Many of the websites on the internet are still prone to a web cache deception attack. In this kind of attack, a bad actor will “fool” a webserver to serve information that he/she is not allowed to access. For example, on a simple eCommerce website, we have two types of users, the customers, and the administrator. The user can only view orders relating to his/her account. He is also restricted from viewing some of the pages found on the website. On a web cache deception attack, the user is able to access these restricted pages.
Checking all the links manually can be a very tedious and tiring job for a penetration tester. In this guide, I will be showing you how to automate the checking of vulnerable links using the burp suite.
Requirements
- Have a burp suite installed (The community edition can be used ).
- Have a vulnerable website to try the attack on(There are many free vulnerable web apps on the internet that can be used for this test i.e. OWASP Juice Shop, Damn Vulnerable Web Application, and the Web Goat among other many web apps ). For this guide, we will use the OWASP Juice Shop.
Burpsuite
We will first start by installing burpsuite on our system. To install burpsuite on Linux, we download the burpsuite installer and give it permission to execute.
cd ~/Downloads
chmod +x burpsuite_community_linuxv2022_8_4.sh
We can start the installation.
./burpsuite_community_linux_v2022_8_4.sh
An installation panel will appear to help you with the installation and the configuration. While installing, burpsuite will also check if the requirements required to run are met.
Autorize
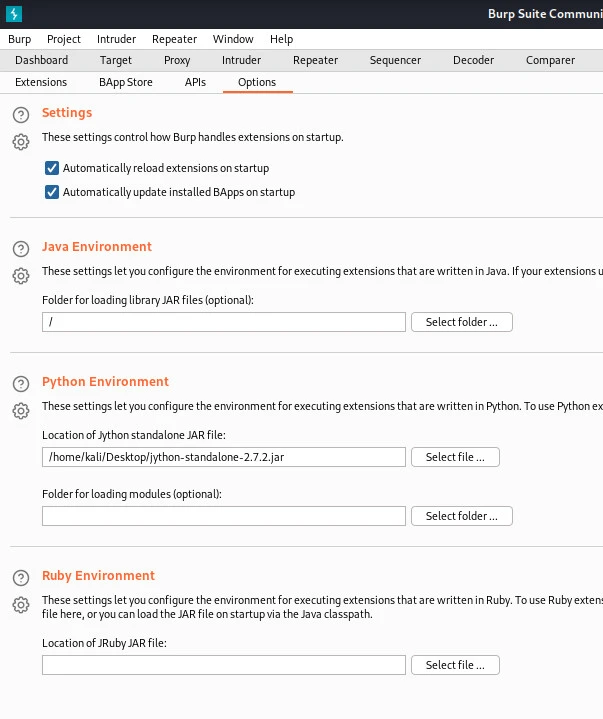
When launching the web cache deceptive attack using burpsuite, an extension known as autorize is required. This is the extension that we will be using to automate the link-checking task. For autorize extension to work, we first need to configure a python environment that burpsuite will use. Navigate to the Jython downloads pageto download Jython standalone.
To configure the python environment on burpsuite, we will navigate to the “Extender” tab and select the location of our Jython standalone file as shown in the image below.
After the configuration, we can install Autorize. Still, on the extender tab, we navigate to the BAppStore tab. On this tab, you can be able to install extensions used on burpsuite for various website tests. On the tab, we will search for autorize and install it in burpsuite as shown below.
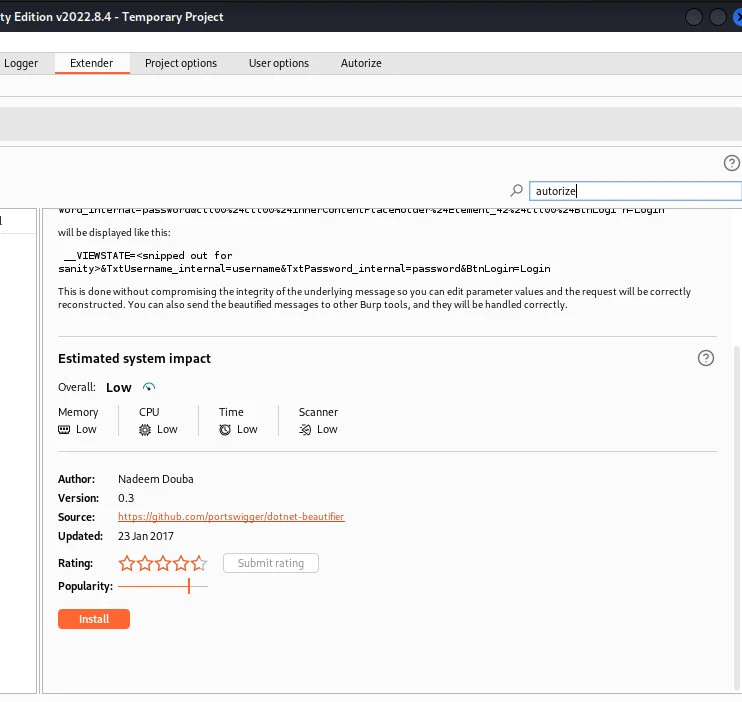
After the installation is complete, you can see another tab for autorize has been added.
We can now run our target website.
installing and setting up OWASP juice-shop
For the purpose of this guide, we will be testing the OWASP juice-shop. We will be running the dockerized OWASP juice-shop for this attack. The first step is to install docker and pull the dockerized OWASP juice-shop.
Run
docker pull bkimminich/juice-shop
The next step will be running the dockerized juice-shop.
Run
docker run --rm -p 3000:3000 bkimminich/juice-shop
The running instance of juice-shop can now be accessed on 0.0.0.0:3000 via any browser.
Web cache deception attack **** ****
Ensure everything is up and configured ready for web cache deception attack(make sure your vulnerable web app is running[In this guide we are using OWASP Juice-Shop], and make sure burpsuite is up and proxy settings properly configured. We can do the proxy configuration by using the burpsuite’s inbuilt browser).
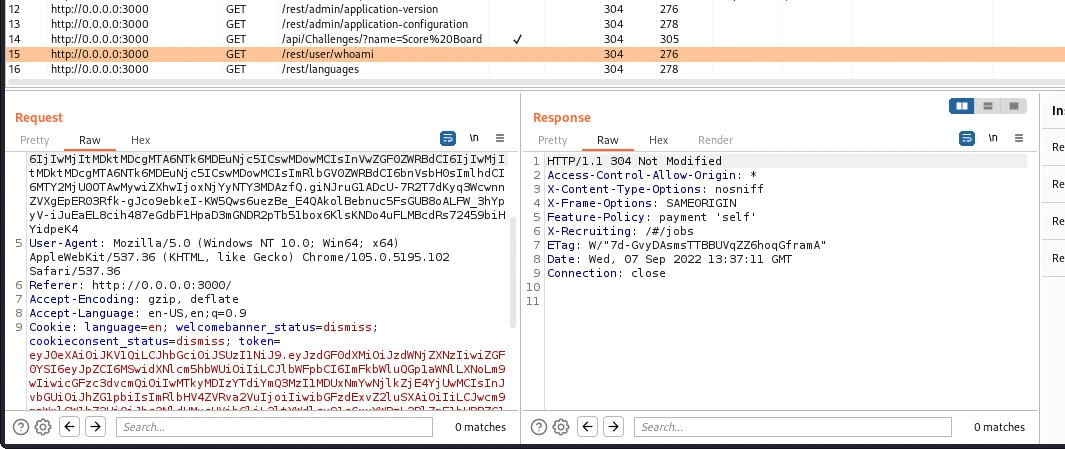
Capturing low-level user cookies
Capturing the cookies from a session where the client browsing the web application has low-level privileges is the first step of launching a web cache deception attack. Using the browser proxied to burpsuite, we navigate to access the web application. We can try navigating to various pages found on the web app. On burpsuite we can be able to see various requests made to the web application as shown in the image below.
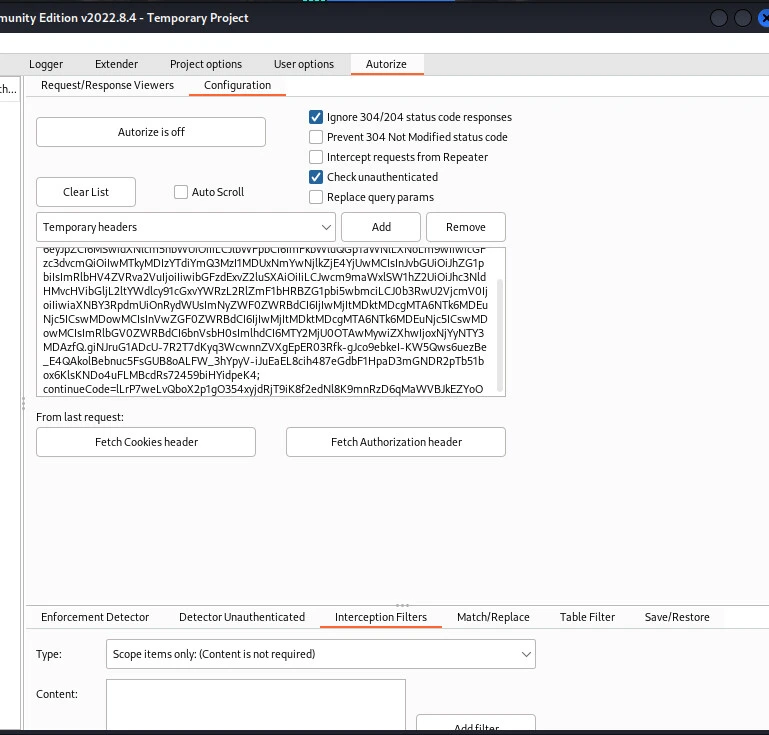
Adding the captured headers and cookies to autorize
After we have the low privilege user cookies and authorization headers, we can now navigate to autorize to add them. On the autorize tab, we have a text box with a title temporary headers. This is where we will be adding the cookies and headers. The process is automated we just have to click the fetch headers button below as shown in the image.
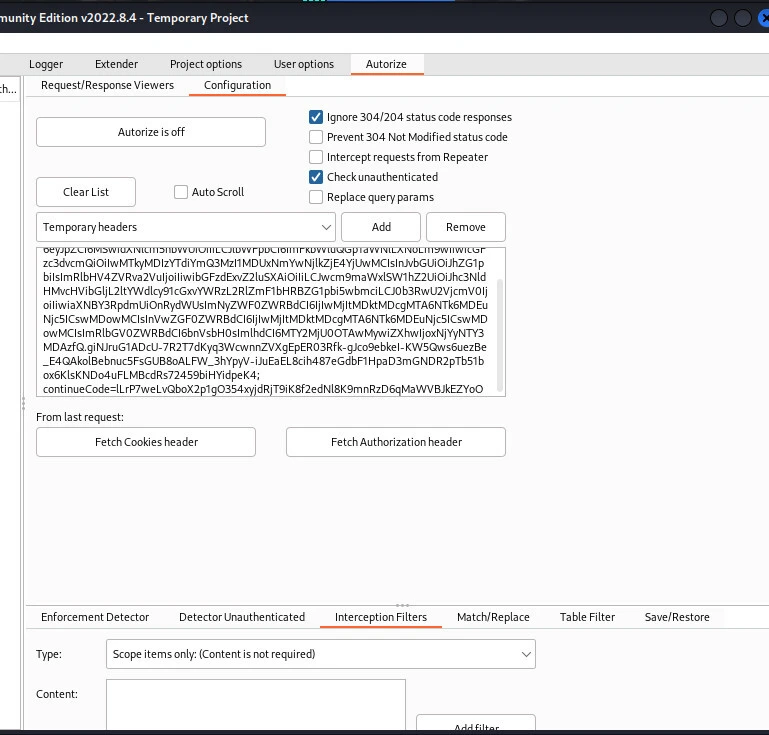
On the interception filter, make sure you add the “Scope items only” filter before launching a web cache deception attack. You can also choose to check the unauthenticated which is highly recommended since the webpage can be accessed by a user with no account only that he will be limited. Finally, we turn on the autorize extension by clicking the "autorize is off button" shown in the image below.
We can now go back to our web application and log in as high privilege user and navigate around the pages found on the website.
Checking results from autorize
On autorize tab, we can see the links which have been bypassed using autorize in the image below. Autorize works to repeat requests similar to those made on the web application using a high privilege user account but now using a low privilege user cookie. This is similar to a low-privilege user testing those links manually one by one. The main function of autorize is to automate the task of checking of these links.

Conclusion
In the above guide were able to launch a web cache deception attack test against a target website. Autorize extension has been used to automate the process of checking the links hence lesser time is used compared to manually checking each link. Autorize extension is useful, especially when used for bug bounty hunting. All the tools used to test for this vulnerability are freely available on the internet. Many websites on the internet are still vulnerable to web cache deception attack.

![Automated web cache deception attack [Tutorial]](/web-cache-deception-attack/web-cache-800w.webp)



![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_a379947ab424c826.webp)

![How to build Windows Remote Access Trojan? [SOLVED]](/windows-remote-access-trojan/windows-rat_hu_d3b8841c62382181.webp)
![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![APKHunt: Android App Pentesting [Step-by-Step]](/apkhunt-android-app-pentesting/apkhunt_hu_bbbe3c633e38f7fc.webp)
![Hack Android Remotely with Ghost Framework [Step-by-Step]](/hack-android-using-ghost-framework/hack_android_remotely_hu_cec3651da0aba4c1.webp)