The other day I noticed this specific message on the console of Virtual Box VM installed with Ubuntu 22.04
RETBleed: WARNING: Spectre v2 mitigation leaves CPU vulnerable to RETBleed attacks, data leaks possible!As you can see on my VM console:
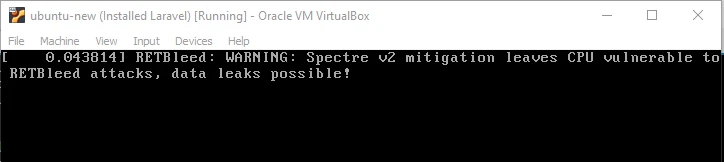
So let's understand why we are getting this WARNING message and how to mitigate or solve this issue so we don't get any such message as obviously who wants data leak right?
What is RETBleed?
RETBleed is a security vulnerability that affects certain Intel and AMD CPUs, exploiting speculative execution similarly to other side-channel attacks like Spectre and Meltdown. RETBleed specifically targets the return stack buffer (RSB), which is used to predict return addresses in speculative execution. The vulnerability allows attackers to potentially read sensitive data from memory that should not be accessible, leading to information disclosure.
- RETBleed has been assigned specific CVE (Common Vulnerabilities and Exposures) identifiers which provide official details and severity assessments of the vulnerability.
- CVE-2022-29900: NIST CVE-2022-29900
- CVE-2022-29901: NIST CVE-2022-29901
Why we get "RETBleed: WARNING: Spectre v2 mitigation leaves CPU vulnerable to RETBleed attacks, data leaks possible!" ?
The error message we are seeing, suggests that while our system may have mitigations in place for Spectre v2 (another speculative execution vulnerability), these measures do not sufficiently protect against a more specific and potentially harmful variant known as RETBleed.
- Spectre v2: This is part of a broader set of vulnerabilities known as speculative execution side-channel vulnerabilities, which affect many modern microprocessors. Spectre v2 involves branch target injection, where an attacker could potentially trick error-free programs into leaking their secrets by exploiting the way processors execute instructions out of order for speed.
- RETBleed: RETBleed is a specific type of speculative execution vulnerability that exploits the return stack buffer (RSB). The RSB is used by processors to predict return addresses when functions return. RETBleed can manipulate this prediction process to force the CPU to execute speculatively in an attacker-controlled direction, potentially exposing sensitive data through side-channel methods.
Mitigation Steps
1. Disabling RETBleed Mitigations
You can explicitly set retbleed=off which disables mitigations for the
RETBleed vulnerability. Disabling RETBleed mitigations may remove
warning messages what we are seeing during system startup and improve
performance, but it does not necessarily mean the system is secure
against the attack; it simply means the system is not actively
mitigating it.
2. Spectre V2 Mitigations
You can set spectre_v2=retpoline,force which actively mitigates
Spectre V2 vulnerabilities by ensuring that all vulnerable speculative
execution paths use retpolines, a safer method of handling speculative
branches.
While retpoline is an effective mitigation, it can have performance impacts, particularly on older CPUs or in specific workload scenarios. The degree of impact can vary, so performance testing is advisable if this is a concern. You can refer some of our other articles to learn more about CPU, Processors, Threads etc and how to improve performance of servers in production environment:
- CPU, processors, core, threads - Explained in layman's terms
- Shell script to check top memory & cpu consuming process in Linux
- Sysctl Configuration for High Performance Servers
If your system operates in a controlled environment where the risk of
attack is low (e.g., no execution of untrusted code, strong network
security), you might consider lowering the security settings by setting
spectre_v2=off to disable the mitigation.
3. Update GRUB Configuration File
You can update your GRUB configuration to mitigate these vulnerabilities and/or disable the RETBleed Warning message which we are getting. Open the GRUB configuration file using root user or with a user having sudo access:
sudo nano /etc/default/grubLook out for the line starting with GRUB_CMDLINE_LINUX_DEFAULT and
append the values I have explained in above sections. For example to
follow the recommended settings:
GRUB_CMDLINE_LINUX_DEFAULT="quiet splash retbleed=off spectre_v2=retpoline,force"When you modify GRUB settings like this, it's important to apply the changes and reboot your system:
sudo update-grub
sudo reboot
During reboot look out for similar error message on the console:

Now we are not getting that message any more.
We can also check dmesg or
journalctl logs for any helpful
information, such as we see below:
deepak@deepak-VirtualBox:~$ sudo dmesg | grep -i spectre
[ 0.042941] Spectre V1 : Mitigation: usercopy/swapgs barriers and __user pointer sanitization
[ 0.042943] Spectre V2 : Mitigation: Retpolines
[ 0.042944] Spectre V2 : Spectre v2 / SpectreRSB mitigation: Filling RSB on context switch
[ 0.042945] Spectre V2 : Spectre v2 / SpectreRSB : Filling RSB on VMEXIT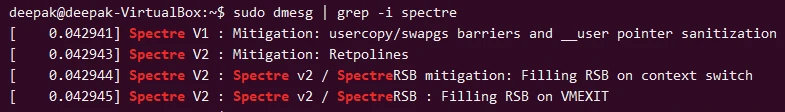
Let's understand these:
usercopy/swapgs barriers and __user pointer sanitization: This line indicates that the kernel has enabled mitigations for Spectre V1, which primarily involve adding security barriers and sanitizing pointers used in user-space to kernel-space transitions. This mitigation helps prevent speculative execution side-channel attacks that could exploit the CPU's branch prediction capabilities to leak sensitive data from kernel memory.Retpolines: This mitigation technique is used to protect against branch target injection attacks associated with Spectre V2. Retpolines ("return trampolines") modify indirect branches so that speculative execution cannot reach sensitive or dangerous areas, effectively neutralizing this type of attack.Spectre v2 / SpectreRSB mitigation: Filling RSB on context switch: This mitigation deals with the Return Stack Buffer (RSB), a structure used by the CPU to predict return addresses. The mitigation ensures that the RSB is filled (with presumably safe data) during context switches, which helps prevent speculative execution attacks that could exploit the RSB.Spectre v2 / SpectreRSB : Filling RSB on VMEXIT: Similar to the previous, this mitigation specifically ensures that the RSB is filled when exiting a virtual machine (VMEXIT). This is particularly relevant in environments like ours (running in VirtualBox) where multiple virtual machines may be managed on the same physical hardware.
So in Summary the mitigations listed in our dmesg output show that our
system has active protections against the known Spectre vulnerabilities,
which are tailored to prevent potential data leaks through speculative
execution pathways.
You can also perform vulnerability scan on a regular basis to keep your system free from any kind of known vulnerabilities.




![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)