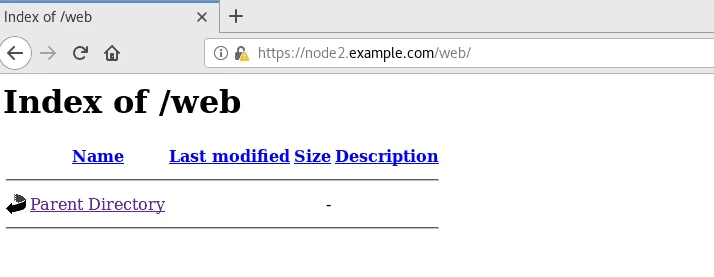
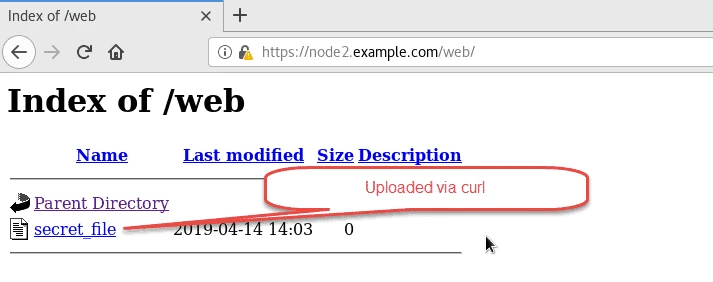
Transfer files using curl on HTTPS
Next we come to the main topic of this article. We will create a dummy
file which we will attempt to upload to our HTTPS server using curl.
[root@node2 ~]# touch /tmp/secret_file
Using the below command we are uploading /tmp/secret_file to the
provided web server location
--insecure argument
here.
[root@node2 ~]# curl --insecure -T /tmp/secret_file https://node2.example.com/web/
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN">
<html><head>
<title>201 Created</title>
</head><body>
<h1>Created</h1>
<p>Resource /web/secret_file has been created.</p>
</body></html>
[root@node2 ~]# ls -l /var/www/html/secret/
total 0
-rw-r--r-- 1 apache apache 0 Apr 14 14:03 secret_file
You can also upload a file using a certain user for enhanced security.
To use a user, your apache must be configured to
allow access for specific user. I have written another article with the steps to authenticate user to
use apache server. Once you have the user in place, try the below
command and replace root:redhat with user:password. Here we are
uploading root_file available under /tmp location to our web server.
[root@node2 ~]# touch /tmp/root_file
[root@node2 ~]# curl --insecure -u root:redhat -T /tmp/root_file https://node2.example.com:443/web/
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN">
<html><head>
<title>201 Created</title>
</head><body>
<h1>Created</h1>
<p>Resource /web/root_file has been created.</p>
</body></html>
[root@node2 ~]# ls -l /var/www/html/secret/
total 0
-rw-r--r-- 1 apache apache 0 Apr 14 14:04 root_file
-rw-r--r-- 1 apache apache 0 Apr 14 14:04 secret_file
Lastly I hope the steps from the article to configure HTTPS server to transfer files on Linux was helpful. So, let me know your suggestions and feedback using the comment section.





![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)