Hello Learners, in this article we will learn the different tools used for Subdomain Enumeration of a Web Application Pentest. The Subdomain Enumeration process has evolved a lot in recent years and finding subdomains manually will take forever , thankfully we don't have to since we can use the tools below to easily enumerate the subdomains.
How do Subdomain Enumeration Tools work ?
There are 5 methods which most of the Subdomain Enumeration tools use:
- Google Dorks
- Brute Forcing
- Third party services
- SSL/TLS Certificates
- DNS Zone Transfers
Method-1: Google Dorks
Search Engines like Google and Bing support various operators to make search Queries which are known as Google Dorks.
Site:google.com
This will return the full list of Google Indexed Subdomains , This list basically comes from a Googlebot crawl. This is very useful for finding subdomains which are not protected by the robots.txt configuration.
Bing also supports some operators just like Google , for example the site operator.
Site:yahoo.com
Method-2: Brute Forcing
Some subdomain enumeration tools use brute-force and recursive brute-force most of the time with a good wordlist.
So , you can just grab some snacks and the scanners will test all the words in the wordlist to see which subdomains are alive. It’s not very fast but it’s actually the most accurate.
Some tools which use this method are : Amass , SubBrute , Puredns and Fierce.
Method-3: Third party services
There are a lot of third party services which collects massive DNS data , so these subdomain enumeration tools can add their API’s as sources and the tools will find the subdomains from each of the service.
Some of the third party services are : VirusTotal , CloudFlare, WaybackMachine .
Method-4: SSL Certificates
SSL/TLS Certificates contain information about domain names . subdomain names and email addresses. This practically makes them a treasure for all the hackers.
The best way to look up certificates of a domain is using the below 2 URLs
Method-5: DNS Zone Transfer
DNS Zone Transfer is a process through which a DNS Server passes a copy of a part of it’s DNS database to another server. The portion which got replicated is known as zone.This technique only works when the DNS zone is not protected from AXFR requests. Most of the servers are fixed with type of request but still its a method being used by the subdomain enumeration tools till date.
With that in mind , let's get started to learn the best tools for Subdomain-Enumeration.
Top 5Subdomain Enumeration Tools
1. Amass
Amass is an intelligent subdomain-enumeration tool used for Subdomain enumeration and information gathering. Amass, an open source tool, finds subdomains through DNS Enumeration , Network mapping , Certificates and Archives.There are various modules inbuilt in Amass which do the work starting from Gathering information to displaying the results in graphs.
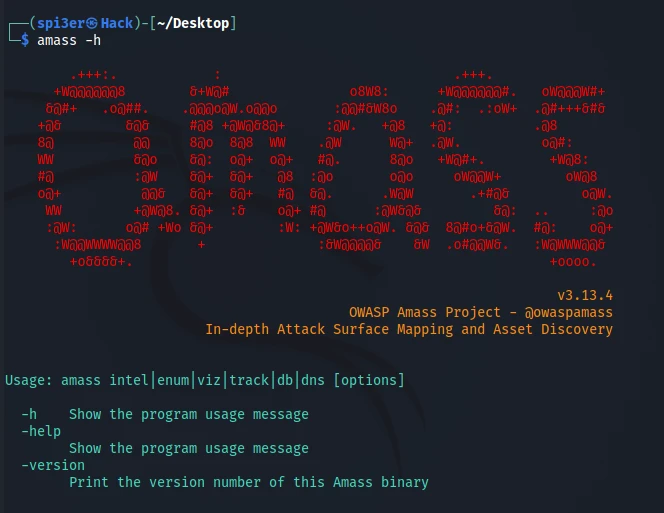
1.1 Amass Core Modules
amass intel - Gathering Information
amass enum - DNS Enumeration and mapping
amass viz - Visual results
amass track - Track differences between outputs
amass db - Stores all the found results and display the results in various formats
1.2 Installation of Amass
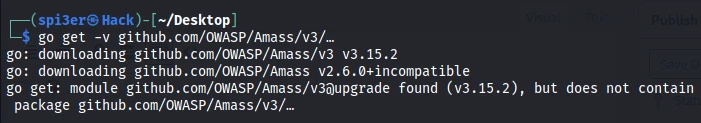
OWASP Amass can be installed on Linux OS by the following command :
go get -v github.com/OWASP/Amass/v3/…
For Mac OS,
brew tap caffix/amass
brew install amass
For Kali,
sudo apt install amass
Check whether amass is properly installed or not
amass -h
amass -version
1.3 Amass Usage
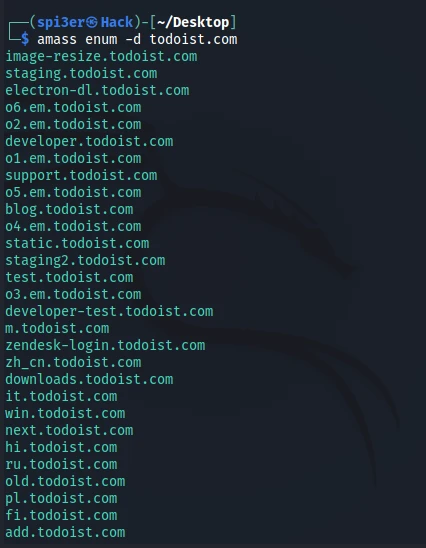
1. Basic command to enumerate the target:
amass enum -d <URL>
2. Mention the ports to scan while enumeration
amass enum -d <URL> -p 443,80,8080
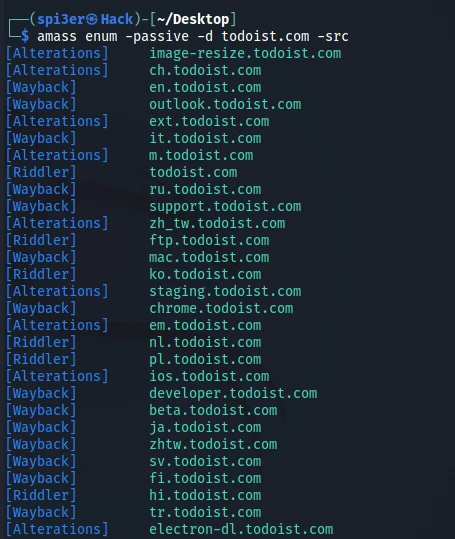
3. Passive Recon
amass enum -passive -d <URL> -src
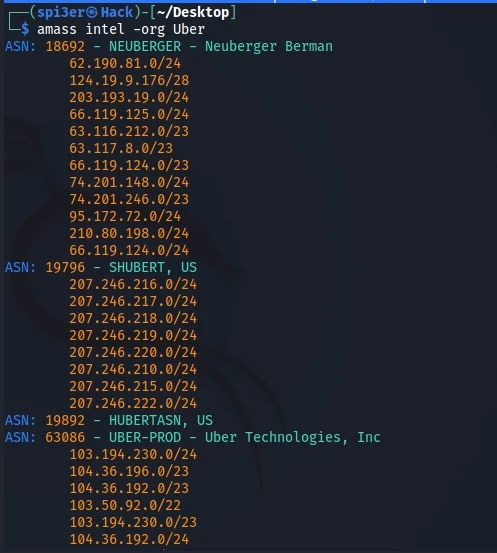
4. Search based on ASN
amass intel -asn <ASN ID’s>
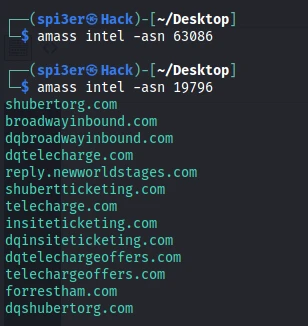
5.Find ASN ID’s through Organisation name
amass intel -org ‘Org Name’
2. Assetfinder
Assetfinder is one of the fastest subdomain enumeration tools available in the market . It's an open source tool written in Go by Tomnomnom which uses the following resources to find subdomains.
- crt.sh
- certspotter
- hackertarget
- threatcrowd
- wayback machine
- dns.bufferover.run
- virustotal
- Findsubdomains
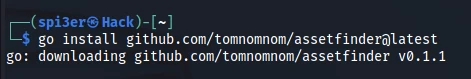
2.1 Installing Assetfinder
1.Check if Go-lang is installed. If it isn’t installed then make sure to install it.
go --version
2.You can download Assetfinder by running the following command:
go install github.com/tomnomnom/assetfinder@latest
3.You can also install Assetfinder by downloading the binaries directly from the following link
https://github.com/tomnomnom/assetfinder/releases
4.Check if assetfinder runs fine on your system
assetfinder --help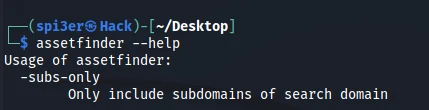
2.2 Assetfinder Usage
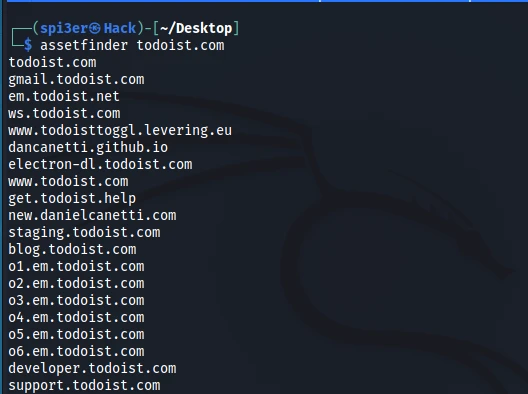
1.Find domains and subdomains of a specific domain
assetfinder todoist.com
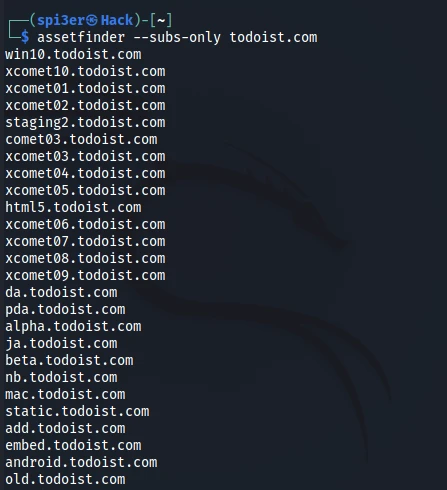
2.Find only the subdomains of a domain
assetfinder –subs-only todoist.com
3. Subfinder
Subfinder is an open source subdomain enumeration tool that finds subdomains using passive reconnaissance. Subfinder uses a simple modular architecture and is optimised for speed. It purely built for Passive reconnaissance and it does that very well.
The following resources are used to find the subdomains:
- Binaryedge
- C99
- Certspotter
- Chingz
- Censys
- Chaos
- DnsDB
- Fofa
- Github
- Intelx
- PassiveTotal
- Robtex
- Shodan
- Security trails
- Spyse
- Virustotal
- Threatbook
- Zoomeye
3.1 Installation of Subfinder
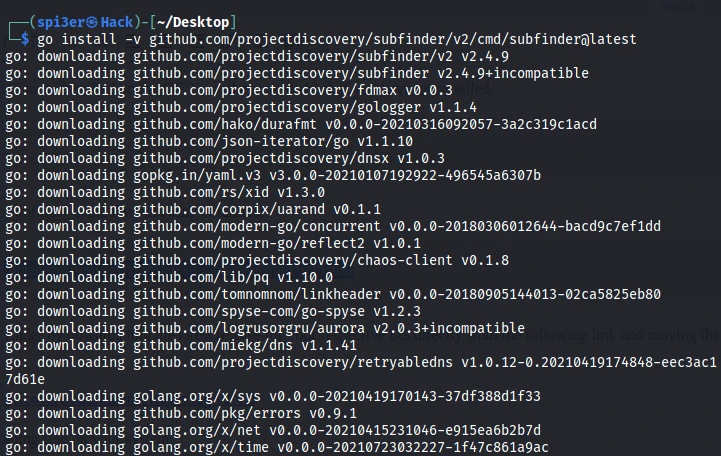
1.Subfinder requires go 1.17 to be installed on the OS. So make sure to check if you have go installed.
go --version
2.You can then download Subfinder using the following command :
go install -v github.com/projectdiscovery/subfinder/v2/cmd/subfinder@latest
3.You can also install Subfinder by downloading the latest release for your respective OS directly from the following link and moving the release to your path:
https://github.com/projectdiscovery/subfinder/releases/tag/v2.4.9
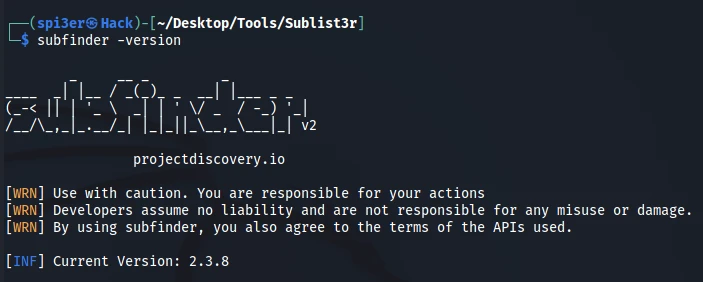
4.Check if subfinder is running fine on your system.
subfinder -version
3.3 Subfinder Usage
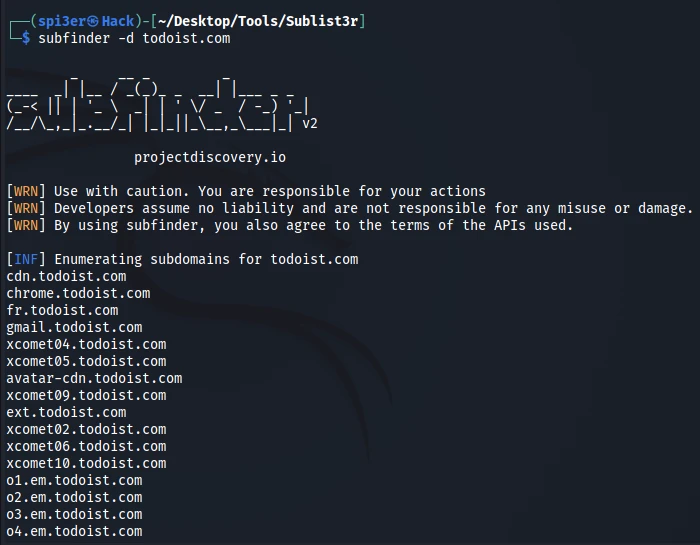
1.Find subdomains of a target domain
subfinder -d todoist.com
2.To store the output in a file
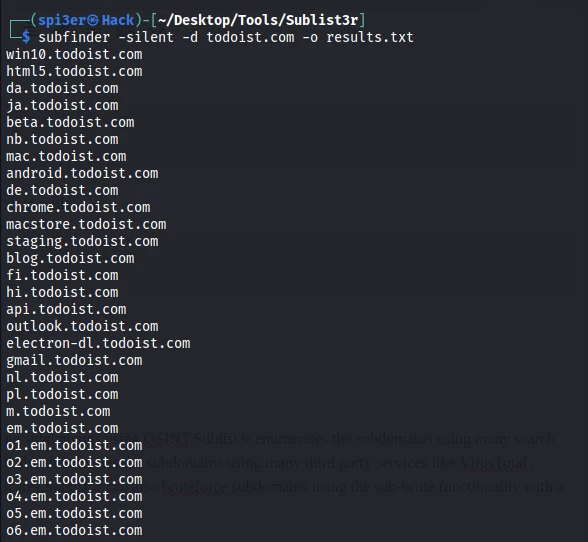
subfinder -d todoist.com -o results.txt
3.Shows only subdomains silently and saves the result in a file
subfinder -silent -d todoist.com -o results.txt
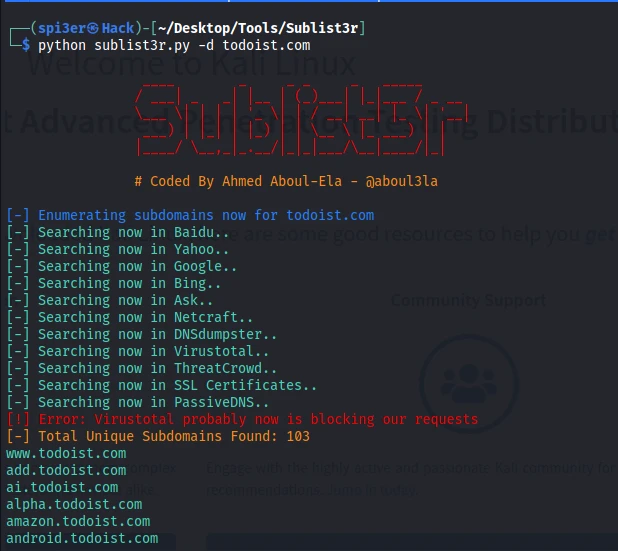
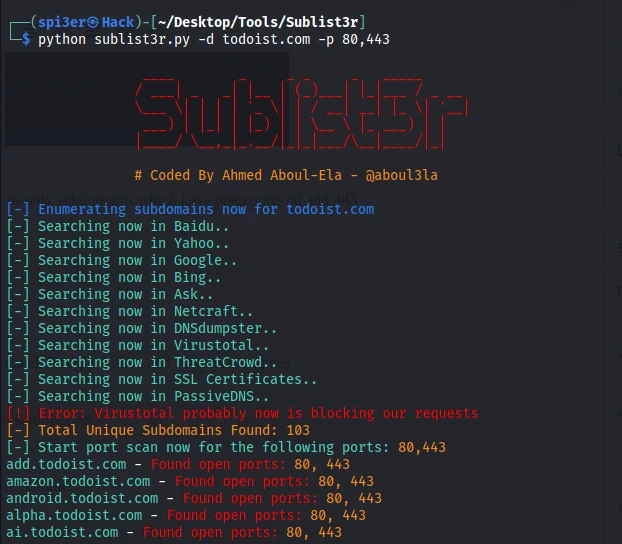
4. Sublist3r
Sublist3r is a python based tool designed to enumerate subdomains using OSINT.Sublist3r enumerates the subdomains using many search engines like Google , Bing , Yahoo, Baidu and Ask.It also enumerates the subdomains using many third party services like VirusTotal , PassiveDNS , Netcraft , DNSDumpster , SSL Certificates.Sublist3r can also bruteforce subdomains using the sub-brute functionality with a good wordlist.
4.1 Installing Sublist3r
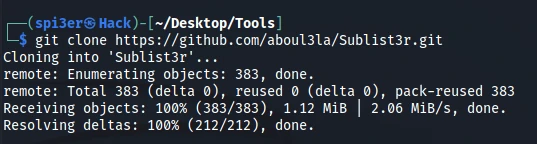
1. First git clone the directory by the following command
git clone https://github.com/aboul3la/Sublist3r.git
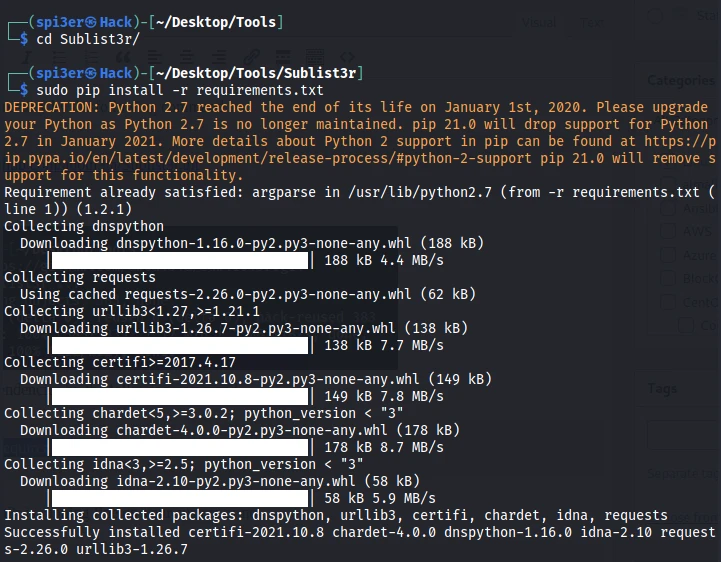
2. Next install the dependencies by the following command
sudo pip install -r requirements.txt
3. Now check if Sublist3r is running fine on your system or not
python sublist3r.py -h
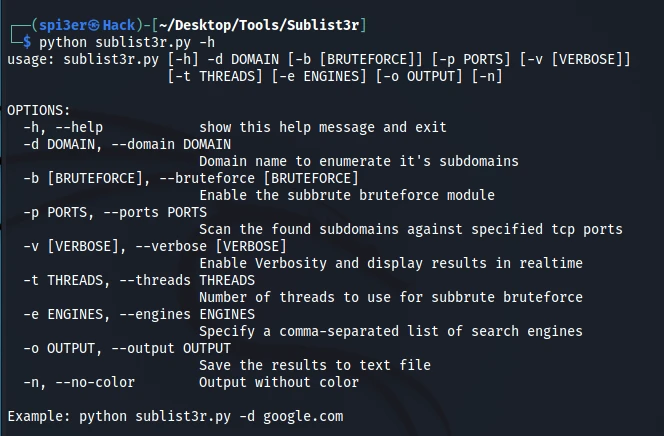
4.2 Sublist3r Usage
1. Enumerate subdomains of a specific domain
python sublist3r.py -d example.com
2. Enumerate subdomains of specific domain and show only subdomains which have open ports 80 and 443
python sublist3r.py -d example.com -p 80,443
3. To enumerate subdomains and use specific engines such Google, Yahoo and Virustotal engines
python sublist3r.py -e google,yahoo,virustotal -d example.com
4. To enumerate subdomains and enable the bruteforce module
python sublist3r.py -b -d example.com
5. PureDns
Puredns is a subdomain brute forcing tool that improves massdns to accurately handle wildcard subdomains and DNS poisoning. It’s easy to use and can be integrated into workflows, it ensures the results obtained by public resolvers are clean.
Features:
- Resolve thousands of DNS queries per second using massdns and a list of public DNS resolvers
- Bruteforce subdomains using a wordlist and a root domain
- Clean wildcards and detect wildcard roots using the minimal number of queries to ensure precise results
- Validate that the results are free of DNS poisoning by running against a list of known, trusted resolvers
5.1 Installing PureDns
1. First, Puredns requires massdns binary to be present on the system. So make sure that massdns is installed. You can check if massdns is installed or not by the following command
massdns -h

2. If massdns is not installed , execute the following commands
git clone https://github.com/blechschmidt/massdns.git
cd massdns
make
sudo make install
3. After you have verified that massdns is installed, execute the following command
go install github.com/d3mondev/puredns/v2@latest
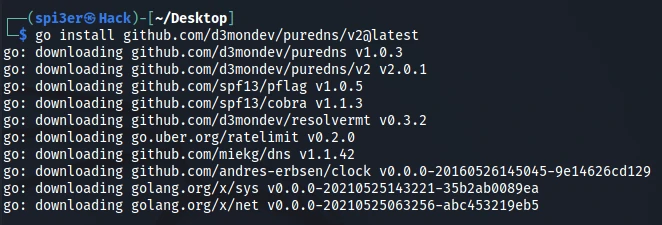
4. Verify if puredns is working fine or not by the following command
puredns --help
5.2 Puredns Usage
1. Bruteforce subdomains using wordlist file
puredns -r DNS.txt bruteforce wordlist.txt domain.com
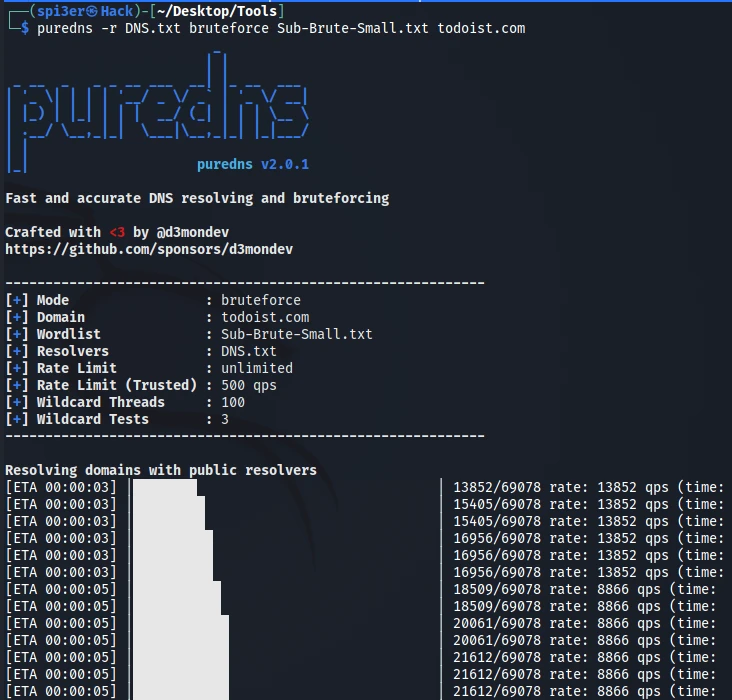
Note: wordlist.txt contains all the words for bruteforcing subdomains, wordlists can be found on SecLists Github.
2. Resolving list of domains one per line
puredns -r DNS.txt resolve domains.txt
Fast and accurate DNS resolving and bruteforcing
Crafted with <3 by @d3mondev
https://github.com/sponsors/d3mondev
------------------------------------------------------------
[+] Mode : resolve
[+] File : domains.txt
[+] Resolvers : DNS.txt
[+] Rate Limit : unlimited
[+] Rate Limit (Trusted) : 500 qps
[+] Wildcard Threads : 100
[+] Wildcard Tests : 3
------------------------------------------------------------
Resolving domains with public resolvers
[ETA 00:00:00] |██████████████████████████████████████| 13/13 rate: 13 qps (time: 00:0[ETA 00:00:00] |██████████████████████████████████████| 13/13 rate: 13 qps (time: 00:0[ETA 00:00:00] |██████████████████████████████████████| 13/13 rate: 13 qps (time: 00:0[ETA 00:00:00] |██████████████████████████████████████| 13/13 rate: 13 qps (time: 00:00:00)
Detecting wildcard root subdomains
[ETA 00:00:00] |██████████████████████████████████████| 7/7 queries: 0 (time: 00:00:00)
Validating domains against trusted resolvers
[ETA 00:00:00] |██████████████████████████████████████| 7/7 rate: 7 qps (time: 00:00:0[ETA 00:00:00] |██████████████████████████████████████| 7/7 rate: 7 qps (time: 00:00:0[ETA 00:00:00] |██████████████████████████████████████| 7/7 rate: 7 qps (time: 00:00:00)
Found 7 valid domains:
shubertorg.com
shubertticketing.com
telechargeoffers.com
forrestham.com
insiteticketing.com
telecharge.com
broadwayinbound.com
-r parameter needs to be supplied a DNS resolvers file.
3. Saving the results to files
puredns -r DNS.txt resolve domains.txt -w results.txt
Fast and accurate DNS resolving and bruteforcing
Crafted with <3 by @d3mondev
https://github.com/sponsors/d3mondev
------------------------------------------------------------
[+] Mode : resolve
[+] File : domains.txt
[+] Resolvers : DNS.txt
[+] Rate Limit : unlimited
[+] Rate Limit (Trusted) : 500 qps
[+] Wildcard Threads : 100
[+] Wildcard Tests : 3
[+] Write Domains : results.txt
------------------------------------------------------------
Resolving domains with public resolvers
[ETA 00:00:00] |██████████████████████████████████████| 13/12 rate: 13 qps (time: 00:00:00[ETA 00:00:00] |██████████████████████████████████████| 13/12 rate: 13 qps (time: 00:00:00[ETA 00:00:00] |██████████████████████████████████████| 13/12 rate: 13 qps (time: 00:00:00[ETA 00:00:00] |██████████████████████████████████████| 13/12 rate: 13 qps (time: 00:00:00)
Detecting wildcard root subdomains
[ETA 00:00:00] |██████████████████████████████████████| 7/7 queries: 0 (time: 00:00:00)
Validating domains against trusted resolvers
[ETA 00:00:00] |██████████████████████████████████████| 7/7 rate: 7 qps (time: 00:00:00)
Found 7 valid domains:
shubertorg.com
shubertticketing.com
broadwayinbound.com
telecharge.com
forrestham.com
telechargeoffers.com
insiteticketing.com
ls
DNS.txt domains.txt results.txt
Summary
In this post , we have learnt the top 5 tools used for Subdomain Enumeration in Web application Pentesting. All the tools in this post are very essential for a web application pentest and I would advise to at least use 3 tools combined for a Web Pentest. If you are just getting started with Security , then please checkout our in-depth articles on Ethical Hacking. If you encounter issues in any of the commands above, please let us know in the comments below.

![Top 5 Subdomain Enumeration Tools [Web Application Pentest]](/subdomain-enumeration-tools/Subdomain-_Enumeration_tools-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)