In this guide, we will be learning how the bad actors or attackers use some of the freely available tools on the internet to launch Snapchat phishing attacks. One of the most popular social apps in the world is Snapchat. Millions of people use Snapchat to share photos and videos with friends and total strangers, and the app has become a primary way people share content in the past few years.
Sometimes, people are tricked into sending Snapchat login information like usernames and passwords to strangers on the internet through phishing pages. This can happen when you are visiting a website that looks like the real thing but is actually built to steal your information. This is called a “Snapchat phishing” or “Snapchat fishing” website. And the worst part is that you probably don’t even realize you’ve been tricked until you’ve already sent your credentials.
Pre-requisites
- Have a PC (Any of the common operating systems i.e. Windows or Linux can be used).
- Have a running web server software on the PC
- Have a target device. Any type of device can be used here.
GrayfishFeatures
- Almost, all Templates are under 20KBs which helps in loading webpages fast.
- Images are encoded in base64 to avoid external + internal linking.
- Codes are highly compressed. Extra codes have been removed.
- The login form can't be bypassed until all inputs have been filled by a victim.
- Link with custom preview(image + title + description) when shared on any website.
- Admin login panel has been created for absolute dummies.
Steps for snapchat phishing using Grayfish
In this guide, we will be installing and using Grayfish on Kali Linux.
Step-1: Installing xampp
To run Grayfish for Snapchat phishing, we need to first install a web server software such as the xampp. Installing such software is a straight forward exercise. We just need to navigate to the xampp web server website and download the installer file with respect to the operating system you are running on.
After downloading xampp web server installer package on Linux we will navigate to the downloads directory and run the installing command.
sudo dpkg -i xampp*.run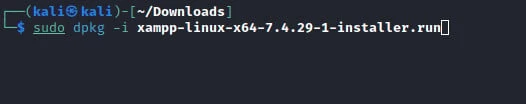
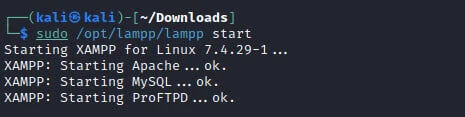
After the installation is complete, we can run the webserver and the required services using the command.
sudo /opt/lampp/lampp start
Step-2: Copy Grayfish files
We have to download grayfish files from its GitHub repository. We
will move grayfish files to the htdocs folder that has been created
after installing xampp. This folder can be found at /opt/lampp/htdocs
on Linux.
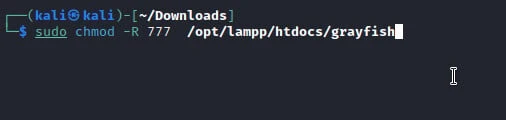
Step-3: Provide required permissions for Grayfish to run
If we try to run grayfish, we may get an error due to a permissions issue, we have to give grayfish the required permissions for it to run from the htdocs folder for Snapchat phishing. To change the permissions we use the command.
sudo chmod -R 777 /opt/lampp/htdocs/grayfish
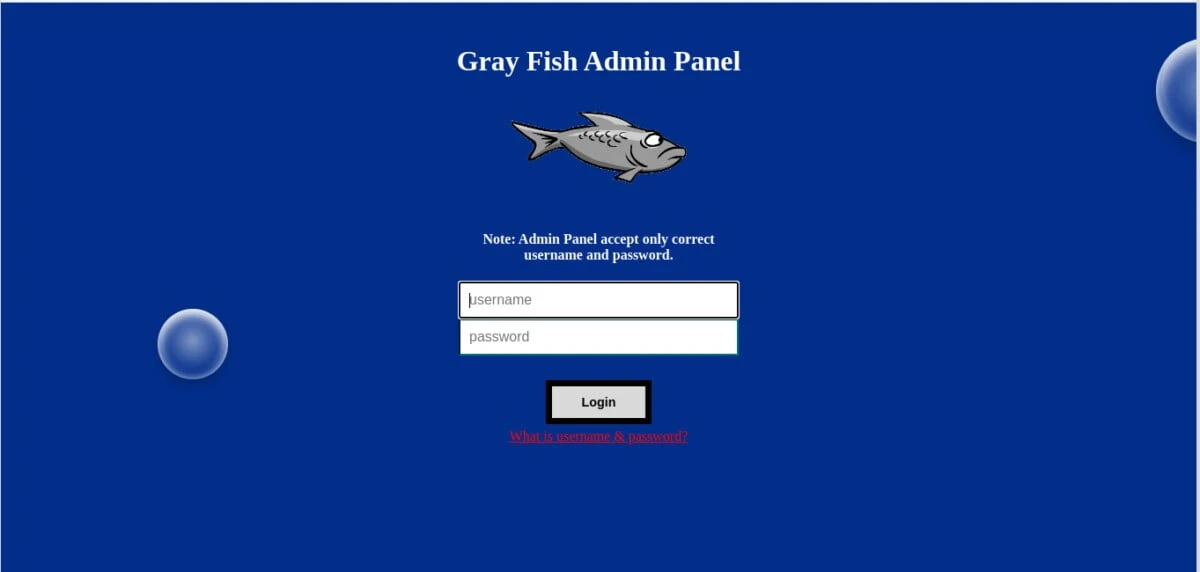
Step-4: Access Grayfish
We can now try to access the grayfish administration page by opening a browser and navigating to localhost/grayfish. If you have done each step shown above correctly, the grayfish login page should appear as shown in the image below. the default admin username is “fish” and the default password is “fish”.
Step-5: Phishing pages
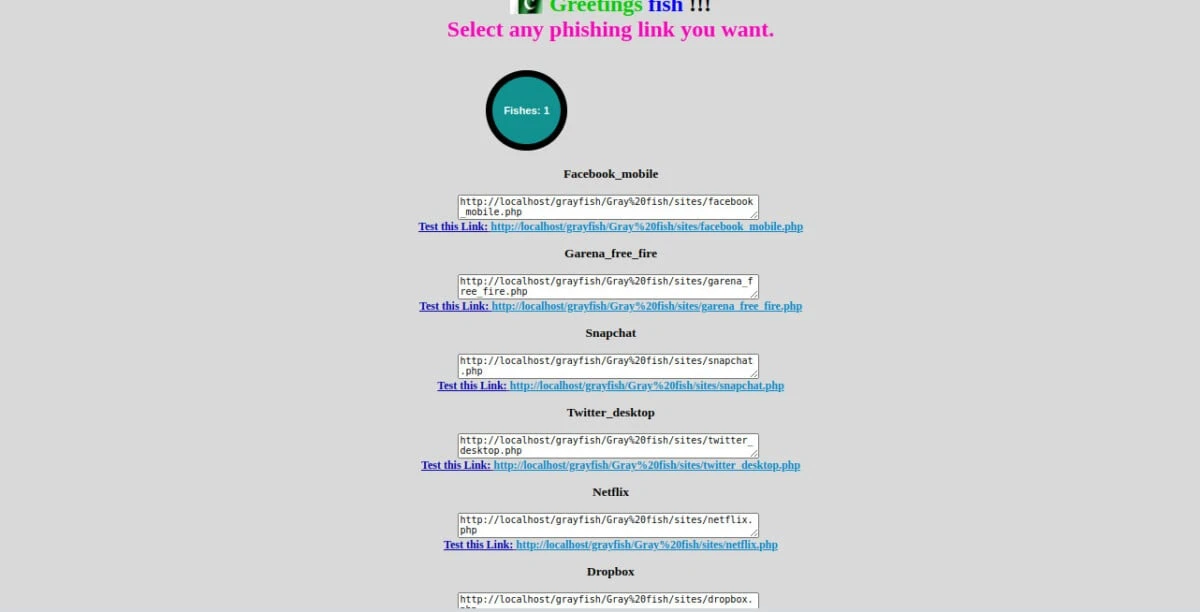
Once logged in we can now launch a Snapchat phishing attack. Grayfish has phishing pages for several popular websites including Google, Microsoft, Instagram, Facebook e.t.c. On the main page, we can now be able to see links to different phishing pages for different popular websites as shown in the image below.
Step-6: Share the Snapchat phishing link
To carry out Snapchat phishing, you can copy and share the Snapchat phishing link with the victim. Once he/she clicks and provides the required information, the information will be logged on grayfish administration page. But that is not yet what we need. As you can see, the attack can only be carried out on targets within our network. If you want to do Snapchat phishing over the internet, we have to use ngrok to ensure our phishing webpage can be accessed over the internet.
./ngrok http 80
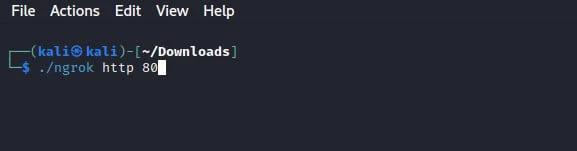
After running the command, we can access the grayfish admin panel using the link we generated on ngrok as shown in the image below.

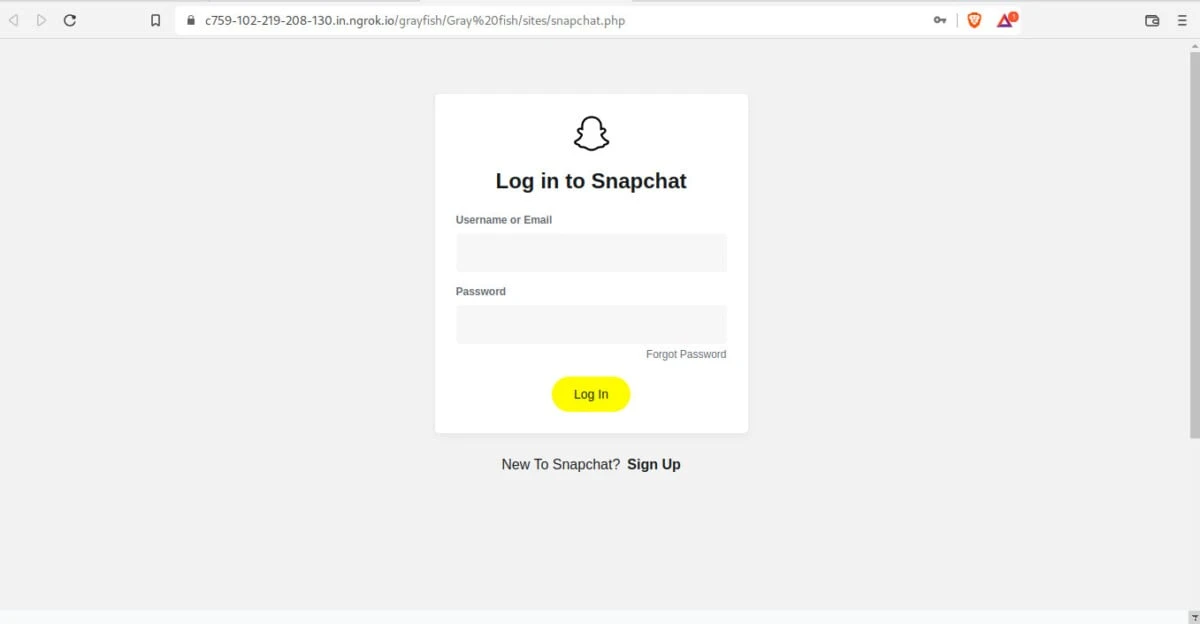
On the image above, we have phishing links which we can share over the internet depending on the site you want to phish passwords for. Since we are doing Snapchat phishing, we will share the respective phishing link with the victim. We can also use an URL shortening service to avoid raising alarms. Applying social engineering tactics will ensure the success of phishing. Below is the login page the victim will see once he/she clicks on the link sent to him/her.
Step-7: Seeing captured credentials
The phishing victim is required to provide Snapchat login details on the Snapchat phishing page. Once the login credentials are submitted, we can view them on grayfish administration page as shown below. The login details include; the username or email, user password and the site used to phish the details.

Conclusion
The main takeaway from the Snapchat phishing guide is that we all need to be better at spotting and avoiding fake websites. Over the years, phishing continues to be a major threat around the world. Many people are still falling victim to phishing methods that have been used over a long period of time. Protecting yourself from phishing attacks is an individual responsibility.s
The only way to protect yourself from Snapchat phishing is to only log in to Snapchat using the official app. If you are ever unsure if a website is really the official website, use the official app instead. This will help you avoid being tricked into sending your information.

![Snapchat Phishing using Grayfish [100% Working]](/snapchat-phishing/snapchat_phishing-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)